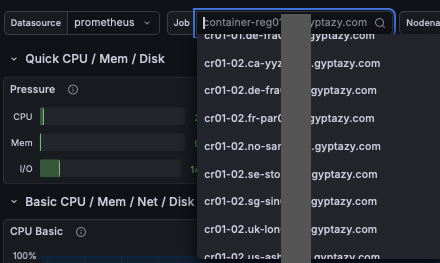
Every network vendor has an "AI-powered" story right now. Most of them are 10% of the actual solution. I broke down what the other 90% looks like after watching Aviz Networks demo their AI NOC platform at Network Field Day. #NFD #Networking #NetOps #AI
https://packitforwarding.com/index.php/2026/04/30/ai-more-than-a-bolt-on-solution-for-networking/

AI, More Than a Bolt On Solution for Networking -
The post critiques the marketing use of "AI-powered" in network tools, highlighting the gap between flashy demos and real enterprise needs. It emphasizes the importance of multi-source data integration, on-premises hosting, and robust role-based access. Genuine AI solutions must address complexities beyond simple Q&A interfaces to be effective in real environments.


 decio
decio