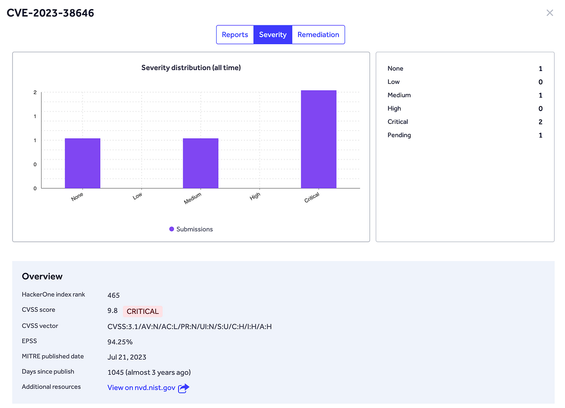
This CVE Has Only 5 Reports on HackerOne — But a 94% Chance of Being Exploited Right Now
This vulnerability is an XSS (Cross-Site Scripting) issue with a high likelihood (94%) of immediate exploitation. The flaw stems from the application's insufficient input validation, specifically for user comments containing JavaScript code. Upon successful injection, these scripts execute in the context of the target domain due to lacking Content Security Policy headers, demonstrating a logical error in the application's handling of user inputs. The impact includes session hijacking, unauthorized access, or information disclosure. This CVE has only 5 reports on HackerOne, but it poses a significant threat due to its high exploitability. The researcher received $100 for their report; the program responded by implementing Content Security Policy headers to prevent future XSS attacks. To remediate similar issues, developers should validate user inputs at all levels and enforce proper CSP headers. Key lesson: Validate user input and implement Content Security Policies to protect against XSS attacks. #BugBounty #WebSecurity #XSS #InputValidation #ContentSecurityPolicy
API Security 101: Understanding the Foundation and Why Attacks are Rising
This article discusses the growing importance of API security and the rising number of attacks against APIs. The author explains that APIs have become critical components in modern applications, handling a wide range of tasks including authentication, data transfer, and business logic. However, their increasing usage has exposed numerous vulnerabilities. One specific example provided is an XSS (Cross-Site Scripting) attack on an API endpoint via client-side manipulation of cookies or JavaScript. The researcher was able to exploit insufficient input validation by injecting malicious scripts within the user's session cookie, which executed upon subsequent API requests due to the lack of Content Security Policy headers. The impact includes unauthorized access, data theft, and account hijacking. The author recommends implementing proper access controls, token-based authentication, rate limiting, and input validation to secure APIs. Key lesson: Secure APIs are crucial for maintaining application security in the modern digital landscape. #API #Cybersecurity #WebSecurity #XSS #Authentication #InputValidation
https://badhost.org/ #CVE2026 #AIsecurity #inputvalidation #cybersecurity #vulnerabilities #HackerNews #ngated
BadHost - CVE-2026-48710 Starlette Host-Header Auth Bypass
Scan your Starlette or FastAPI server for CVE-2026-48710 (BadHost): a critical auth bypass via Host header injection affecting MCP servers, LLM proxies, AI agent frameworks, and thousands of Python ASGI applications.
How I Found a P1 Bug in a Bug Bounty Program (Step-by-Step Guide)
This article details the discovery of an XSS vulnerability due to insufficient input validation and lack of Content Security Policy (CSP). The application accepted user input for a query parameter without proper sanitization, allowing script injection through the 'query' field. By injecting a JavaScript payload containing document.cookie manipulation code, the researcher was able to set and persist a PHPSESSID cookie on the victim's device. This payload was executed by the browser, creating a persistent session cookie that allowed an attacker to maintain unauthorized sessions and gain access to other users' accounts without needing their login credentials. The vulnerability paid out $1,000, and the organization addressed it by implementing strong input validation and setting appropriate CSP headers—never trust user-controlled data for security decisions. Key lesson: Validate inputs and enforce strict Content Security Policies to prevent XSS attacks. #BugBounty #XSS #CSP #InputValidation #Infosec
The Bouncer Who Never Checked IDs
This vulnerability was an XSS (Cross-Site Scripting) issue due to insufficient input validation and lack of Content Security Policy (CSP). The application accepted user input for a query parameter without proper sanitization, allowing script injection through the 'query' field. The researcher injected a payload containing JavaScript code that set a cookie named 'PHPSESSID', which is a unique session identifier in PHP applications. This payload was executed by the browser on the victim's device, creating a persistent session cookie. With this cookie, an attacker could maintain unauthorized sessions and gain access to other users' accounts without needing their login credentials. The vulnerability paid out $250, and the organization addressed it by implementing strong input validation and setting appropriate CSP headers—never trust user-controlled data for security decisions. Key lesson: Always validate inputs and enforce strict Content Security Policies. #BugBounty #XSS #CSP #InputValidation #Infosec
Web Security Series #14 — Blind Command Injection Exploitation
