Rooting Home Assistant through MeshCore: XSS attacks with a LoRa node name
New write-up published: Prototype Pollution in Practice
Using three PortSwigger labs, I walk through a repeatable methodology.
Less about lab solutions, more about the process.
https://medium.com/@marduk.i.am/prototype-pollution-in-practice-437958d27751
pretalx XSS flaw lets attackers hijack conference organizer accounts, steal sessions, auto-accept talks, and demote admins. Patched in v2026.1.0.
Read: https://hackread.com/zero-click-pretalx-xss-hackers-hijack-conference-accounts/
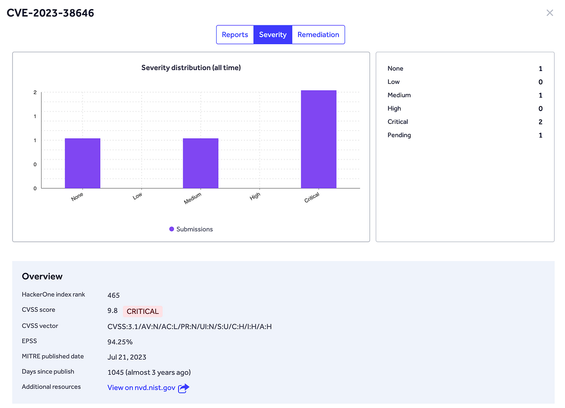
This CVE Has Only 5 Reports on HackerOne — But a 94% Chance of Being Exploited Right Now
This vulnerability is an XSS (Cross-Site Scripting) issue with a high likelihood (94%) of immediate exploitation. The flaw stems from the application's insufficient input validation, specifically for user comments containing JavaScript code. Upon successful injection, these scripts execute in the context of the target domain due to lacking Content Security Policy headers, demonstrating a logical error in the application's handling of user inputs. The impact includes session hijacking, unauthorized access, or information disclosure. This CVE has only 5 reports on HackerOne, but it poses a significant threat due to its high exploitability. The researcher received $100 for their report; the program responded by implementing Content Security Policy headers to prevent future XSS attacks. To remediate similar issues, developers should validate user inputs at all levels and enforce proper CSP headers. Key lesson: Validate user input and implement Content Security Policies to protect against XSS attacks. #BugBounty #WebSecurity #XSS #InputValidation #ContentSecurityPolicy
API Security 101: Understanding the Foundation and Why Attacks are Rising
This article discusses the growing importance of API security and the rising number of attacks against APIs. The author explains that APIs have become critical components in modern applications, handling a wide range of tasks including authentication, data transfer, and business logic. However, their increasing usage has exposed numerous vulnerabilities. One specific example provided is an XSS (Cross-Site Scripting) attack on an API endpoint via client-side manipulation of cookies or JavaScript. The researcher was able to exploit insufficient input validation by injecting malicious scripts within the user's session cookie, which executed upon subsequent API requests due to the lack of Content Security Policy headers. The impact includes unauthorized access, data theft, and account hijacking. The author recommends implementing proper access controls, token-based authentication, rate limiting, and input validation to secure APIs. Key lesson: Secure APIs are crucial for maintaining application security in the modern digital landscape. #API #Cybersecurity #WebSecurity #XSS #Authentication #InputValidation
🚨 Slim Framework released a patch fixing a reflected XSS vulnerability in the HTML error renderer.
Affected versions:
>=v4.4.0, <=v4.15.1
If you are passing unsanitized user input into HttpException, upgrade to Slim v4.15.2 immediately!
https://www.slimframework.com/2026/05/22/slim-security-advisory.html
https://github.com/slimphp/Slim/security/advisories/GHSA-53h4-8rc4-f539