Copy Fail, Dirty Frag and now Fragnesia...
Upside: if you have already ripped out esp4, esp6 and rxrpc for Dirty Frag, you already have the mitigation in place for Fragnesia.
Copy Fail, Dirty Frag and now Fragnesia...
Upside: if you have already ripped out esp4, esp6 and rxrpc for Dirty Frag, you already have the mitigation in place for Fragnesia.
🛡️ AI-Driven Cyber Attacks Now Break Defenses in Just 73 Seconds
Anthropic's Mythos AI model is breaching systems in seconds, making faster, smarter cybersecurity responses critical.
https://byte-pulse.net/article/ai-driven-cyber-attacks-now-break-defenses-in-just-73-seconds
OpenAI’s GPT-5.5 is as Good as Mythos at Finding Security Vulnerabilities
The UK’s AI Security Institute evaluated GPT-5.5’s ability to find security vulnerabilities, and found that it is comparable to Claude Myth... https://www.schneier.com/blog/archives/2026/05/openais-gpt-5-5-is-as-good-as-mythos-at-finding-security-vulnerabilities.html
The UK’s AI Security Institute evaluated GPT-5.5’s ability to find security vulnerabilities, and found that it is comparable to Claude Mythos. Note that the OpenAI model is generally available. Here is the Institute’s evaluation of Mythos. And here is an analysis of a smaller, cheaper model. It requires more scaffolding from the prompter, but it is also just as good.
Linux bitten by second severe vulnerability in as many weeks
Production-version patches are coming online and should be installed pronto.
Archive: ia: https://s.faithcollapsing.com/wai9z
#biz-&-it #exploits #linux #security #vulnerabilities
https://arstechnica.com/security/2026/05/linux-bitten-by-second-severe-vulnerability-in-as-many-weeks/
"six CVEs for serious security vulnerabilities in dnsmasq"
https://lists.thekelleys.org.uk/pipermail/dnsmasq-discuss/2026q2/018471.html
CERT is releasing six CVEs for serious security vulnerabilities in dnsmasq
https://lists.thekelleys.org.uk/pipermail/dnsmasq-discuss/2026q2/018471.html
#HackerNews #CERT #CVEs #dnsmasq #security #vulnerabilities #cybersecurity #patches
Mass npm Supply Chain Attack Hits TanStack, Mistral AI, and 170+ Packages (safedep.io)
https://safedep.io/mass-npm-supply-chain-attack-tanstack-mistral/
#security #supplychain #npm #vulnerabilities #attack #programming
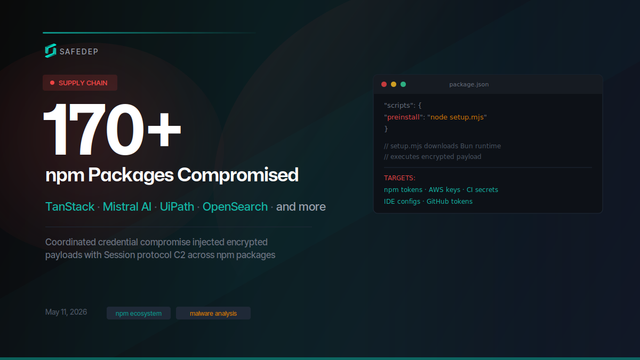
Over 400 compromised npm package versions and at least 2 PyPI packages published in a coordinated supply chain attack targeting TanStack, Mistral AI, UiPath, OpenSearch, guardrails-ai, and dozens of other packages.
Copy.Fail Linux Vulnerability
This is the worst Linux vulnerability in years.
TL;DR
copy.fail is a Linux kernel local privilege escala... https://www.schneier.com/blog/archives/2026/05/copy-fail-linux-vulnerability.html
This is the worst Linux vulnerability in years. TL;DR copy.fail is a Linux kernel local privilege escalation, not a browser or clipboard attack. Disclosed by Theori on 29 April 2026 with a working PoC. It abuses the kernel crypto API (AF_ALG sockets) plus splice() to write four bytes at a time straight into the page cache of a file the attacker does not own. The exploit works unmodified across Ubuntu, RHEL, Debian, SUSE, Amazon Linux, Fedora and most others. No race condition, no per-distro offsets. The file on disk is never modified. AIDE, Tripwire and checksum-based monitoring see nothing. ...