#OpenSource used to mean trusting skilled developers to build and maintain good #software so others did not need to learn every language, tool, or best practice themselves.
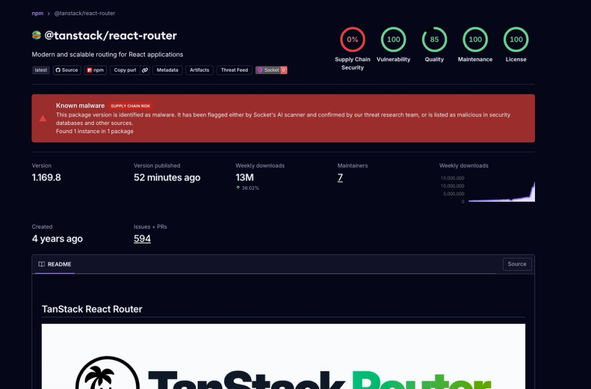
Now, #SupplyChainAttack and #AISlop have made many projects harder to trust.
Too much software is rushed, poorly understood, or built for hype instead of quality.
#Developers now spend more time checking code, #dependencies, and #maintainers instead of simply building software.
#AI was supposed to reduce cognitive load😒