Have you ever been locked-out of your own account "for your protection"? 🤦
🔗 https://tech.michaelaltfield.net/2026/02/03/single-site-browser-firejail-proxychains/
This guide 👆 shows how to setup a Persistent, Sandboxed, Single-Site-Browser using #firejail and #proxychains to minimize the risk of Evil-Corp effectively issuing a #DOS attack against you (due to false positives)
Persistent, Sandboxed, Single-Site Browser (firejail and proxychains) - Michael Altfield's Tech Blog
Or how to avoid getting locked-out of another Google Account This guide will describe how to setup a persistent browser (for Evil Corp) that’s isolated in a sandbox (with firejail) and forced to use a SOCKS5 proxy to retain a static IP address (using proxychains) Have you ever been locked out of your own account, and then got an email for your service provider annoyingly letting you know that they’ve “blocked a login attempt — for your protection?“ There’s countless reports of frustrated users who have permanently lost access to their own gmail accounts because of Google’s faulty “fraud protection” systems that locked the account owner out of their own account, due to false-positives. Problem Especially the past 10 years, large corporations have been using machine learning anomaly detection systems on their login pages. Unfortunately, sometimes this is (ab)used to have priority over credential authentication challenges. Even if you enter your username, password, and 2FA credentials correctly on the very first login attempt, you may get locked out of your own account because you “look different” Even if you enter your username, password, and 2FA credentials correctly on the very first login attempt, you may get locked . . . → Read More: Persistent, Sandboxed, Single-Site Browser (firejail and proxychains)
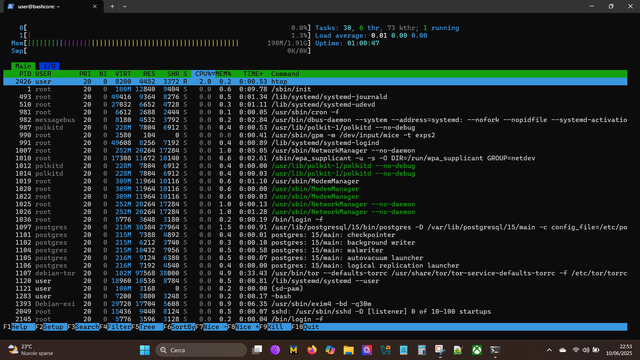
Built a custom Buildroot distro for #Raspberry Pi 4 running:
Linux 6.12 PREEMPT_RT, Wi‑Fi, #NordVPN, #Tor + #Proxychains, #macchanger, #nftables, #nmap, #netcat, #watchdog.
A real‑time, stealth, weapon‑grade network appliance.
Minimal. Fast. Untraceable. Mine 👊🏻
#Linux #Buildroot #RaspberryPi #PREEMPTRT #FOSS #Privacy #Networking
Update: after rebooting Firefox and repeating the same tests, no more DNS leaks appeared. It was likely caused by cached connections or temporary files rather than ProxyChains4 or Tor itself. Still, it’s a good reminder to always test with a clean browser profile when experimenting with chained proxies.
🖥️💡 Turn an old PC into a Tor-routed home VPS with #BashCore live USB. No install, no VPN, no AnonSurf.
🔒 Safe, private, CLI-only. 🌐 Not directly exposed to the web. 🛠️
Just run:
sudo apt install openssh-server
Edit proxychains4.conf, SSH in, and you're in.
Browse the net anonymously, test tools, study networking, all under your control 🫵
#linux #privacy #infosec #bash #tor #proxychains #debian #vps #cli #opensource #minimalism
[Перевод] Мастер-класс по обходу WAF: Использование SQLMap с Proxychains и Tamper-скриптами против Cloudflare и…
Практическое руководство по изучению и тестированию техник обхода WAF с помощью продвинутых настроек SQLMap и proxychains. Введение В современном быстро меняющемся мире кибербезопасности веб-фаерволы (WAF) играют важнейшую роль в защите сайтов от вредоносных воздействий, таких как SQL-инъекции. Однако и злоумышленники, и этичные хакеры постоянно ищут новые методы для тестирования и обхода таких мер защиты. В этом руководстве я покажу, как использовать SQLMap, ProxyChains и tamper-скрипты для проверки и оценки эффективности WAF. Вы узнаете, как настроить эти инструменты и проводить сканирование, соблюдая этические стандарты и лучшие практики.
https://habr.com/ru/articles/906860/
#sqlmap #proxychains #хакинг #взлом #кибербезопасность #багхантинг #waf
Мастер-класс по обходу WAF: Использование SQLMap с Proxychains и Tamper-скриптами против Cloudflare и…
Практическое руководство по изучению и тестированию техник обхода WAF с помощью продвинутых настроек SQLMap и proxychains. Введение В современном быстро меняющемся мире кибербезопасности веб-фаерволы...
One of things I suffer on #FreeBSD using an #Iranian connection, is that all package mirrors are terribly slow.
Currently, as a workaround, I'm using #proxychains with the FreeBSD package manager. Unfortunately, setting a SOCKS5 #proxy through pkg.conf does not seem to work.
Using a proxy or a #VPN is not a big deal for a typical developer based in #Iran. But it's the first time I have to change IP(and route) to properly use an OS's first class package manager.
Maybe I could host a mirror for Iranians if FreeBSD stays as my main OS. Tho I don't see much point with only myself being the FreeBSD user in here.
@nemo I somewhat blindly voted #Proxychains despite abandoning it years ago. The recent #Torsocks version breaks Postfix and never worked on Java apps. So I should probably retry proxychains. When I tried proxychains many years ago it worked on nothing. But I should try it again.
My top choice is actually to use #Firejail with the --net option pointing to a Tor middlebox (which is not a separate box but just a config that yields a virtual eth0 replacement device).