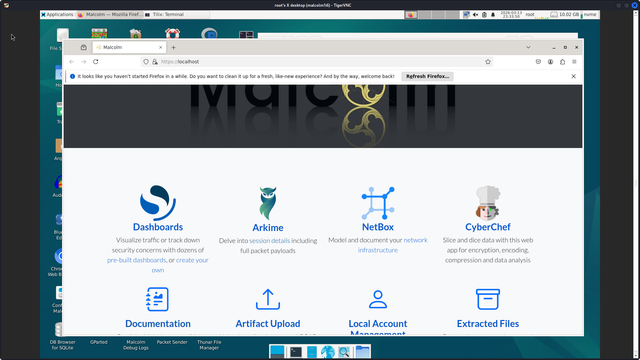
running malcom but the old malcolm - need to image and install latest - sort of dread going from debian to ubuntu but if i image i can revert easily. maybe they figured out updating, i don't want github only updates.
anyways it is a good one to offer vs say security onion - they use the same components mostly, suricata, zeek, elastic, maybe he has a live iso like last time.
i think the reason to go to ubuntu is better newer drivers, bigger dev base? as long as it works - that is my concern, avoid dependency hell and breakage.
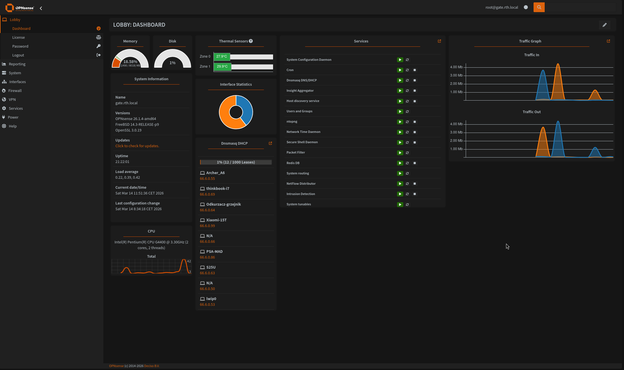
it is good with managing all the containers and space for /datastore #sigs #hashes #dpi #netflow #ntop-ng #tcp-replay #binaries #hashcat
@da_667 i may have to break into the mountains and drink a cold one
make a paid version of suri with ndpi for opnsense - plus upsells - their licensing is good , somebody may already do this? either way good idea#hashcat #ntop products #ids #opnsense
#you can't run away from your problems #you can run away from your problems
@da_667 i would say go for the standalonelib? this would be a nice switch to use when building, more info is better #ntop-ng #netflow #logs
Using nDPI as a standalone library when building Suricata is a powerful way to transform it from a traditional signature-based IDS/IPS into a smarter, more context-aware network security monitoring system. The integration addresses several key limitations of Suricata by adding a dedicated, high-performance deep packet inspection (DPI) engine .
The table below summarizes the core reasons for this integration.
Reason Explanation Key Benefits
Massively Expanded Protocol Coverage Suricata natively supports ~20 protocols, while nDPI recognizes 450+ (including Cloud, IoT, and OT protocols) . Enables visibility into a wider range of applications and potential threats that Suricata would otherwise miss .
Enhanced Threat Detection Capabilities nDPI adds behavioral analysis and risk detection to Suricata's signature-based approach . Allows detection of anomalies like encrypted traffic on standard ports, self-signed certificates, and command-and-control (C2) channels hiding in plain sight .
More Powerful and Precise Rules The plugin introduces new rule keywords: ndpi-protocol and ndpi-risk . Enables writing rules based on detected application (e.g., TLS.YouTube) or specific risk (e.g., NDPI_BINARY_APPLICATION_TRANSFER), significantly reducing false positives .
Richer Contextual Metadata Suricata's logs (EVE JSON) can be augmented with protocol and metadata identified by nDPI . Provides security analysts with deeper insights for faster threat hunting and forensic analysis without needing full packet captures .
🛠️ How to Integrate nDPI with Suricata
nDPI is integrated as a plugin that is not built into Suricata by default. You need to explicitly enable it during compilation. The process, as outlined in the official Suricata documentation, involves two main steps :
Build Suricata with nDPI Support: When configuring your Suricata build from source, you must use the --enable-ndpi flag and point to your nDPI source code.
bash
./configure --enable-ndpi --with-ndpi=/path/to/your/nDPI/source
Load the Plugin: After installation, you need to ensure Suricata loads the nDPI plugin by adding its path to the suricata.yaml configuration file.
yaml
plugins:
- /usr/lib/suricata/ndpi.so
By building Suricata with the standalone nDPI library, you are essentially giving it a "second opinion" on network traffic. nDPI handles the heavy lifting of identifying countless applications and their potential risks, which then feeds directly into Suricata's core engine for alerting and logging. This makes your network defense far more robust and intelligent.
Would you like to see more detailed examples of Suricata rules that use the ndpi-protocol and ndpi-risk keywords?
N .Top are dropping their first single album today.
엔탑(N .TOP) 'WE:DISCONNECT' HIGHLIGHT MEDELY
https://www.youtube.com/watch?v=jnQU1QFI7AY
엔탑(N.TOP) 'WE:DISCONNECT' HIGHLIGHT MEDELY
they have to get more input from stakeholders and also find out when fiber is available #network visibility #netflow #ntop-ng deb file #ndpi
New post as part of a new series on Unit Gradient Fields (UGFs): https://www.blakecourter.com/2023/05/05/what-is-offset.html
UGFs are more versatile than distance fields when applying implicit modeling to engineering applications. The new #nTop logo, for example, hints at them. As we ramp up to #cdfam23, expect frequent posts discussing the role of UGFs when engineering with implicits.
*ntopng*
High-Speed Web-based Traffic Analysis and Flow Collection
ntopng is the next generation version of the original ntop, a network traffic probe that monitors network usage. ntopng is based on libpcap/PF_RING and it has been written in a portable way in order to virtually run on every Unix platform, MacOS and on Windows as well.
ntopng – yes, it’s all lowercase – provides a intuitive, encrypted web user interface for the exploration of realtime and historical traffic information.
Main Features
Sort network traffic according to many criteria including IP address, port, Layer-7 (L7) application protocols, throughput, Autonomous Systems (ASs)
Show realtime network traffic and active hosts
Produce long-term reports for several network metrics including throughput and L7 application protocols
etc