🔴 This Server Bug Lets Hackers Own Your System
Hackers are exploiting this RIGHT NOW to write files directly onto your server as SYSTEM.
https://www.youtube.com/shorts/_0Km84P23-E
#cybersecurity #SamsungMagicINFO #CVE20247399 #pathtraversal #infosec #hacking #cve #vulnerability #threatintel #security
This Server Bug Lets Hackers Own Your System #Shorts
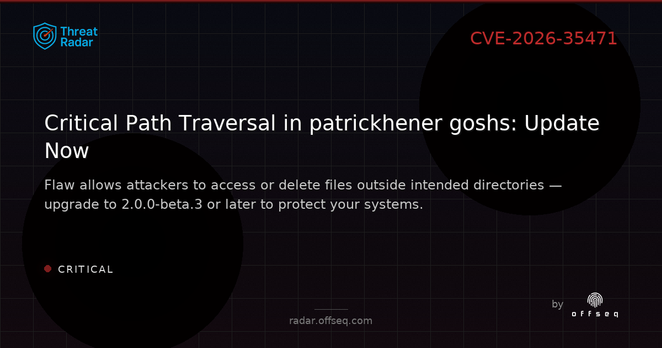
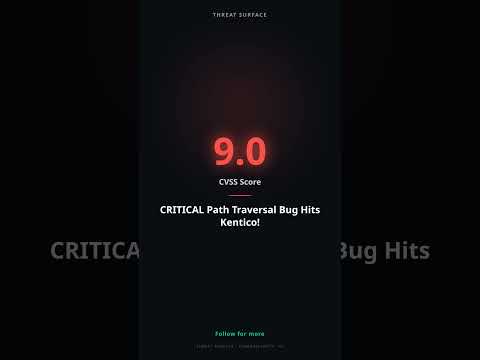
🔴 CRITICAL Path Traversal Bug Hits Kentico!
A 9.0 CVSS vulnerability just hit Kentico Xperience!
https://www.youtube.com/shorts/DKGuuh-ObSc
#cybersecurity #vulnerability #kentico #pathtraversal #infosec #cybersecurity #infosec #hacking #cve #vulnerability
CRITICAL Path Traversal Bug Hits Kentico! #Shorts
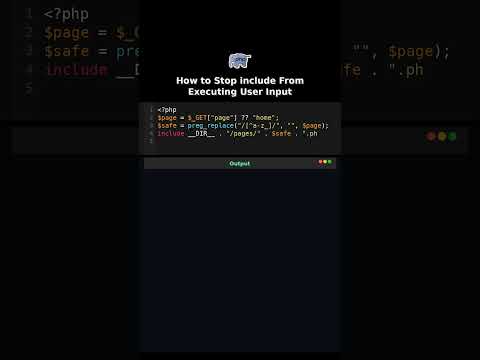
How to Stop include From Executing User Input
Including user input turns filenames into attacks.
How to Stop include From Executing User Input #lfi
How to Block Path Traversal in Uploads
Two dots can escape any upload folder.
#python #pathtraversal #security #uploads #howto #filesystem

How to Block Path Traversal in Uploads #howto
Struggling with the #Java Path API in
safePrefix(Path prefix, Path tail)
to resolve tail onto prefix or return null if the result is not a file **below** prefix. This shall prevent path traversal attacks. The code is ugly.
The tricky shit is in things like safePrefix("..", "..") where Path.normalize() does not what we might like it to do.
I would be happy about any code review I can get. (So boosts would be nice.)