Microsoft Disputes Azure Vulnerability Report, Silent Patch Issued
Security researcher Justin O'Leary claims a critical flaw in Azure Backup for AKS could let users with zero Kubernetes permissions gain full cluster administration, but Microsoft disputes the finding. The tech giant quietly issued a patch without acknowledging the vulnerability.
#AzureVulnerability #CloudSecurity #Kubernetes #PrivilegeEscalation #MicrosoftAzure
MiniPlasma
MiniPlasma는 6년 전 Google Project Zero가 발견해 Microsoft에 보고한 CVE-2020-17103 취약점이 여전히 Windows의 cldflt.sys 드라이버에 존재함을 재조명합니다. 해당 취약점은 권한 상승(LPE) 문제로, 원본 PoC를 활용해 SYSTEM 권한 쉘을 생성하는 데 성공했으며, 모든 Windows 버전에 영향을 미치는 것으로 보입니다. Microsoft가 이 취약점을 제대로 패치하지 않았거나 패치를 되돌린 것으로 추정됩니다.
https://github.com/Nightmare-Eclipse/MiniPlasma
#windows #security #exploit #cve202017103 #privilegeescalation
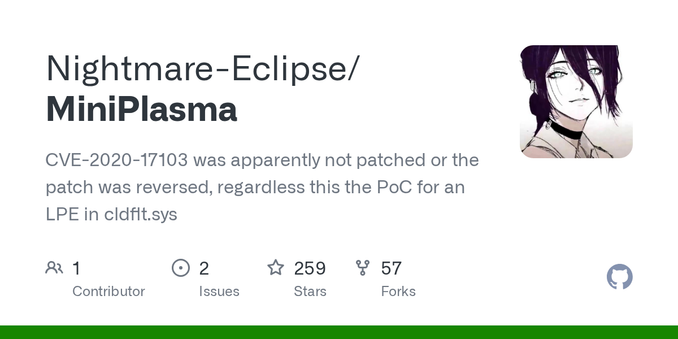
GitHub - Nightmare-Eclipse/MiniPlasma: CVE-2020-17103 was apparently not patched or the patch was reversed, regardless this the PoC for an LPE in cldflt.sys
CVE-2020-17103 was apparently not patched or the patch was reversed, regardless this the PoC for an LPE in cldflt.sys - Nightmare-Eclipse/MiniPlasma
OpenClaw Flaws Expose Data, Enable Privilege Escalation
A chain of four vulnerabilities, dubbed Claw Chain, in OpenClaw can be exploited to turn an agent into a powerful tool for attackers, allowing them to extract sensitive data, escalate privileges, and plant backdoors for long-term access. This flaw chain enables adversaries to gain a foothold, move undetected, and wreak havoc on an…
#PrivilegeEscalation #VulnerabilityChain #Openclaw #ClawChain #Cyera
AI znalazło lukę w macOS – dlaczego Mac nigdy nie będzie tak bezpieczny jak iOS?
Firma Anthropic i badacze z firmy Calif użyli modelu AI Claude Mythos, żeby znaleźć nową lukę w macOS. Przy okazji Jason Snell z Six Colors tłumaczy, jak Apple od lat zaciska ochronę Maca, nie rezygnując z jego otwartości.
AI znalazło lukę, zanim zrobili to złoczyńcy
Jak informuje MacRumors na podstawie „The Wall Street Journal”, badacze z firmy cyberbezpieczeństwa Calif użyli modelu Claude Mythos Preview — najnowszego modelu Anthropic — do odkrycia nowej luki w macOS. Konkretnie: model pomógł napisać kod łączący dwie istniejące podatności systemowe w taki sposób, że powstał z nich exploit klasy privilege escalation, czyli umożliwiający nieuprawnione podwyższenie uprawnień w systemie.
