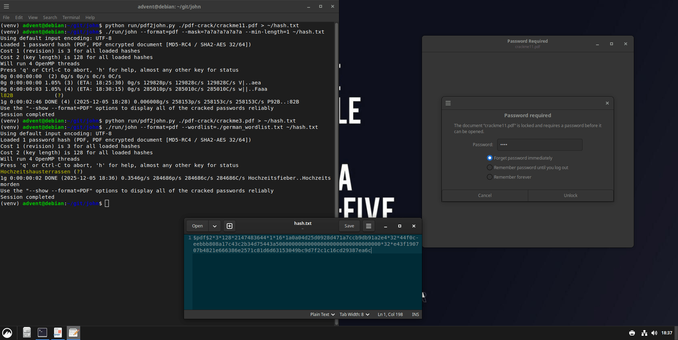
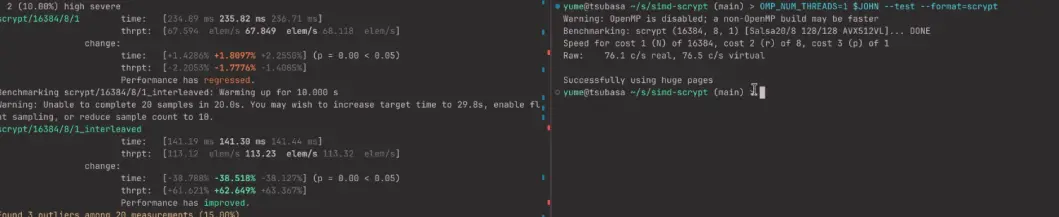
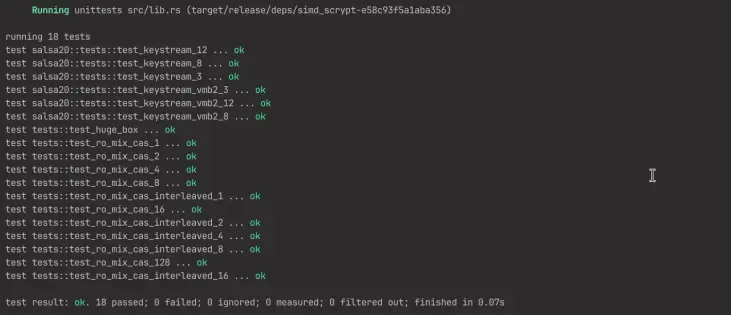
Today we explore John the Ripper, one of the most powerful and flexible open-source password-cracking tools. It is widely used for security testing, digital forensics, and understanding how weak passwords can be recovered.
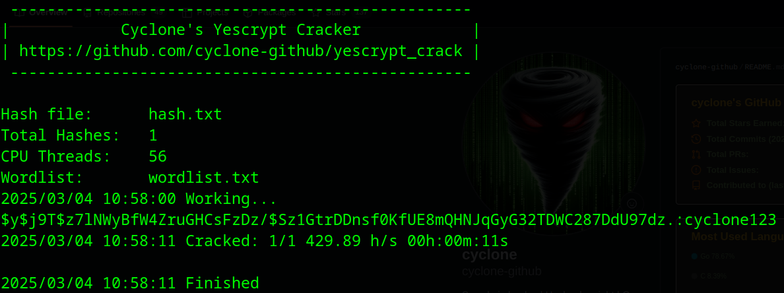
John works by taking a password hash and trying to recover the original password. It can do this in different ways, for example through brute force, where every possible combination is tried, or through wordlists, where John tests passwords from a predefined dictionary. When the generated hash matches the original, the password is revealed.
This tool is perfect for learning about cybersecurity, testing the strength of your own passwords, or experimenting with how attackers might attempt to crack weak credentials.
Pro tip: try using both brute force and a wordlist. You’ll immediately see how effective wordlists can be compared to testing every combination.
Which hashing algorithm gives you the most headaches?
Link: https://github.com/openwall/john
#FOSS #OpenSource #Linux #CLI #Terminal #JohnTheRipper #CyberSecurity #PasswordCracking #SecurityTools #HashCracking #Pentesting #EthicalHacking #DigitalForensics #Unix #Infosec #NerdContent #TechNerds #AdventCalendar #OpenTools #FOSSAdvent #adventkalender #adventskalender