因为在现在的ipad上用csp画漫画太卡打算升级设备,调查的过程里发现 #csp 官方居然有选购?指南:
🌙 Kyle 🌙
Lately I'm rewatching South Park, so I'm doing some randoms fanarts in between comms~ Kyle it's my fav between the main kids!
#drawing #digital #art #illustration #human #humanoid #fanart #southpqark #south_park #south #park #kyle #broflovski #kylebroflovski #kyle_broflovski #kid #male #men #boy #sketch #sketchpage #doodle #coloredsketch #colored_sketch #csp #clipstudiopaint
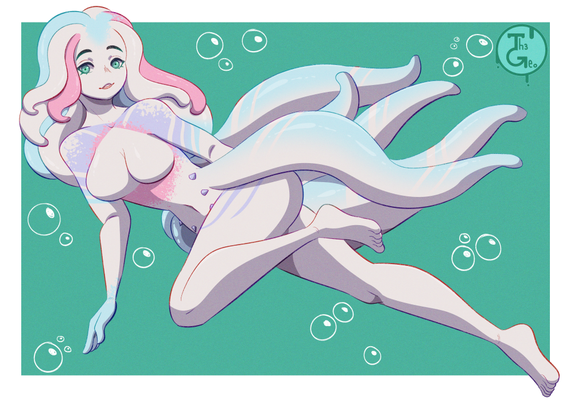
#mermaid #mermay #mermay2026 #beauty #pretty #underwater #bellydancer #bellydancing #kwalthersart #myart #ClipStudioPaintEX #ClipStudioPaint #CSP #DigitalArt #woman #sexy #beautiful #female
A Belly Dancing Mermaid for Mermay 2026
------------
Made with Clip Studio Paint Ex and a Huion Kamvas
If you want to see more of my work, check out https://kwalthersart.carrd.co/
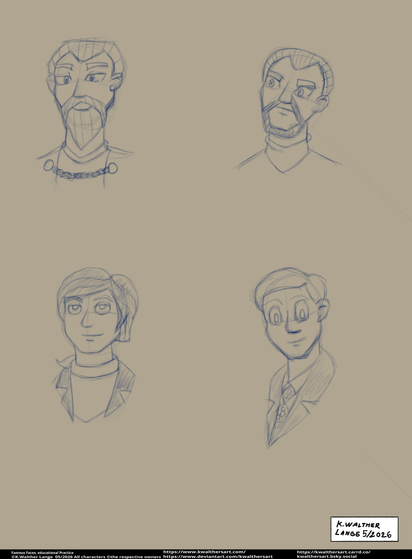
#famousactors #RogerDelgado #ChristopherLee #YousukeOkada #DickVanDyke #DoctorWho #StarWars #SuperRobotRedBaron #ClipStudioPaintEX #CSP
I did some practice sketching faces to see if i could do it right.
Not sure but it looks okay, can you guess whose Whom? see below
From left to Right, Christopher Lee as Count Dooku, Roger Delgado as the Master, Yousuke Okada as Ken Kuenai, and Dick Van Dyke as Robert Petrie
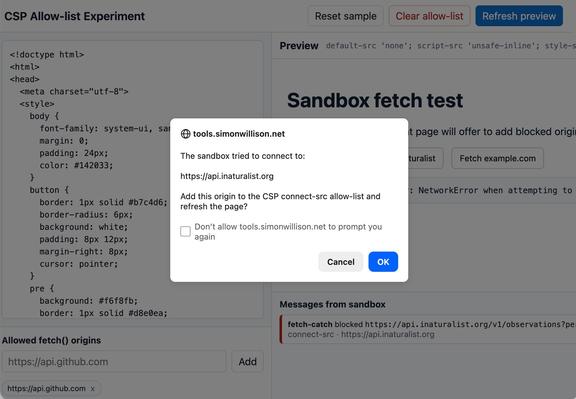
The one header I didn't add yet: CSP.
For sites that render untrusted input it mitigates an active surface. For a static site it guards against rarer-but-bigger events: a compromised analytics script, a poisoned CDN, a future change that adds an input path.
Astro 6 added an integration for what it emits; iframes, external fonts, and third-party services stay manual. Will inshallah follow when the audit fits.
CSP Allow-list Experiment
https://simonwillison.net/2026/May/13/csp-allow/#atom-everything
✨WIP✨
Spicy wip with my OC Keki~
#wip #workinprogress #sketch #sketchpage #doodle #furry #fursona #anthro #drawing #oc #originalcharacter #girl #female #woman #donkey #nsfw #notsafeforwork #hot #fap #spicy #nude #naked #dick #penis #cock #oral #sixtynine #69 #pleasure #sub #submissive #csp #clipstudiopaint #adult
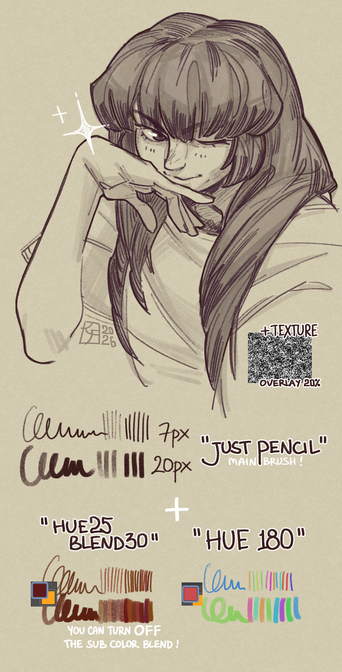
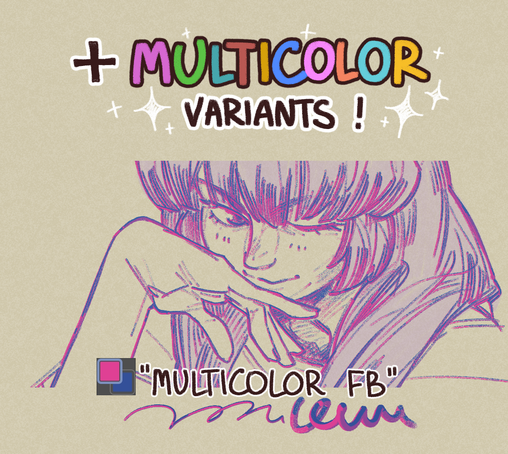
#csp #clipstudiopaint #cspassets #cspbrushes
It is here: https://assets.clip-studio.com/en-us/detail?id=2268082