The use of cell site simulators is still shrouded in secrecy. It’s not just the government who uses these to catch “bad guys”.
But a lot of really great research by the academic community, privacy advocates, and some of my colleagues has advanced our knowledge of how they work.
If you have an Android device, and you’re able to do so, the single most impactful thing you can do for your cellular privacy and security is to disable the “Allow 2G” setting in the mobile network settings screen (available on most devices shipped in the last couple of years). If you’re in North America it’s extremely likely there’s no legitimate 2g networks still in service from your carrier, and a downgrade to a 2g connection is a very common and easy mechanism for all sorts of privacy invading attacks.
It doesn’t come close to mitigating all risks posed by CSSs, but it’s an impactful start.
#privacy #cellular #2g #cellsitesimulators #android #imsicatcher
https://www.wired.com/story/fbi-cell-site-simulator-stingray-secrecy/



 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉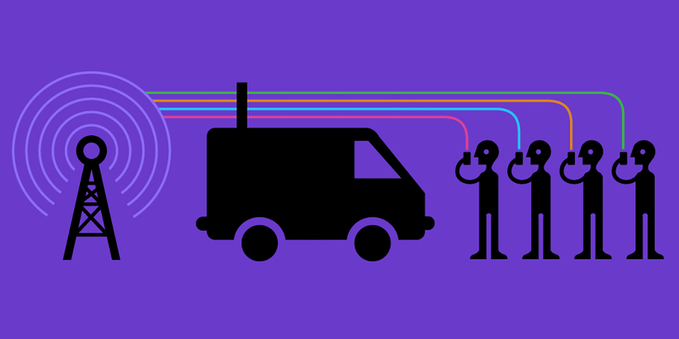


 :EA DATA. SF:
:EA DATA. SF: