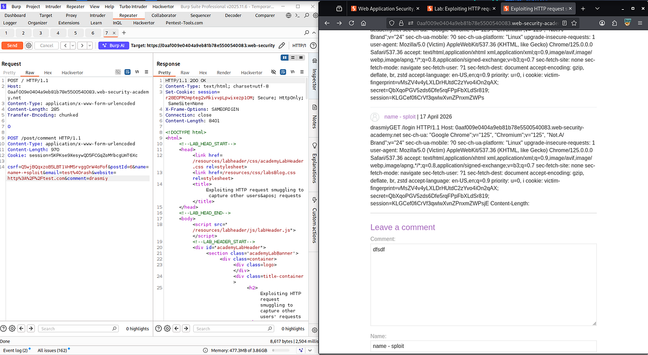
Exploiting HTTP Request Smuggling to Capture Other Users’ Requests | khan sploit | Mo Rashid
This vulnerability is an Information Disclosure through HTTP request smuggling. The application server failed to handle multiple requests concurrently, leading to the intermingling of user requests. By sending two malicious requests simultaneously—a comment post and a cookie-grabbing request—the attacker exploited this flawed handling logic, causing the server to send the response for both requests in a single response. The researcher was then able to capture the victims' cookies by observing the responses for the cookie-grabbing request. This information disclosure allowed unauthorized access to other users’ sessions. The researcher did not disclose a payout amount, but the article mentions that they reported the vulnerability to HackerOne and received recognition from Khan Academy. To remediate, implement request parsing logic that correctly handles multiple concurrent requests and separates them before processing—never trust user-controlled headers for security decisions. Key lesson: Validate and separate concurrent requests to prevent HTTP request smuggling. #BugBounty #WebSecurity #InformationDisclosure
The plaintiffs are seeking minimum damages of $1,000 per survivor from the Justice Department, as well as punitive damages 'in amounts sufficient to punish and deter' Google.
#Trending #USNews #DonaldTrump #Google
https://globalnews.ca/news/11748748/epstein-survivors-sue-us-government-google-over-epstein-files-release/
The plaintiffs are seeking minimum damages of $1,000 per survivor from the Justice Department, as well as punitive damages 'in amounts sufficient to punish and deter' Google.
#Trending #USNews #DonaldTrump #Google
https://globalnews.ca/news/11748748/epstein-survivors-sue-us-government-google-over-epstein-files-release/
Forbidden Does’t Mean Impossible — Discovering Hidden Endpoints with 403Bypasser
In this article, the researcher discovered a technique for bypassing 403 Forbidden errors and uncovering hidden endpoints. The vulnerability stemmed from a lack of proper error handling and insufficient input validation on the application's side. By using the 403Bypasser tool, the researcher sent crafted requests to test for potential bypasses. The payload contained an If-Modified-Since header with a future timestamp. If the response included a 200 OK status instead of the expected 403 Forbidden, it indicated that the endpoint was vulnerable. The researcher found that the application failed to handle invalid timestamps, allowing them to access sensitive information. This flaw could potentially lead to unauthorized data access or information disclosure. The researcher earned $1,500 for this discovery. Proper remediation involves implementing proper input validation for timestamps, as well as thorough error handling. Key lesson: Inadequate error handling and input validation can lead to information disclosure and bypassing intended access restrictions. #BugBounty #InformationDisclosure #403Bypasser #InputValidation #Cybersecurity #WebSecurity
XXE Injection Guide: Fundamentals, Payloads, and Bug Bounty Strategies
This write-up describes the XML External Entity (XXE) injection vulnerability, focusing on its fundamentals, payloads, and bug bounty strategies. The root cause is an application's failure to properly handle XML entities, allowing external data (DTD or XML entity references) to be loaded. By crafting payloads with DTD-based entities to force external file inclusions or Remote File Inclusion (RFI), the researcher discovered vulnerable applications. The mechanism involves tricking the application into parsing malicious XML entities, causing it to read and execute arbitrary files or network resources. This vulnerability can lead to serious consequences such as data breaches, information disclosure, and even Remote Code Execution (RCE). A $2,000 bounty was awarded for discovering an XXE vulnerability on a popular platform. To remediate, enforce strict XML entity handling, limit DTD processing, and consider using XML parsers with built-in protection against XXE injections. Key lesson: Always validate and sanitize user-supplied XML input to prevent XXE injections. #BugBounty #Cybersecurity #XML #XXEInjection #InformationDisclosure
#YonhapInfomax #KoreaHydroNuclearPower #InformationDisclosure #MinistryOfTheInteriorAndSafety #CustomerSatisfaction #Transparency #Economics #FinancialMarkets #Banking #Securities #Bonds #StockMarket
https://en.infomaxai.com/news/articleView.html?idxno=105845

Korea Hydro & Nuclear Power Earns Top Rating in '2025 Information Disclosure Comprehensive Assessment'
Korea Hydro & Nuclear Power Co. secured the top rating in the 2025 public institution information disclosure assessment, highlighting its commitment to transparency and improved customer satisfaction.
Clobbering DOM Attributes to Bypass HTML Filters and Trigger DOM-Based XSS
This article demonstrates a unique form of DOM-based Cross-Site Scripting (XSS) by exploiting property collisions in the Document Object Model (DOM). The application filters user comments for restricted HTML but overlooks unsafe assumptions about specific DOM properties. By intentionally clobbering an existing property (onclick), the researcher overwrites its original value with malicious code, effectively bypassing filtering mechanisms that should have removed it. Although event handlers such as onclick and onfocus were supposed to be removed, the clobber attack allowed their retention. This vulnerability can result in sensitive data exposure or account takeover. The researcher did not disclose a bounty amount, but the article serves as a valuable lesson for security researchers to scrutinize assumptions about DOM properties during sanitization. Key lesson: Carefully examine all DOM properties when implementing HTML filtering to avoid clobber attacks. #BugBounty #Cybersecurity #DOMXSS #InformationDisclosure
Here's something that wasn't on your bingo card. Secrets, like API keys were gobbled up in a huge dataset used to train most GenAI models. People leave them in GitHub, then the model absorbs the code, and bobs your uncle.
https://thehackernews.com/2025/02/12000-api-keys-and-passwords-found-in.html?m=1
#ACTIVELYEXPLOITED #DLINK #HARDWARE #INFORMATIONDISCLOSURE https://www.bleepingcomputer.com/news/security/hackers-exploit-critical-d-link-dir-859-router-flaw-to-steal-passwords/