@bortzmeyer As the manager of the Cascade project, I feel it's important to provide some context and nuance to the terms "alpha”, “beta" and “production ready”. This applies especially to software that is intended to run in critical infrastructure, with possible grave consequences when there is a failure.
While @nlnetlabs is building Cascade on 25 years of experience in DNS and software architecture, operators should not take our work for granted based on that.
This is our plan.
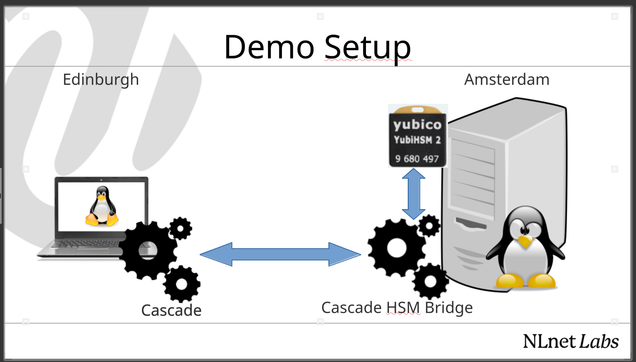
We have frozen the feature set Cascade has now, for the beta release. That means a DNSSEC signer with HSM support, IXFR in and out with TSIG, deterministic incremental signing, review hooks, and monitoring endpoints.
We will mark this release as “beta” in the coming weeks, but read this as whatever you feel is appropriate given the context I gave. That being said: we will dogfood this release. Starting this summer, operators can put Cascade in their testing environments to put it through their wringers, so we can iron out bugs and fix corner cases.
Over the coming months, our aim to have operators build the confidence to start deploying Cascade in production, with the expectation that we'll see real-world Cascade deployments towards the end of this year.