New.
Any.Run: New Phishing Campaign Targets US with Credential Theft: What CISOs Need to Know https://any.run/cybersecurity-blog/us-fake-invitation-phishing/ @anyrun_app #infosec #malware #threatresearch #phishing
New.
Any.Run: New Phishing Campaign Targets US with Credential Theft: What CISOs Need to Know https://any.run/cybersecurity-blog/us-fake-invitation-phishing/ @anyrun_app #infosec #malware #threatresearch #phishing
New.
Zscaler: Malicious OpenClaw Skill Distributes Remcos RAT and GhostLoader https://www.zscaler.com/blogs/security-research/malicious-openclaw-skill-distributes-remcos-rat-and-ghostloader #infosec #OpenClaw #threatresearch
New.
Recorded Future: Hacking Embodied AI https://www.recordedfuture.com/research/hacking-embodied-ai #infosec #threatresearch #bots #robots
New. The campaign targets China.
ESET: A rigged game: NKOR APT ScarCruft compromises gaming platform in a supply-chain attack https://www.welivesecurity.com/en/eset-research/rigged-game-scarcruft-compromises-gaming-platform-supply-chain-attack/ @ESETresearch #infosec #cyberattack #databreach #threatresearch #Windows #Android
New.
Cyera: Bleeding Llama: Critical Unauthenticated Memory Leak in Ollama https://www.cyera.com/research/bleeding-llama-critical-unauthenticated-memory-leak-in-ollama #threatresearch
More:
Security Week: Critical Bug Could Expose 300,000 Ollama Deployments to Information Theft https://www.securityweek.com/critical-bug-could-expose-300000-ollama-deployments-to-information-theft/ @SecurityWeek #infosec #vulnerability #LLM #Ollama
New.
Huntress: dMSA Ouroboros: Self-Sustaining Credential Extraction in Windows Server 2025 https://www.huntress.com/blog/dmsa-ouroboros-credential-extraction-windows-server-2025 https://www.huntress.com/blog/dmsa-ouroboros-credential-extraction-windows-server-2025 @huntress #infosec #threatresearch #Windows
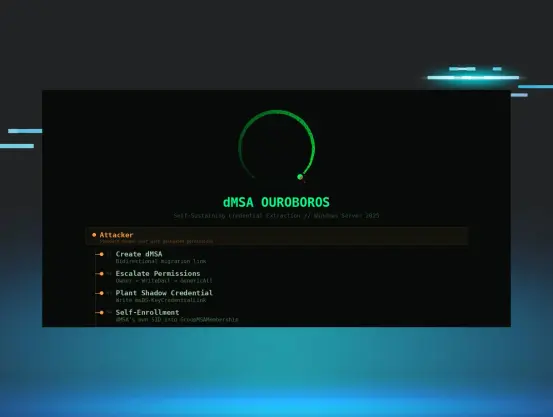
A fully patched Windows Server 2025 domain is vulnerable to dMSA Ouroboros—a self-sustaining credential extraction technique requiring only standard delegated permissions. Learn how it works, why remediation fails, and how to detect it.
⚡ Fresh Lightning Talk Alert for BSides Luxembourg 2026!
“𝗥𝗔𝗡𝗦𝗢𝗠-𝗜𝗦𝗔𝗖 𝗟𝗢𝗖𝗞 𝗦𝗧𝗔𝗥 𝗜𝗡𝗜𝗧𝗜𝗔𝗧𝗜𝗩𝗘” – 𝗘𝗟𝗟𝗜𝗦 𝗦𝗧𝗔𝗡𝗡𝗔𝗥𝗗
What if ransomware defenders shared knowledge as effectively as attackers share tactics?
In this fast-paced Main Stage session, Ellis Stannard introduces L.O.C.K. S.T.A.R. — Level of Critical Knowledge in Specialized Techniques on Advancements and Research — a community-driven recognition framework built by Ransom-ISAC to strengthen collaboration across the ransomware defense ecosystem.
From DFIR and reverse engineering to HUMINT, cryptocurrency tracing, AI, and quantum research, the initiative aims to surface and reward the practitioners doing the hard work behind the scenes. Think of it as a “Michelin star” system for ransomware expertise — designed to turn isolated intelligence into actionable community knowledge.
This session explores how structured knowledge sharing, recognition, and collaborative intelligence can help defenders reduce dwell time, accelerate response, and make life harder for ransomware operators.
Ellis Stannard is a security researcher and core member of the Ransom-ISAC initiative, contributing to collaborative threat intelligence efforts focused on ransomware and APT campaigns.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #Ransomware #ThreatIntelligence #DFIR #CyberSecurity #RansomISAC #ThreatResearch #BlueTeam #APT #InfoSec
New.
Socket: Malicious Ruby Gems and Go Modules Impersonate Developer Tools to Steal Secrets and Poison CI https://socket.dev/blog/malicious-ruby-gems-and-go-modules-steal-secrets-poison-ci #socket #infosec #threatresearch #RubyGems #GitHub
New.
"Hello! Yes, it's all a disaster again!"
Watch Tower: The Internet Is Falling Down, Falling Down, Falling Down (cPanel & WHM Authentication Bypass CVE-2026-41940) https://labs.watchtowr.com/the-internet-is-falling-down-falling-down-falling-down-cpanel-whm-authentication-bypass-cve-2026-41940/ #threatresearch
Also:
Tenable: Copy Fail (CVE-2026-31431): Frequently asked questions about Linux kernel privilege escalation vulnerability https://www.tenable.com/blog/copy-fail-cve-2026-31431-frequently-asked-questions-about-linux-kernel-privilege-escalation @tenable #Linux #infosec #vulnerability

Hello! Yes, it's all a disaster again! Let's get this party started: 0:00 /0:12 1× No comments today, so imagine this: * We wrote something that we find very funny, * Nobody else gets it, * But everyone humors us It's your typical watchTowr Labs blog introduction. What Is cPanel & WHM?
New.
Microsoft Email threat landscape: Q1 2026 trends and insights https://www.microsoft.com/en-us/security/blog/2026/04/30/email-threat-landscape-q1-2026-trends-and-insights/
Proofpoint:
Report highlights: AI is changing collaboration security faster than most organizations realize: key insights from the 2026 AI and Human Risk Landscape report https://www.proofpoint.com/us/blog/threat-insight/ai-changing-collaboration-security-faster-most-organizations-realize-key
The report: https://www.proofpoint.com/us/resources/threat-reports/ai-human-risk-landscape-report #Microsoft #infosec #threatintel #threatintelligence #phishing #threatresearch

In early 2026, email threats increased with a rise in credential phishing, QR code phishing, and CAPTCHA-gated campaigns, highlighted by Microsoft’s disruption of the Tycoon2FA phishing platform which led to a 15% volume decrease and shifts in threat actor tactics.