Как я автоматизировал отправку постов в Threads* и X*, но споткнулся о невидимые лимиты Twitter*
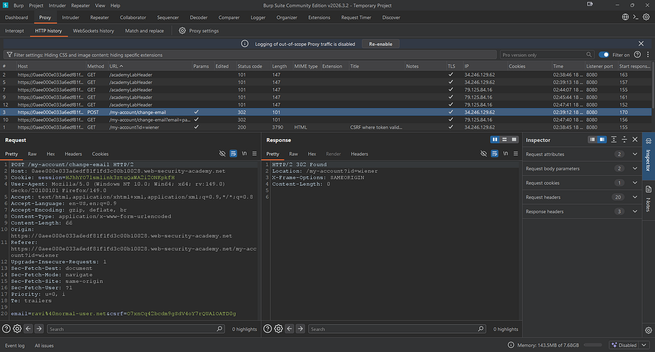
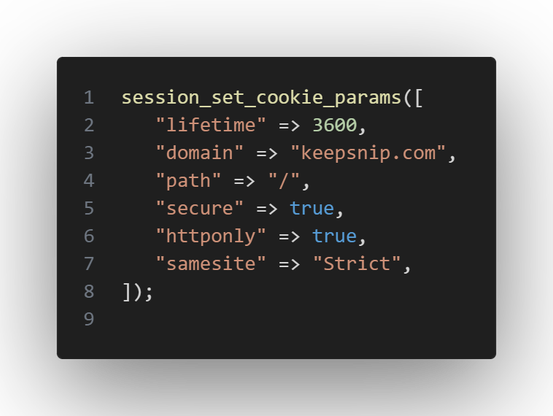
Я хотел сделать простую штуку: написал пост один раз, а он сам улетел в Threads* и X*. С Threads всё оказалось почти скучно: официальный API, токен, два запроса, готово. С X* началась отдельная инженерная прогулка по тёмному лесу: официальный API стоит денег, сервер из России напрямую ходит нестабильно, а браузерный GraphQL-путь то публикует, то отвечает 200 без созданного поста, то присылает 226, 344 или внезапное Tweet needs to be a bit shorter. В этой статье разбираю, как я собрал кросспостинг через Cloudflare Worker, где достать auth_token и ct0, почему нельзя верить HTTP-статусу, какие лимиты и антибот-ошибки реально прилетают, и что показали две недели логов.
https://habr.com/ru/articles/1031926/
#Threads_API #X_API #Twitter_API #Cloudflare_Worker #GraphQL #автопостинг #кросспостинг #rate_limits #auth_token #CSRF