@downey
Warning! A lot of acronyms ahead! Welcome to Telco land...
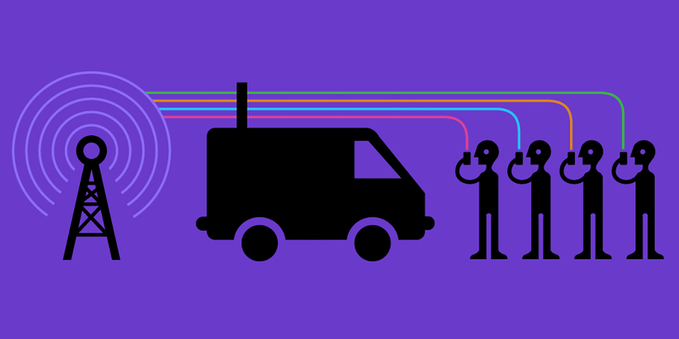
TLDR: Anyone with the "fake cellphone tower" device mentioned can track BOTH your SIMcard, AND your mobile device.
So you better leave them at home, or bring a burner1 phone with a burner1 SIM.
IMSI vs IMEI
The "#IMSI" in #IMSIcatcher is an identifying number tied to your SIM(card).
But what #IMSIcatchers can also capture is your device's #IMEI 2.
The supposed purpose of an IMEI is stated clearly in the official documentation:
"The main objective is to be able to take measures against the use of stolen equipment or against equipment of which the use in the PLMN3 can not or no longer be tolerated for technical reasons."4
Mobile device manufacturers are obligated to produce device unique IMEI's:
"The IMEI shall be unique and shall not be changed after the ME’s [Mobile Equipment] final production process. It shall resist tampering, i.e. manipulation and change, by any means (e.g. physical, electrical and software)."4
IMSIcatcher vendors state their equipment can also capture IMEIs.5 6
So, every phone in the neighborhood of IMSIcatchers in use by law enforcement, are certainly in a batch of "to be tracked".
Did I mention law enforcement (through a legal warrant, they'll need help from mobile operators) can track phones based on IMEI alone (so even if you remove the SIM)? Yes, I believe I did.
PS: a phone connecting to or connected to an IMSIcatcher, is not on the network. Not being able to reach emergency services could lead to physical harm, including death. Just saying.
1 https://ssd.eff.org/glossary/burner-phone
2 International Mobile Station Equipment Identity
3 Public Land Mobile Network: wireless communication services offered by a specific operator in a specific country.
4 https://www.3gpp.org/ftp/Specs/archive/22_series/22.016/
5 https://x-surveillance.com/imsi-stingray-device/
6 https://www.stratign.com/imsi-catcher-system/




 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