The
#paper “Fix It - If you Can! Towards Understanding the Impact of Tool Support and Domain Owners’ Reactions to SSHFP Misconfigurations" by Anne Hennig, Sebastian Neef, and Peter Mayer has been accepted for presentation at the
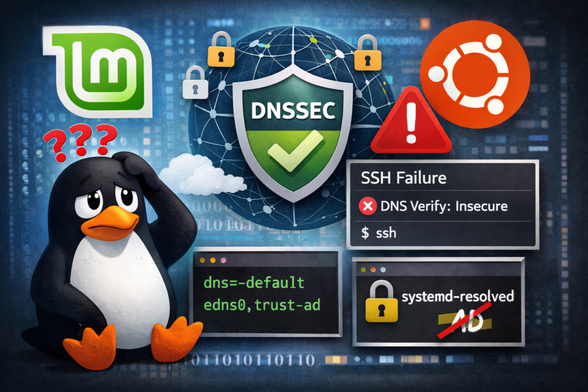
@ACSAC_Conf! The paper sent notifications to domain owners with misconfigured
#SSHFP records, investigating the effect of tool support. While the sender of the
#notification itself has no effect, the results suggest that tool support might increase remediation when the sender of the notification is different than the institution providing the tool. By analyzing domain owners’ responses to the authors' notification, multiple reasons for non-remediation were identified, supporting the argument that remediation rate should not be considered a success measure for a notification campaign but instead individual challenges faced by domain owners should be taken into account. ACSAC will take place December 8 to 12, 2025, in Honolulu, Hawaii, USA:
https://www.acsac.org/@Aryderwood @gehaxelt