От видимости сети до кибербезопасности: главный миф о сетевой телеметрии, который мешает раскрыть потенциал NetFlow
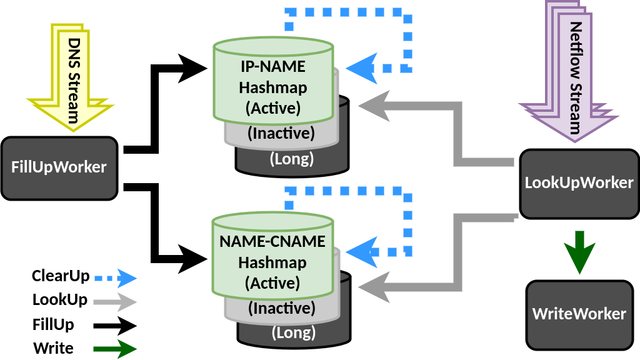
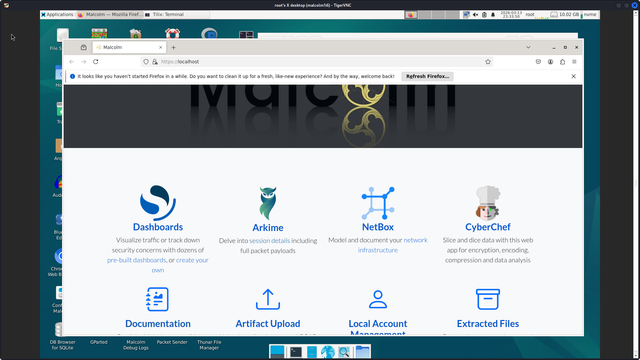
Привет, Хабр! На связи Станислав Грибанов, я руководитель продукта NDR компании «Гарда», автор блога «Кибербезопасность и продуктовая экспертиза для бизнеса» . Сегодня хочу поговорить о пользе NetFlow и сетевой телеметрии для защиты сетей от хакерских атак. Тема эта не новая, но вокруг неё до сих пор существует множество противоречий. Сетевая телеметрия часто воспринимается как артефакт из мира сетевых инженеров, а не как серьёзный инструмент информационной безопасности. Как правило, это связано с ошибочным восприятием NGIPS-систем, как аналога NTA. В этом случае основной считается функциональность сигнатурного детектирования атак, которая требует для работы только сырой трафик. При этом методы поведенческого анализа, машинного обучения и других несигнатурных техник в таких системах являются комплиментарными и не формируют ядро детектирующей логики. Из-за подобного ошибочного восприятия на российском рынке сформировалось массовое заблуждение: для поиска угроз в сетевом трафике нужен только анализ сырого сетевого трафика, а телеметрия для этого не подходит. Под катом я расскажу, как можно детектировать угрозы на основе метаданных сетевого трафика без анализа payload, в частности, сетевой телеметрии.
https://habr.com/ru/companies/garda/articles/1035666/
#ndr #nta #netflow #ipfix #ml #TI_feeds #анализ_сетевого_трафика #ngips #anomaly_detection
От видимости сети до кибербезопасности: главный миф о сетевой телеметрии, который мешает раскрыть потенциал NetFlow
Привет, Хабр! На связи Станислав Грибанов, я руководитель продуктового направления компании «Гарда», автор блога «Кибербезопасность и продуктовая экспертиза для бизнеса» . Сегодня хочу поговорить о...