<p class="font-claude-response-body break-words whitespace-normal leading-1„>Żeby zrozumieć, dlaczego to istotne, trzeba wiedzieć, czym jest Memory Integrity Enforcement (MIE). To opracowany przez Apple sprzętowy system bezpieczeństwa pamięci, zbudowany na bazie specyfikacji Arm Memory Tagging Extension z 2019 roku. W skrócie: każdy blok pamięci otrzymuje tajny znacznik, a hardware weryfikuje, czy każde odwołanie do pamięci zawiera właściwy znacznik. Jeśli nie — aplikacja się zawiesza. Apple rozwijało MIE przez pięć lat i wdrożyło go w iPhone’ach 17 i iPhone Air, a następnie rozszerzyło na MacBooki z M5.<p class="font-claude-response-body break-words whitespace-normal leading-1„>Calif obeszło tę ochronę na M5 w pięć dni. Bruce Dang znalazł podatności 25 kwietnia. Dion Blazakis dołączył do zespołu 27 kwietnia. Josh Maine zbudował narzędzia, a 1 maja działający exploit był gotowy. Atak startuje z konta zwykłego użytkownika bez żadnych specjalnych uprawnień, korzysta wyłącznie ze standardowych wywołań systemowych i kończy się uzyskaniem dostępu do powłoki roota — czyli pełnej kontroli nad systemem. <p class="font-claude-response-body break-words whitespace-normal leading-1„>Calif zaznacza, że Mythos Preview był kluczowym wsparciem na każdym etapie: szybko zidentyfikował podatności należące do znanych klas błędów, a potem pomagał przez cały proces budowania exploita. Jednocześnie badacze przyznają, że autonomiczne ominięcie MIE wymagało ludzkiej ekspertyzy — AI samo tego nie zrobiłoby. Badacze zastrzegają, że samo AI nie wystarczyłoby — do przeprowadzenia całości konieczna była ich własna ekspercka wiedza. Niemniej przypadek ten potwierdza, że modele językowe mogą skutecznie asystować w znajdowaniu podatności w oprogramowaniu, co jest zarówno dobrą, jak i niepokojącą wiadomością — zależy, kto z tego korzysta.Anthropic uruchomiło projekt o nazwie Glasswing, który umożliwia firmom technologicznym, w tym Apple, korzystanie z Claude Mythos Preview do szukania luk bezpieczeństwa w systemach operacyjnych i przeglądarkach. Znaleziona przez Calif podatność dotyczyła jądra systemu — i co ciekawe, w notatkach do aktualizacji macOS 26.5, którą Apple wydało w tym tygodniu, pojawia się wzmianka o naprawionej luce kernelowej z podziękowaniem właśnie dla Calif i Anthropic. The Wall Street Journal jednak sugeruje, że spotkanie Calif z Apple odbyło się dopiero w tym tygodniu i poprawka może jeszcze nie być wdrożona. Apple poinformowało, że analizuje raport firmy Calif.
Puenta jest jednak wyraźna: mały zespół z dostępem do najlepszego modelu AI jest w stanie w tydzień pokonać zabezpieczenie, które kosztowało Apple lata pracy i prawdopodobnie miliardy dolarów.
Mac nigdy nie będzie tak bezpieczny jak iOS — i dobrze
To dobry moment, żeby sięgnąć po opublikowaną tego samego dnia analizę Jasona Snella z Six Colors, która nadaje całej historii szerszy kontekst.
Snell pisze, że Mac z założenia jest platformą otwartą — możesz na nim uruchomić dowolny kod z dowolnego źródła — i to jest coś, co sprawia, że Mac jest Makiem. Jednocześnie ta otwartość czyni go bardziej podatnym niż iOS, gdzie Apple kontroluje każdy fragment oprogramowania przez podpisywanie kodu, App Store i notaryzację. Od lat Apple prowadzi na macOS swoistą grę w krecika ze złośliwym oprogramowaniem: kiedy jedno wyjście zostaje zablokowane, scammerzy szukają kolejnego.
Kiedy Apple utrudniło instalowanie nienotaryzowanych aplikacji, scammerzy zaczęli instruować użytkowników, jak ominąć ostrzeżenia. Kiedy Apple utrudniło to do granic możliwości, przenieśli się do Terminala — i właśnie dlatego macOS 26.4 wprowadził ostrzeżenia przy wklejaniu kodu do Terminala, z inteligentnym mechanizmem rozpoznającym, czy użytkownik jest programistą (i wtedy ostrzeżenie jest mniej natrętne), czy zwykłym użytkownikiem (i wtedy blokada jest surowsza). Sprawdzane są też złośliwe skrypty AppleScript.
