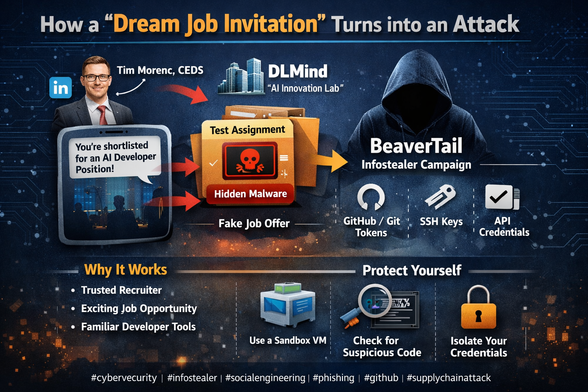
📢 Lazarus Group cache un loader malveillant dans des Git hooks pour cibler les développeurs
📝 ## 🕵️ Contexte
Publié le 6 mai 2026 par l'équipe OpenSourceMalware, cet article documente une évolution tactique de la...
📖 cyberveille : https://cyberveille.ch/posts/2026-05-08-lazarus-group-cache-un-loader-malveillant-dans-des-git-hooks-pour-cibler-les-developpeurs/
🌐 source : https://opensourcemalware.com/blog/dprk-git-hooks-malware
#BeaverTail #Contagious_Interview #Cyberveille
Lazarus Group cache un loader malveillant dans des Git hooks pour cibler les développeurs
🕵️ Contexte Publié le 6 mai 2026 par l’équipe OpenSourceMalware, cet article documente une évolution tactique de la campagne Contagious Interview / TaskJacker attribuée au groupe nord-coréen Lazarus Group (DPRK). La source est un blog de threat intelligence communautaire spécialisé dans les menaces open source. 🔄 Évolution de la technique Les opérateurs ont abandonné leurs vecteurs habituels (.vscode/tasks.json, scripts postinstall dans package.json, faux fichiers .woff2) au profit de Git hooks malveillants placés dans .githooks/pre-commit. Le hook se déclenche automatiquement lorsque la victime tente de committer du code, soit exactement au moment où le faux recruteur lui demande de “corriger un bug et committer”.