Два Kubernetes-кластера — одна сеть: объединяем через Mesh и межкластерный роутинг
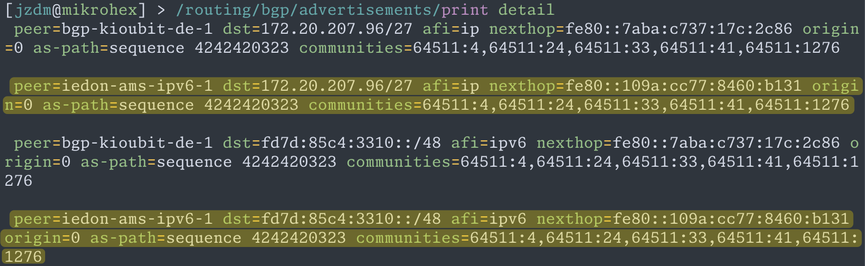
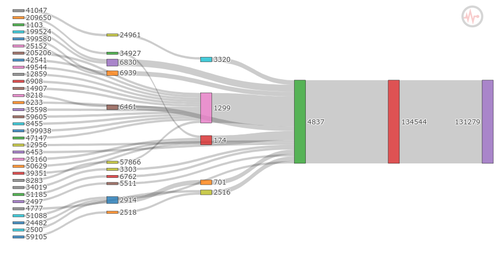
Когда Kubernetes-кластеров становится больше одного, инфраструктура начинает жить по новым правилам. Один кластер развёрнут в основном датацентре, второй — в резервной площадке. Сложности начинаются в тот момент, когда этим кластерам нужно взаимодействовать друг с другом. Сервисы в одном кластере должны обращаться к сервисам в другом, приложениям требуется нормальная маршрутизация, а инженерам хочется управлять этим без набора временных решений вроде iptables и ручных DNS-записей. В качестве сетевого слоя будем использовать Calico , а для межкластерного взаимодействия сервисов — Istio . Первый даст маршрутизацию и связность, второй — discovery, балансировку и управление трафиком на уровне приложений.
https://habr.com/ru/companies/gnivc/articles/1026994/
#calico #bgp #istio #kubernetes