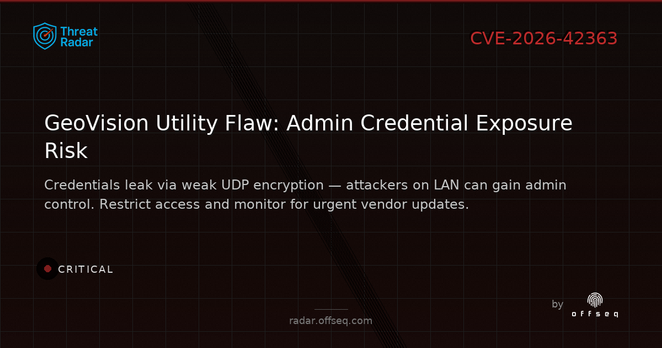
🚨CRITICAL: CVE-2026-42363 in GeoVision GV-IP Device Utility 9.0.5 exposes admin creds via UDP broadcast with weak encryption. Attackers on LAN can take full control. Limit access, avoid untrusted networks, and watch for patches. https://radar.offseq.com/threat/cve-2026-42363-cwe-656-reliance-on-security-throug-65391bf4 #OffSeq #infosec #IoTSecurity
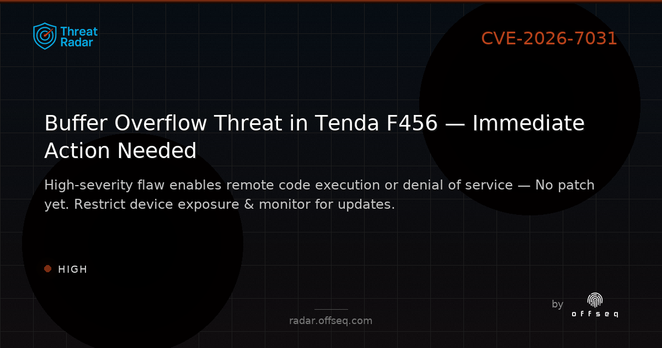
🔒 CVE-2026-7031: HIGH-severity buffer overflow in Tenda F456 (v1.0.0.5). Remote, no user interaction needed. Exploit public, no patch yet. Limit device exposure & monitor for updates. More: https://radar.offseq.com/threat/cve-2026-7031-buffer-overflow-in-tenda-f456-f28ef6c0 #OffSeq #Vulnerability #IoTSecurity #NetSec
Das #NCSC warnt mit Partnern wie #CISA und #BSI vor verdeckten Netzwerken kompromittierter Router und IoT-Geräte mit China-Bezug. Für Unternehmen ist das auch ein Compliance-Thema. #CyberSecurity #IoTSecurity
https://www.ncsc.gov.uk/news/defending-against-china-nexus-covert-networks-of-compromised-devices
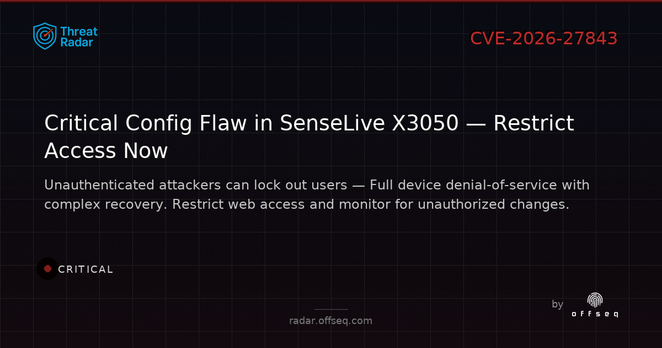
🚨 CVE-2026-27843: SenseLive X3050 (V1.523) CRITICAL vuln — missing auth lets attackers lock out users, causing full denial-of-service. No reset button; recovery needs console access. Restrict mgmt access & monitor configs. https://radar.offseq.com/threat/cve-2026-27843-cwe-306-missing-authentication-for--e4fcb515 #OffSeq #IoTSecurity #Vuln
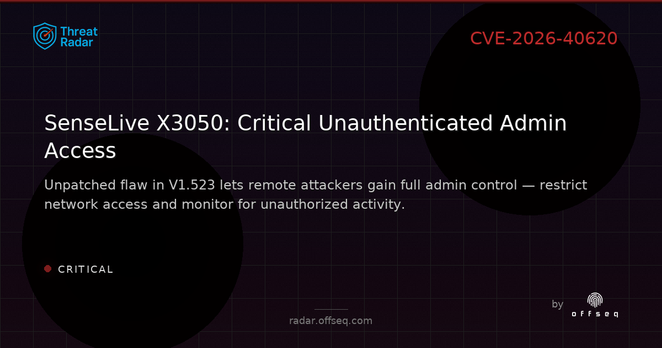
SenseLive X3050 V1.523 is at CRITICAL risk (CVE-2026-40620, CVSS 9.3): missing auth lets remote attackers gain admin access. No patch yet — restrict management access, monitor logs, and follow vendor updates. https://radar.offseq.com/threat/cve-2026-40620-cwe-306-missing-authentication-for--0af2786c #OffSeq #CVE202640620 #IoTSecurity
🔍 CVE-2026-25775: SenseLive X3050 (V1.523) critical vuln — remote firmware updates possible without auth! Patch unavailable. Restrict access & monitor for unauthorized firmware actions. https://radar.offseq.com/threat/cve-2026-25775-cwe-306-missing-authentication-for--773ccfcd #OffSeq #IoTSecurity #CVE202625775
🚨 CRITICAL: SenseLive X3050 v1.523 is vulnerable to authentication bypass (CVE-2026-40630) via alternate paths. No fix yet — restrict device network access and monitor closely. https://radar.offseq.com/threat/cve-2026-40630-cwe-288-authentication-bypass-using-b2eedf7d #OffSeq #CVE202640630 #IoTSecurity #VulnAlert
Defender for IoT is your friend. Protect OT networks from lateral movement attacks. https://aka.ms/DefenderIoT #IoTSecurity #Azure
⚠️ CVE-2026-32955: HIGH severity stack-based buffer overflow in silex SD-330AC (≤v1.42). Attackers with low privileges can execute code via redirect URLs. Restrict access & monitor devices until patch is available. https://radar.offseq.com/threat/cve-2026-32955-stack-based-buffer-overflow-in-sile-b2529213 #OffSeq #Vulnerability #IoTSecurity
⚠️ CRITICAL: CVE-2026-32956 — Heap buffer overflow in silex SD-330AC (≤v1.42) & AMC Manager. Remote code execution possible. No patch yet; restrict exposure, monitor advisories. https://radar.offseq.com/threat/cve-2026-32956-heap-based-buffer-overflow-in-silex-2da79db9 #OffSeq #IoTSecurity #CVE202632956 #Vuln