Verivox warnt: Versteckte Kosten - Miet-Router machen Internet teuer
Bequem, einsteigerfreundlich, aber extrem teuer: Die Router-Miete beim Internetanbieter erweist sich oft als finanzielle Fehlentscheidung. Schon nach rund zwei Jahren übersteigen die monatlichen Raten den Kaufpreis für ein neues Endgerät.
Start9 RISC-V Router features SpacemiT K1 SoC, runs StartWRT OpenWrt fork (Crowdfunding)

Start9 RISC-V Router features SpacemiT K1 SoC, runs StartWRT OpenWrt fork (Crowdfunding)
Start9's "RISC-V Router" is powered by a SpacemiT K1 octa-core RISC-V processor paired with 4GB RAM and 16GB eMMC flash, and offers dual GbE networking, as well as an AsiaRF AW7915-NP1 WiFi 6 4T4R module enabling up to 2401 Mbps combined data link. It's not exactly a high-end router, but Start9 claims it is the "most open router on the market" thanks to its RISC-V processor, OpenSBI open-source boot stack, and StartWrt operating system, a fork of OpenWrt. Start9 router specifications: SoC – SpacemiT K1 CPU – 8-core X60 RISC-V processor with single-core performance equivalent to about 1.3x the performance of an Arm Cortex-A55 GPU – Imagination IMG BXE-2-32 with support for OpenCL 3.0, OpenGL ES3.2, Vulkan 1.2 VPU – H.265, H.264, VP9, VP8 4K encoding/encoding NPU – 2.0 TOPS AI accelerator System Memory – 4GB LPDDR4 Storage 16GB eMMC flash MicroSD card slot Networking 2x Gigabit Ethernet RJ45 ports
SOHO router attack by APT28
Few weeks ago, one particular large scale cyber-attack hit the mainstream news everywhere. Russian cyber actor APT28 attacked SOHO routers and managed to compromise some credentials through that. The attack itself was carried in multiple phases and was quite interesting. Let's take a look at those individual steps, what happened, how it worked and what
Das System läuft jetzt seit gut 1,5 Jahren extrem zuverlässig, lässt sich per Snapshot sichern, ist extrem flexibel konfigurier- und erweiterbar…
Und wenn i h die Hardware wechseln will brauche ich auch nur die virtuelle Machine zu übertragen und behalte alle Konfigurationen…
#OpenWRT #Proxmox #Linux #Router
RISC-V Router
#HackerNews #RISC-V #Router #open-source #hardware #networking #tech #innovation
Router-Falle beim Internetanschluss: Kunden zahlen bis zu 28 Prozent mehr
Wieder Zero-Day Angriffe gegen Palo Alto Firewall
Und täglich grüßt das Murmeltier. Wieder ein amerikanischer Hersteller von proprietärer Netzwerktechnik, dessen Zero-Day "Sicherheitslücke" (Hintertür) von wahrscheinlich staatlich unterstützten Hackern angegriffen wird. Der Netzwerk-Ausrüster Palo Alto ist und ja schon öfter begegnet. Die CISA hat die Lücke CVE-2026-0300 bereits in den KEV Katalog aufgenommen. Normalerweise bedeutet das eine Anweisung an die Behörden, Updates gegen die betreffende Lücke innerhalb kürzester Frist einzuspielen. Nur dass im vorliegenden
#Allgemein #Empfehlung #Hintergrund #Warnung #0day #closedsource #cybercrime #exploits #firewall #foss #hersteller #hintertr #opensource #router #sicherheit #spionage #UnplugTrump #usa #vorbeugen
𝗖𝗵𝗶:
Lightweight, idiomatic and composable router for building Go HTTP services .
Broadcom BCM67142, BCM67192, and BCM68565 chips target low-cost WiFi 8 10 Gbps fiber access points
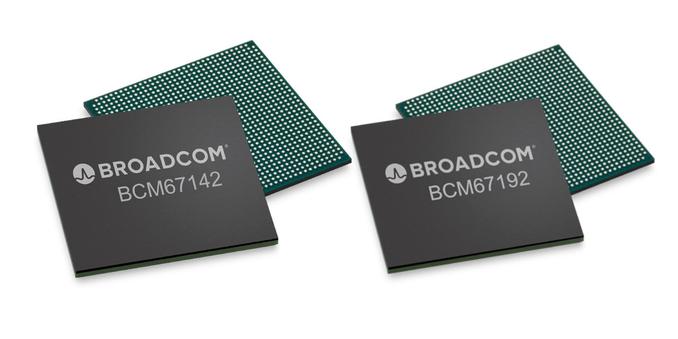
Broadcom BCM67142, BCM67192, and BCM68565 chips target low-cost WiFi 8 10 Gbps fiber access points
Broadcom has recently announced the BCM67142 and BCM67192 WiFi 8 (802.11bn) chips for low-cost residential access points, and the BCM68565 PON Gateway SoC with 10 Gbps Fiber support to enable complete broadband access points. The announcement follows the launch of the company's flagship residential (BCM6718) and enterprise (BCM43840/BCM43820) platforms last year, with the new chips aiming to provide value-focused residential Wi-Fi 8 and 10G PON gateway solutions. Broadcom BCM67142 and BCM67192 WiFi 8 access point chips BCM67142/BCM67192 specifications: Wi-Fi Standards IEEE 802.11bn (Wi-Fi 8) compliant IEEE 802.11be (Wi-Fi 7) compliant IEEE 802.11 a/b/g/n/ac/ax Spatial Streams BCM67142 - Dual-Radio: 3x3 (2.4 GHz) + 4x4 (5 GHz). Total 7 streams BCM67192 - Dual-Radio: 4x4 (2.4 GHz) + 4x4 (5 GHz). Total 8 streams Spectral Bands - 2.4 GHz, 5 GHz Channel Bandwidths - 20/40 MHz (2.4 GHz), 20/40/80/160 MHz (5 GHz) Highest Modulation Rate - 4096-QAM (for UHR/Wi-Fi 8 operation) Multi-Link Operation

