Wenn die Dinger wirklich so sicher sind, wie beschworen, dann sehe ich den Nutzen in so Sachen wie Signatur und Verschlüsselung von Emails oder Dokumenten, an die man ja eh erst dran kommt, wenn das OS nach meiner MANUELLEN Eingabe eines Authentifizierungsfaktors gebootet ist und die Partitionen, die Benutzer und damit auch der Zugang zum Mail-Client und den Dokumenten freigegeben werden. Aber ansonsten?
##openSUSE Tumbleweed now uses systemd-boot as default for NEW installations! Better# FDE integration with #TPM2 / #FIDO2, simpler boot management via BLS. Existing systems stay on GRUB..#Linux https://linuxiac.com/opensuse-tumbleweed-switches-fresh-installs-to-systemd-boot/
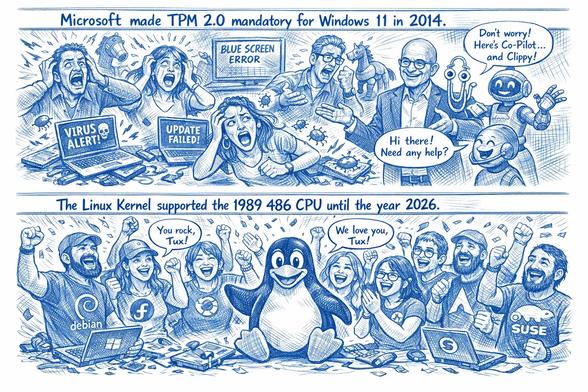
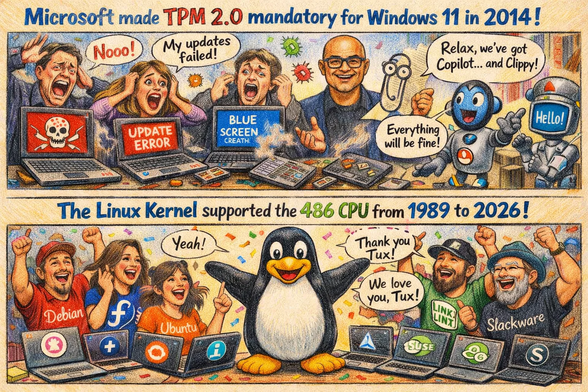
#meme #microsoft #difference #linux #486 #cpu #intel #support #update #windows #win11 #windows11 #endof10 #computer #laptop #notebook #tux #foss #floss #software #tpm #tpm2 #malware #virus #bluescreen #cybersecurity #hardware #copilot #clippy #security #economy #bigtech #freedom #fail #opensource #freeSoftware #kernel #user #fans #customers
#meme #microsoft #difference #linux #486 #cpu #intel #support #update #windows #win11 #windows11 #endof10 #computer #laptop #notebook #tux #foss #floss #software #tpm #tpm2 #malware #virus #bluescreen #cybersecurity #hardware #copilot #clippy #security #economy #bigtech #freedom #fail #opensource #freeSoftware #kernel #user #fans #customers
#openSUSE is dropping pcr-oracle in Full Disk Encryption #FDE. systemd-pcrlock now handles #TPM2 policy, fixing rollback attacks and simplifying maintenance. Migration is just two commands! 🔒🐧 Find out more. #Linux https://news.opensuse.org/2026/03/11/dropping-pcr-oracle/
Talking about #TPM2 again at a new venue #scale23x
https://www.socallinuxexpo.org/scale/23x/presentations/enhancing-tpm-security-linux-kernel
I don't think they record but I promise to do a blog post really soon about how to use the exported null name to verify the #TPM in your booted OS is secure.
@lug_nuernberg Great Meme 🫶 #TPM2 was a child once - for a better understanding, may I add this great animation to your thread? I think it's worth viewing ❤️
https://youtu.be/mLoIcdIu_Kk?si=YULJHV9WXf56U_OZ
#trustedcomputing #tcpa