The Register: 60% of MD5 password hashes are crackable in under an hour. “Using a dataset of more than 231 million unique passwords sourced from dark web leaks – including 38 million added since its previous study – and hashing them with MD5, researchers at security firm Kaspersky found that, using a single Nvidia RTX 5090 graphics card, 60 percent of passwords could be cracked in less than an […]
https://rbfirehose.com/2026/05/10/the-register-60-of-md5-password-hashes-are-crackable-in-under-an-hour/MD5 Password Hashes Cracked in Under an Hour
In a shocking test, Kaspersky researchers cracked 60% of 231 million MD5 password hashes in under an hour using just one high-powered graphics card, revealing the alarming vulnerability of even the most seemingly secure passwords. This unsettling experiment highlights the urgent need for stronger password protection.
GPU Price Doesn't Dictate Password Cracking Success
You don't need to break the bank on cutting-edge AI hardware to crack weak passwords - a recent study found that a $30,000 GPU doesn't outperform readily available consumer cards, proving that attackers can succeed with everyday tech.
#PasswordCracking #BruteForce #WeakCredentials #EmergingThreats #AiHardware
Removing the BIOS Administrator Password on a ThinkPad Takes Timing
#SecurityHacks #Bios #Passwordcracking
#Computerhacks #Bios #Passwordcracking
If you are:
"abusing" hashcat
--stdoutor other cracking tools (or bulk string-generation tools) using GNU parallel, andyou're producing highly duplicate output per process, and
you need to do low-memory, best-effort dedupe in parallel, per process prior to passing the aggregated output to a final dedupe
... the dedupe tool included in CynosurePrime's rling repo:
https://github.com/Cynosureprime/rling
... really does the trick! Just do:
[parallel stuff] '[cmd] | dedupe' | final-process-thing
Thanks, @Waffle_Real !
GitHub - Cynosureprime/rling: RLI Next Gen (Rling), a faster multi-threaded, feature rich alternative to rli found in hashcat utilities.
RLI Next Gen (Rling), a faster multi-threaded, feature rich alternative to rli found in hashcat utilities. - GitHub - Cynosureprime/rling: RLI Next Gen (Rling), a faster multi-threaded, feature ri...
@kibcol1049 nope nope nope nope nope :)
This chart is highly irrelevant for end-users and very deceptive if you don’t take it into the context of the full article it illustrates.
I crack +40 characters long passwords on a regular basis.
Don’t share this chart.
ping @tychotithonus ;)
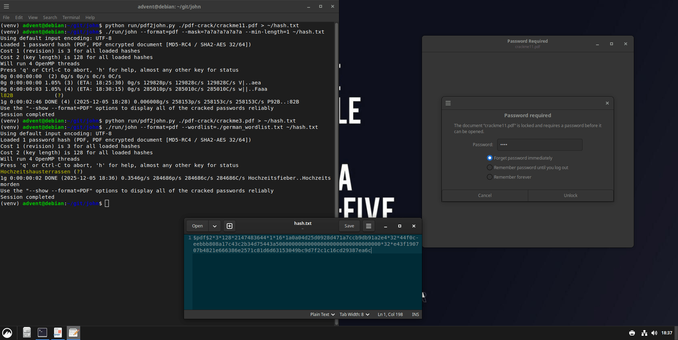
Today we explore John the Ripper, one of the most powerful and flexible open-source password-cracking tools. It is widely used for security testing, digital forensics, and understanding how weak passwords can be recovered.
John works by taking a password hash and trying to recover the original password. It can do this in different ways, for example through brute force, where every possible combination is tried, or through wordlists, where John tests passwords from a predefined dictionary. When the generated hash matches the original, the password is revealed.
This tool is perfect for learning about cybersecurity, testing the strength of your own passwords, or experimenting with how attackers might attempt to crack weak credentials.
Pro tip: try using both brute force and a wordlist. You’ll immediately see how effective wordlists can be compared to testing every combination.
Which hashing algorithm gives you the most headaches?
Link: https://github.com/openwall/john
#FOSS #OpenSource #Linux #CLI #Terminal #JohnTheRipper #CyberSecurity #PasswordCracking #SecurityTools #HashCracking #Pentesting #EthicalHacking #DigitalForensics #Unix #Infosec #NerdContent #TechNerds #AdventCalendar #OpenTools #FOSSAdvent #adventkalender #adventskalender