Cartoon medical equipment #Apparat #Machine #Xray #Ultrasound #Mri #Dropper #Clinic #Infirmary #Hospital #Care #Emergency #Medical #Medicine #Doctor #Surgery #AssetStore
🚨 ALERT: Banking Apps Under Attack: Credentials Hijacked via Telegram
⚠️ A #malware dropper delivers a stealer disguised as the IndusInd Bank app. It embeds a phishing website inside the Android app to steal victims’ financial data, posing a threat to mobile banking users and financial institutions.
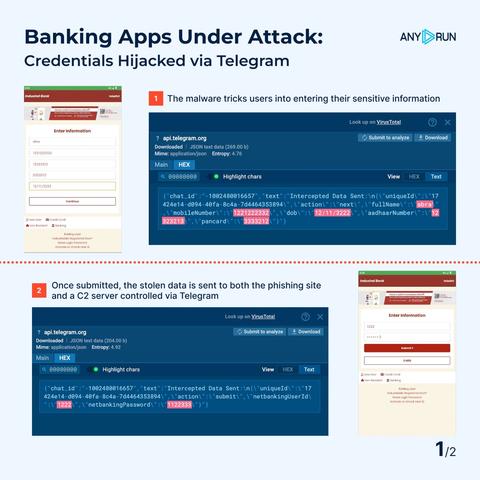
The malware tricks users into entering their sensitive information (registered mobile number, Aadhaar number, PAN card, net banking user ID, etc.) through a fake banking interface embedded in the app.
📥 Once submitted, the stolen data is sent to both the #phishing site and a C2 server controlled via Telegram.
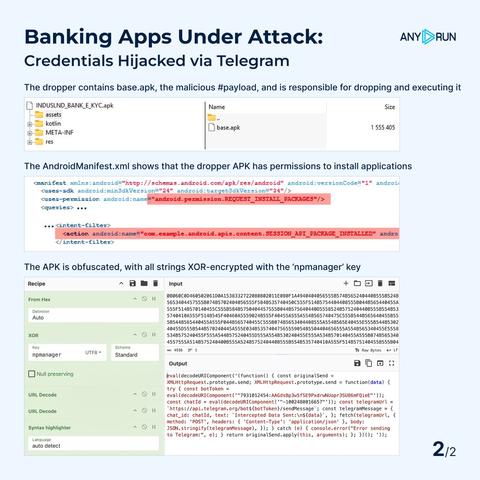
The AndroidManifest.xml shows that the dropper APK has permissions to install applications. The #dropper contains base.apk, the malicious #payload, and is responsible for dropping and executing it.
👨💻 Our new #Android sandbox allows #SOC teams reveal base.apk behavior: communication via Telegram, starting from another location, monitoring incoming messages, and more. Fast access to threat details enables deep analysis and proactive response, mitigating potential damage.
The APK is obfuscated, with all strings #XOR-encrypted with the ‘npmanager’ key. The CyberChef recipe below reveals the script that sends intercepted data to Telegram: https://gchq.github.io/CyberChef/#recipe=From_Hex%28%27Auto%27%29XOR%28%7B%27option%27%3A%27UTF8%27%2C%27string%27%3A%27npmanager%27%7D%2C%27Standard%27%2Cfalse%29%26oeol%3DNEL
#IOCs:
#Phish URL: hxxps://t15[.]muletipushpa[.]cloud/page/
C2 Server (Telegram Bot): hxxps://api[.]telegram[.]org/bot7931012454:AAGdsBp3w5fSE9PxdrwNUopr3SU86mFQieE
More IOCs and insights will be shared in our blog post. Let us know if you're interested! 💬
🚀 Expose Android threats in seconds with real-time APK analysis in #ANYRUN Sandbox: https://app.any.run/?utm_source=mastodon&utm_medium=post&utm_campaign=android_banking_app&utm_term=200325&utm_content=linktoregistration#register/
💡 Malware: cosa sono, quali e come difendersi
Panoramica completa sul mondo oscuro dei malware, le diverse famiglie di questi software malevoli che rappresentano una costante minaccia per la sicurezza dei dispositivi e dei dati.
https://gomoot.com/malware-cosa-sono-quanti-sono-e-come-difendersi/
#Adware #Backdoor #Dropper #malware #ransomware #spyware #tech #tecnologia #Trojan #virus #hacker #dialer
The material impact [of #operationendgame] to attackers is that they’ve just had it laid out to them, very clearly, that there’s a capable, resourced, and persistent threat in play on the defender side.
International Law Enforcement Operation Cracks Down on Some of the Biggest Dropper Malware and Botnets
A Europol-headed law enforcement operation has put a serious dent in the dropper malware ecosystem, disrupting the botnets that these dropper systems rely on to function, with over 100 servers and 2,000 domains impacted across about a dozen countries.
https://arstechnica.com/security/2024/05/over-100-malware-dropper-servers-crushed-in-largest-ever-botnet-takedown/ #malware #dropper #ransomware #spyware
Largest ever operation against botnets hits dropper malware ecosystem
Congratulations to Europol and partners for concluding an
International operation that disrupted botnets responsible for distributing IcedID, SystemBC, Pikabot, Smokeloader and Bumblebee botnets.
Now it's up to the courts to impose serious sentences on the perpetrators.
“Le #dropper (#Brunhilda) déploie une version mise à jour du malware bancaire #Vultur via 3 charges utiles” : nouvelle variation du #trojan bancaire Vultur sous Android !