Most cloud breaches trace back to simple configuration errors. Continuous audits, identity controls, and workload protections are essential to keep cloud environments secure.
☁️ Cloud Security Tools — Essential Toolkit for Modern Teams 🛡️🚀
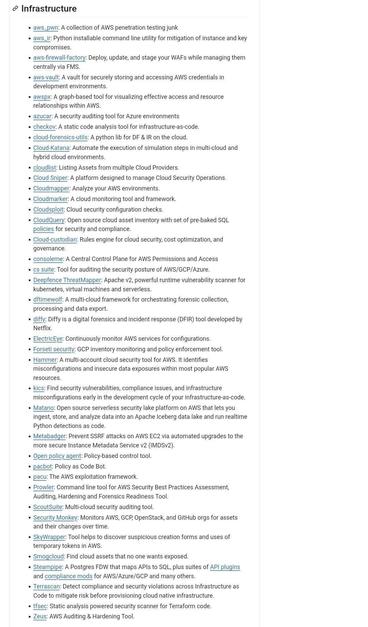
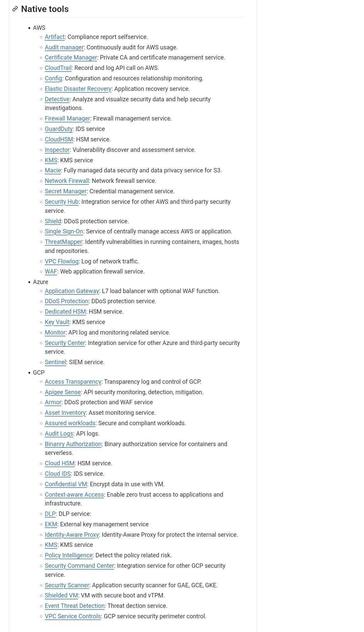
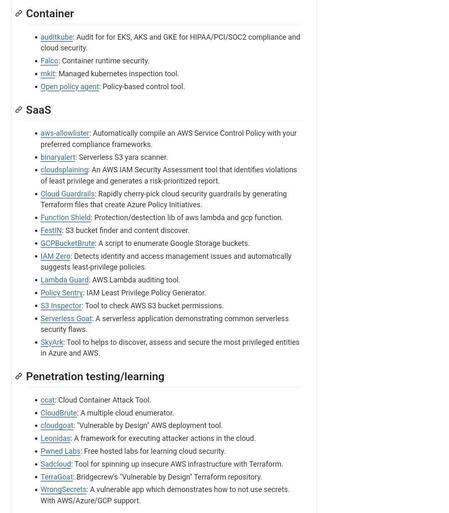
Cloud environments introduce new risks and require specialized tooling to secure workloads, configurations, and data. Use a mix of CSP-native and third-party tools to cover posture management, runtime protection, identity, and visibility. Key categories and examples: Cloud Security Posture Management (CSPM) — Prisma Cloud, Dome9, Wiz for misconfig & compliance checks 🔍; Cloud Workload Protection (CWPP) — CrowdStrike, Trend Micro, Aqua for container and VM runtime defense 🐳🛡️; Cloud Access Security Broker (CASB) — Netskope, Microsoft Defender for Cloud Apps for SaaS visibility & data control ☁️🔐; Identity & Access Management — AWS IAM/Azure AD hardening, BeyondTrust, Okta for strong auth & least privilege 🔑; Threat Detection & SIEM — Splunk, Sumo Logic, Datadog + cloud-native logging for alerting and forensics 📊; Vulnerability & Configuration Scanning — Qualys, Tenable, Trivy for images and infra-as-code scanning ⚙️; Secrets Management — HashiCorp Vault, AWS Secrets Manager for safe key handling 🔐; and Supply-chain & CI/CD security — Snyk, Checkov, GitHub Advanced Security to catch insecure deps and pipelines 🧩.
