How I Sandbox My AI Agents
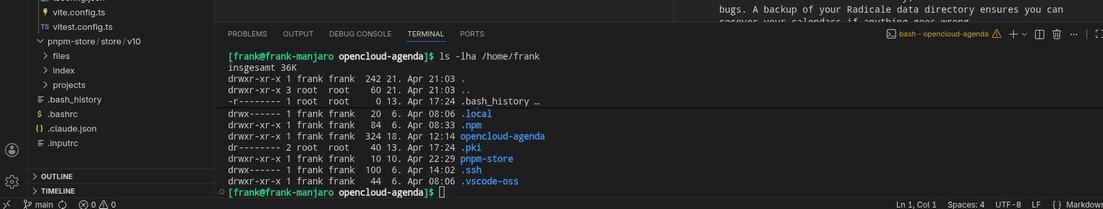
작성자는 오픈소스 AI 코딩 에이전트인 Opencode를 Firejail을 이용해 커널 레벨에서 샌드박싱하여 시스템 접근을 제한하는 방법을 소개합니다. 이 방식으로 Opencode가 SSH 키 등 민감한 파일에 접근하지 못하도록 안전하게 격리하며, 프로젝트 디렉토리만 화이트리스트로 허용해 사용합니다. 향후 로컬 LLM 모델과 인터넷 차단 환경에서 Opencode를 활용하는 확장도 계획 중입니다. 이 접근법은 AI 에이전트 사용 시 보안과 프라이버시를 강화하는 실용적 사례로 참고할 만합니다.
https://blog.fidelramos.net/software/how-i-sandbox-ai-agents

How I Sandbox my AI Agents
I've been using Opencode as my AI coding agent. Very unlike me, I don't have a long list of reasons why I picked it among the many alternatives. I just wanted to get started with an agent system that checked my main requirements: Must be fully open-source. Popular, meaning it's …