This article discusses a Blind Command Injection (BCI) vulnerability in an unnamed web application. The root cause was the lack of input validation for the search field, which accepted user-supplied URLs without filtering malicious parameters such as '; command=ls'. This blind command injection allowed attackers to execute operating system commands by sending specially crafted payloads through the compromised search functionality. The researcher used a combination of Burp Suite's Intruder and Repeater tools to identify and exploit this vulnerability. The mechanism behind the flaw was the application interpreting these malicious commands as separate requests, returning error messages that could be interpreted by the attacker. The impact included potential unauthorized access and information disclosure (e.g., listing files using 'ls' command). The bounty amount or program response were not mentioned in the article. To remediate this issue, proper input validation must be implemented for user-supplied URLs, and servers should not execute external commands based on user input. Key lesson: Input validation is crucial for preventing Blind Command Injection attacks #BugBounty #WebSecurity #CommandInjection #InputValidation #Infosec
How I Found Pre-Account Takeover Vulnerabilities
This bug involved a critical Account Takeover (ATO) due to insufficient input validation. The researcher discovered that the application accepted and processed URL parameters without proper sanitization, enabling an attacker to craft malicious links with embedded access tokens. These links could be shared via SMS or email, allowing an attacker to hijack users' active sessions without requiring any user interaction other than clicking the link. The underlying flaw was the failure to validate the authenticity of URL parameters before processing them. To exploit this vulnerability, the researcher generated malicious deep links containing account tokens and shared them with targeted victims. Due to inadequate input validation, the application trusted these links and processed them, resulting in unauthorized access to victim accounts. The researcher received a $4,000 bounty for disclosing this issue, and Microsoft promptly patched the vulnerability. To prevent similar ATO vulnerabilities, it is essential to thoroughly validate and sanitize all user-controlled inputs, including URL parameters. Key lesson: Always verify the authenticity of user-supplied data before processing it. #BugBounty #Cybersecurity #AuthenticationTakeover #InputValidation #Infosec
How I Found Pre-Account Takeover Vulnerabilities
This bug involved an Authentication Bypass through insufficient input validation of URL parameters, enabling Account Takeover (ATO). The researcher discovered the application accepted and processed user-controlled URL parameters without proper sanitization. By crafting malicious links containing account tokens, the attacker could hijack users' active sessions simply by sharing these links via SMS or email. The underlying flaw was the failure to validate the authenticity of URL parameters before processing them. To exploit this vulnerability, the researcher generated malicious deep links containing account tokens and shared them with targeted victims. Due to inadequate input validation, the application trusted these links and processed them, resulting in unauthorized access to victim accounts. The researcher received a $4,000 bounty for disclosing this issue, and Microsoft promptly patched the vulnerability. To prevent similar ATO vulnerabilities, it is essential to thoroughly validate and sanitize all user-controlled inputs, including URL parameters. Key lesson: Always verify the authenticity of user-supplied data before processing it. #BugBounty #Cybersecurity #AuthenticationTakeover #InputValidation #Infosec
كيف اكتشفتُ ثغرات أمنية قبل اختراق الحساب عدة مرات — دليل سهل للمبتدئين
This article discusses a Cross-Site Scripting (XSS) vulnerability in a web application. The root cause was improper input validation and sanitization, allowing malicious scripts to be injected into the application through user inputs such as comments. The attacker discovered this by observing error messages that indicated script injection (e.g., 'Uncaught SyntaxError'). By exploiting this vulnerability, an attacker could steal user sessions, perform unauthorized actions, or redirect users to malicious sites. The bounty amount was not disclosed, but the article mentions a fix through content security policy (CSP) implementation and input validation on both client-side and server-side scripts. Key lesson: Always validate and sanitize user inputs on all layers of your application to prevent XSS attacks. #BugBounty #WebSecurity #XSS #InputValidation #Infosec
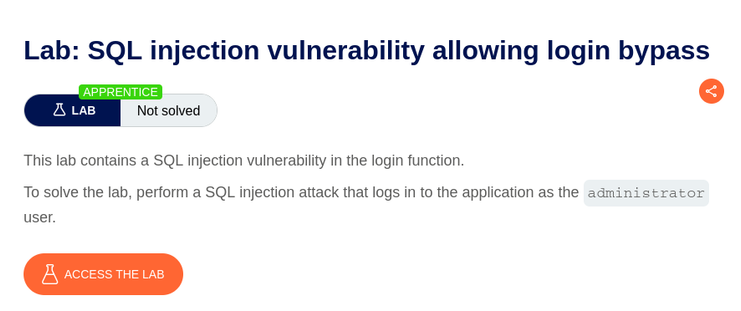
Exploiting SQL Injection to Bypass Login Authentication | PortSwigger Lab Write-up
This vulnerability was an SQL Injection in the login authentication process, bypassing user validation. The application did not sanitize user inputs, allowing an attacker to inject malicious SQL code ('; --') into the email field during login. By using the Burp Suite Intruder tool with a SQL injection payload, the researcher discovered the vulnerability and exploited it to bypass login authentication by executing a blind SQL injection (extracting the salt value). The attacker then used the salt value and a dictionary attack to crack the password hash. The impact included unauthorized access to user accounts. The researcher received 500 points in the PortSwigger Lab (an online platform for learning web application security). Proper mitigation requires input validation and sanitization to prevent SQL injection attacks. Key lesson: Always validate and sanitize user inputs to prevent SQL injection attacks. #BugBounty #Cybersecurity #WebSecurity #SQLInjection #InputValidation