Do tego Apple przez ostatnie lata coraz mocniej kryptograficznie podpisuje partycje systemowe, ograniczyło uprawnienia kont administratorskich, wprowadza aktualizacje bezpieczeństwa w tle między normalnymi aktualizacjami systemu i — od macOS 26.4 — obowiązkowo synchronizuje klucze FileVault przez iCloud.
Snell kończy optymistycznie: jeśli scammerzy zeszli do poziomu nakłaniania użytkowników do wklejania kodu w Terminal, to być może po latach zaciskania śruby Apple sprawiło, że instalowanie złośliwego oprogramowania na Maku stało się po prostu za trudne dla przeciętnego oszusta. I że obietnica złożona przez przedstawiciela Apple na WWDC w 2018 roku — że użytkownicy Maka zawsze będą mogli uruchomić dowolny kod — wciąż jest dotrzymana.
#Anthropic #Bezpieczeństwo #ClaudeMythos #FileVault #Gatekeeper #JasonSnell #lukaBezpieczeństwa #macOS #macOSTahoe265 #notaryzacja #privilegeEscalation #ProjectGlasswing #SixColors #terminalThe “Fragnesia” Linux kernel flaw enables local root access attacks - proving once again that kernel-level bugs can turn minor access into full compromise. 🐧⚠️ #LinuxSecurity #PrivilegeEscalation
#infosec #cybersecurity
Three minor #Linux #kernel releases in three days to fix the copy fail / dirty frag local #privilegeescalation
You would think the #shitshow is over?
Nope! Today, Gentoo published new kernels with a bespoke patch.
--- linux-6.18.29-gentoo/net/core/skbuff.c 2026-05-12 12:00:13.960097343 +0200
+++ linux-6.18.29-gentoo-r1/net/core/skbuff.c 2026-05-14 12:36:07.935053114 +0200
@@ -2188,6 +2188,7 @@
skb_frag_ref(skb, i);
}
skb_shinfo(n)->nr_frags = i;
+ skb_shinfo(n)->flags |= skb_shinfo(skb)->flags & SKBFL_SHARED_FRAG;
}
if (skb_has_frag_list(skb)) {
@@ -6149,6 +6150,8 @@
from_shinfo->frags,
from_shinfo->nr_frags * sizeof(skb_frag_t));
to_shinfo->nr_frags += from_shinfo->nr_frags;
+ if (from_shinfo->nr_frags)
+ to_shinfo->flags |= from_shinfo->flags & SKBFL_SHARED_FRAG;
if (!skb_cloned(from))
from_shinfo->nr_frags = 0;
Linux Flaw Exposes Systems to Root Privilege Attacks
A newly discovered Linux kernel vulnerability, dubbed Fragnasia, allows hackers to gain root privileges and take control of your system - and it's been hiding in plain sight in all Linux kernels released before May 13, 2026. This high-severity flaw lets unprivileged attackers write malicious code into read-only files, giving…
#LinuxKernelVulnerability #Cve202646300 #Fragnesia #EmergingThreats #PrivilegeEscalation
#Fragnesia Made Public As Latest #Linux Local #PrivilegeEscalation #Vulnerability
A new Linux local privilege escalation flaw called Fragnesia has been disclosed as a Dirty Frag-like vulnerability, allowing arbitrary byte writes into the #kernel page cache of read-only files through a separate ESP/XFRM logic bug.
#dirtyfrag #security

Fragnesia Made Public As Latest Linux Local Privilege Escalation Vulnerability - Slashdot
A new Linux local privilege escalation flaw called Fragnesia has been disclosed as a Dirty Frag-like vulnerability, allowing arbitrary byte writes into the kernel page cache of read-only files through a separate ESP/XFRM logic bug. Phoronix reports: Proof of concept code for Fragnesia is already ou...
Linux Defenders Scramble to Outpace Exploit Cycle
Linux defenders are racing against the clock to outmaneuver exploiters, with one maintainer proposing a temporary "kill switch" to disable vulnerable kernel functions until a proper patch can be developed. This stopgap solution aims to buy crucial time between vulnerability discovery and patch release.
#LinuxKernelExploit #EmergingThreats #Cve202643284 #PrivilegeEscalation #VulnerabilityManagement






