Is there any tool (#DNS server or standalone) where I can keep managing a plain file and then the signed records live independently?
Is there any tool (#DNS server or standalone) where I can keep managing a plain file and then the signed records live independently?
Unser aktueller Security Digest ordnet ein, was die letzten Wochen wirklich relevant war:
🔐 Copy Fail, Dirty Frag, Dirty Pipe: Local Privilege Escalation bleibt eine der häufigsten Schwachstellenklassen im Linux-Kernel. Unser Take: SELinux ist kein Nice-to-have, sondern die wirksamste Gegenmaßnahme. Nicht-privilegierte Accounts sollten nicht unter unconfined_u laufen. Punkt.
🌐 DNSSEC-Ausfall der .de-Zone: Ein Signierfehler bei der DENIC hat am 05.05. gezeigt, wie fragil zentralisierte DNS-Infrastruktur sein kann.
🤖 KI und Open Source: curl erlebt nach der AI-Slop-Welle jetzt hochwertige Meldungen. Gleichzeitig steigt die Last für Maintainerinnen und Maintainer massiv.
📱 Android Intrusion Logging: Google liefert mit dem Advanced Protection Mode endlich eine echte Datenquelle für mobile Forensik. Wir empfehlen die Aktivierung für exponierte Personen und Organisationen mit erhöhtem Schutzbedarf.
Das Security-Modell aus dem Mobilbereich wird zunehmend zum Vorbild für Desktop und Server. Wer heute noch ohne Mandatory Access Control arbeitet, liefert eine Angriffsfläche, die sich mit wenigen Konfigurationsschritten deutlich reduzieren ließe. Den vollständigen Digest mit allen Quellen und unserer Einordnung finden Sie hier: https://research.hisolutions.com/2026/05/
Wie gehen Sie in Ihrer Organisation mit SELinux um? Und nutzt jemand von Ihnen bereits Android Intrusion Logging in der Vorfallsbehandlung?
#Cybersecurity #SELinux #DNSSEC #AndroidSecurity #OpenSource @brahms @jrt
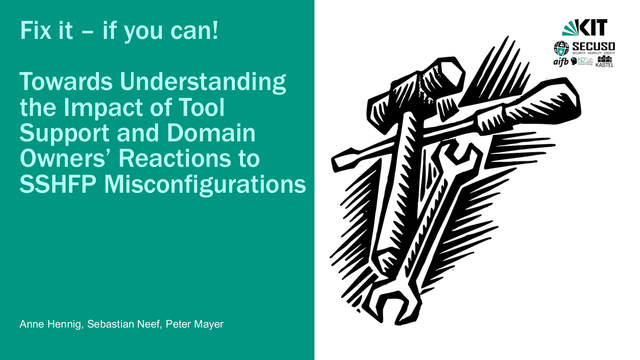
#SSHFP #DNSSEC
Rolling the Root Key
DNSSEC에서 사용하는 암호키는 시간이 지남에 따라 공격 가능성이 증가하므로 정기적인 키 교체가 필수적입니다. 특히 DNS 루트 존의 키서명키(KSK)는 교체 주기가 길어, 새로운 키가 모든 검증자에 신뢰받기까지 오랜 시간이 필요합니다. 2026년 10월 예정된 루트 KSK 교체는 알고리즘 변경 없이 키 값만 교체하는 작업이며, RFC 8145 신호를 통해 DNS 검증자들이 새 키를 신뢰 앵커에 추가했는지 모니터링합니다. 이 과정은 DNSSEC의 보안성과 신뢰성을 유지하는 데 중요한 운영 관행입니다.
New canary Unbound QUIC build is out. Runs on basically any platform @nlnetlabs Unbound supports. Distroless, and built using our hardened native and mighty 🦾 OpenSSL 3.6.2 + QUIC build environment! (https://github.com/madnuttah/openssl-buildenv)
Full DNSSEC support, QUIC/HTTP3 via ngtcp2/nghttp3... So much fun!
cc @nlnetlabs 💚
https://github.com/madnuttah/unbound-docker
https://hub.docker.com/r/madnuttah/unbound
#DNS #DNSSEC #DoT #DoH #QUIC #HTTP3 #Unbound #FOSS #SelfHosting #Homelab #Privacy
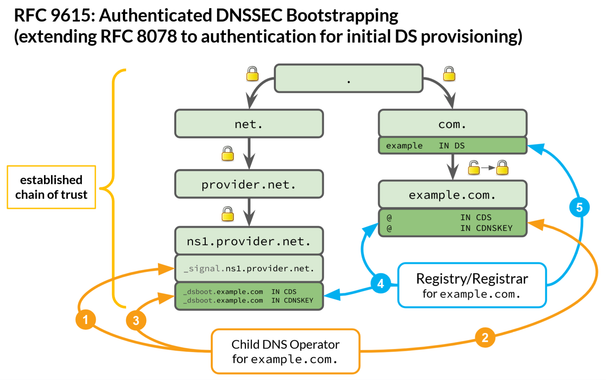
Automatic authenticated DNSSEC Bootstrapping in PowerDNS Authoritative
The day the German internet ground to a halt.
This was supposed to be a post about the CENTR Jamboree in Berlin, hosted by DENIC. Instead, it's a post about the night the .de zone stopped resolving — and an event with two faces.
The event was unlike any CENTR Jamboree before, and one I hope won't be repeated any time soon. I had very little sleep — not because of great social events, but because of the amount of work in the crisis team.