⚠️ Disclaimer:
For educational & defensive use only. Evaluate tools against your cloud provider, compliance needs, and threat model before deploying. Always test changes in staging before production. 🚫🔒
#CloudSecurity #CSPM #CWPP #IAM #DevSecOps #InfoSec #Cloud #CyberSecurity #SecurityTools #Compliance #ContainerSecurity ☁️🛡️
via SBCFireInfo 🐦
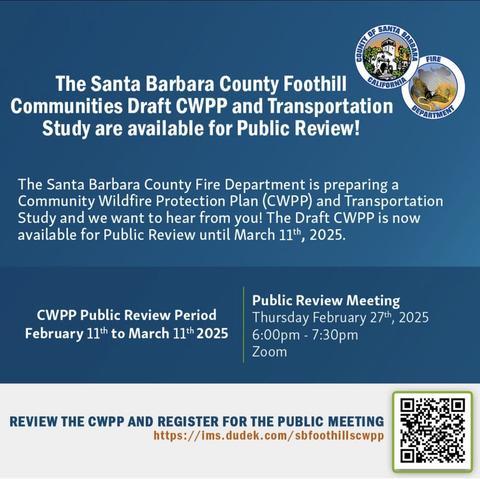
Public Input Needed: Draft CWPP & Transportation Study
The #SantaBarbara County Fire Department is seeking public input on the Community Wildfire Protection Plan (CWPP) and Transportation Study for the Santa Barbara Foothill Communities. The Draft CWPP is now available for public review until March 11, 2025.
🔹 Public Review Period: February 11 – March 11, 2025
🔹 Virtual Public Meeting: Thursday, February 27, 2025 | 6:00 – 7:30 PM | Register Here
Your feedback is crucial in shaping wildfire preparedness and community safety. Review the draft plan and register for the public meeting at: ims.dudek.com/sbfoothillscwpp
𝐌𝐚𝐩 𝐂𝐨𝐧𝐭𝐚𝐢𝐧𝐞𝐫 𝐈𝐦𝐚𝐠𝐞𝐬 𝐟𝐫𝐨𝐦 𝐂𝐨𝐝𝐞 𝐭𝐨 𝐂𝐥𝐨𝐮𝐝 𝐰𝐢𝐭𝐡 𝐃𝐞𝐟𝐞𝐧𝐝𝐞𝐫 𝐟𝐨𝐫 𝐂𝐥𝐨𝐮𝐝
When a vulnerability is identified in a container image stored in a container registry or running in a Kubernetes cluster, it can be difficult for a security practitioner to trace back to the CI/CD pipeline that first built the container image and identify a developer remediation owner.
With DevOps security capabilities in Microsoft Defender Cloud Security Posture Management (CSPM), you can map your cloud-native applications from code to cloud to easily kick off developer remediation workflows and reduce the time to remediation of vulnerabilities in your container images.
Details: https://learn.microsoft.com/en-us/azure/defender-for-cloud/container-image-mapping
#defender #cspm #CloudSecurityPostureManagement #devops #pipeline #codetocloud #container #vulnerabilities #Kubernetes #cnapp #cwpp #cloudnative #cloudsecurity #soc #microsoft #microsoftsecurity #azure #multicoud
𝐈𝐧𝐭𝐫𝐨𝐝𝐮𝐜𝐢𝐧𝐠 𝐌𝐢𝐜𝐫𝐨𝐬𝐨𝐟𝐭 𝐃𝐞𝐟𝐞𝐧𝐝𝐞𝐫 𝐟𝐨𝐫 𝐂𝐥𝐨𝐮𝐝 𝐋𝐚𝐛𝐬
Our labs project help you get ramped up with Microsoft Defender for Cloud and provide hands-on practical experience for product features, capabilities, and scenarios. The labs are divided into 3 main tracks, a beginner (level 100/200) and an advanced (level 300+) track. The labs contain several modules cover different pillars such as Cloud Security Posture Management (CSPM) to Cloud Workload Protection (CWP). To start using our labs, you will need to create Azure Trial Subscription which provides you all capabilities for 30 days – so you have to finish this lab at this point to take advantage of the free trial.
