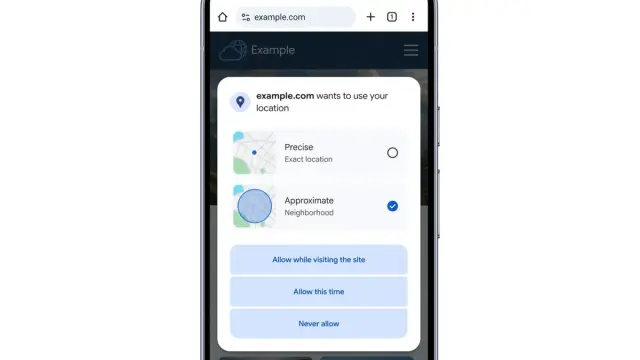
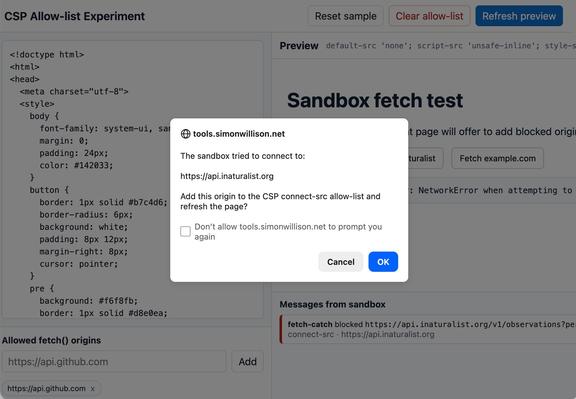
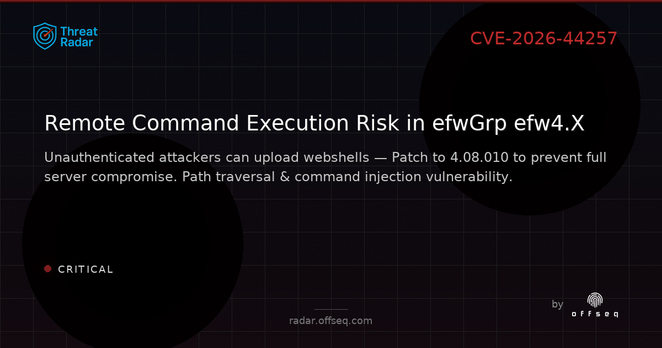
#AI #Cybersecurity #CAPTCHA #Technology #Internet #Bots #OnlineSecurity #DigitalSecurity #MachineLearning #Privacy #Spam #Automation #WebSecurity #Tech #CyberAttack #DataProtection #Innovation
https://the-14.com/more-and-more-websites-want-proof-youre-human-blame-the-bots/