https://github.com/Azure/Microsoft-Defender-for-Cloud/tree/main/Labs
#defender #defenderforcloud #cnapp #cspm #cwp #cwpp #cloudsecurity #multicloud #azure #aws #gcp #microsoft #microsoftsecurity #soc #server #container #storage #dns #api #devops #database #api #github #arc #agentless #storageaccount #mde #vulnerability #mdvm #siem
VMware Carbon Black: 기능 및 규격
NGAV 및 EDR 활용한 정보보안 업무에 참고할 수 있도록 규격서 정리되어 있습니다.
솔루션 도입 검토에 참고하실 수 있습니다.
- https://bs.etevers.tech/books/carbon-black/page/cloud-workload-protection-platfom-cwpp
#VMware #CarbonBlack #CWPP #containersecurity #infosec #정보보안
Steps Forward: Can ‘CNAPP’ solutions truly unify cloud, on-premises best cybersecurity practices?
Byron Acohido hosts a #CNAPP conversation with #Runecast, Data Theorem, Palo Alto Networks, and #Gartner.
#CSPM #CWPP
https://www.lastwatchdog.com/steps-forward-can-cnapp-solutions-truly-unify-cloud-on-premises-best-cybersecurity-practices/
Steps Forward: Can ‘CNAPP’ solutions truly unify cloud, on-premises best cybersecurity practices? | The Last Watchdog
A fledgling security category referred to as Cloud-Native Application Protection Platforms (CNAPP) is starting to reshape the cybersecurity landscape. Related: Computing workloads return on-prem CNAPP solutions assemble a varied mix of security tools and best practices and focuses them on intensively monitoring and managing cloud-native software, from development to deployment. Companies are finding that CNAPP […]
𝗛𝗼𝘄 𝘁𝗼 𝘀𝗲𝗰𝘂𝗿𝗲 𝗮 𝗙𝘂𝗻𝗰𝘁𝗶𝗼𝗻 𝗔𝗽𝗽?
𝚂̲𝚎̲𝚌̲𝚞̲𝚛̲𝚎̲ ̲𝚘̲𝚙̲𝚎̲𝚛̲𝚊̲𝚝̲𝚒̲𝚘̲𝚗̲
➡️Defender for Cloud for assessment of potential configuration-related security vulnerabilities
➡️Log and monitor: diagnostic settings to configure streaming export of platform logs and metrics
➡️Require HTTPS
➡️Securing keys with Azure key Vault
➡️Enable App Service Authentication/Authorization
➡️Use Azure API Management (APIM) to authenticate requests
➡️Run your function app with the lowest possible permissions
➡️Store data encrypted
𝚂̲𝚎̲𝚌̲𝚞̲𝚛̲𝚎̲ ̲𝚍̲𝚎̲𝚙̲𝚕̲𝚘̲𝚢̲𝚖̲𝚎̲𝚗̲𝚝̲
➡️Disable FTP
➡️Secure the scm endpoint
𝙽̲𝚎̲𝚝̲𝚠̲𝚘̲𝚛̲𝚔̲ ̲𝚜̲𝚎̲𝚌̲𝚞̲𝚛̲𝚒̲𝚝̲𝚢̲
➡️Set access restrictions
➡️Secure the storage account
➡️Private site access with Azure Private Endpoint
➡️Deploy your function app in isolation configuring a Web Application Firewall (WAF) for App Service Environment.
More details: https://learn.microsoft.com/en-us/azure/azure-functions/security-concepts?tabs=v4
#security #azure #cloud #data #management #streaming #functionapp #serverless #waf #appservice #privateendpoint #networksecurity #securedeployment #apim #ftp #keyvault #key #vulnerability #assessment #misconfiguration #encryption #storage #storageaccount #defender #defenderforcloud #cnapp #cspm #cwpp #microsoft #microsoftsecurity #cloudsecurity #cloudnative #siem #monitoring #soc