⚠️ HIGH severity: CVE-2026-28761 impacts Fujitsu Musetheque V4 for IPKNOWLEDGE (≤V4L1 rev2203.0). CSRF flaw allows unwanted actions if logged-in users visit malicious pages. Patch status unknown. https://radar.offseq.com/threat/cve-2026-28761-cross-site-request-forgery-csrf-in--3c8966ad #OffSeq #CSRF #Fujitsu #Vuln
⚠️ CRITICAL: CVE-2026-0481 in AMD Instinct™ MI210 (ROCm). Unrestricted IP binding allows remote attackers to modify GPU configs — could cause availability loss. Awaiting mitigation. Details: https://radar.offseq.com/threat/cve-2026-0481-cwe-1327-binding-to-an-unrestricted--12062e2f #OffSeq #AMD #Vuln #ROCm #GPUsecurity
⚠️ CRITICAL vuln: CVE-2026-8511 in Google Chrome (pre-148.0.7778.168) — use-after-free in UI may enable remote sandbox escape via crafted HTML. Patch status unclear. Update ASAP once confirmed! https://radar.offseq.com/threat/cve-2026-8511-use-after-free-in-google-chrome-d050ec47 #OffSeq #Chrome #Infosec #Vuln
CRITICAL: CVE-2026-8580 (CVSS 9.6) — Use after free in Chrome Mojo could enable sandbox escape via HTML. Patch to 148.0.7778.168+ now. No active exploits yet. https://radar.offseq.com/threat/cve-2026-8580-use-after-free-in-google-chrome-1dc444d7 #OffSeq #Chrome #Vuln #PatchTuesday
⚠️ CRITICAL: CVE-2026-44666 in zelon88 HRConvert2 (< 3.3.8) enables OS command injection via unsafe sanitizeString() handling of backtick & tab chars. Patch to 3.3.8 ASAP. Impact: full server compromise possible. Details: https://radar.offseq.com/threat/cve-2026-44666-cwe-78-improper-neutralization-of-s-fac9c425 #OffSeq #Vuln #Infosec
🔥 CRITICAL: Microsoft Authenticator for Android 6.0.0 (CVE-2026-41615) leaks sensitive info to unauthorized actors over the network. Immediate patching required to prevent full compromise. Details: https://radar.offseq.com/threat/cve-2026-41615-cwe-200-exposure-of-sensitive-infor-205e2230 #OffSeq #Microsoft #Android #CVE202641615
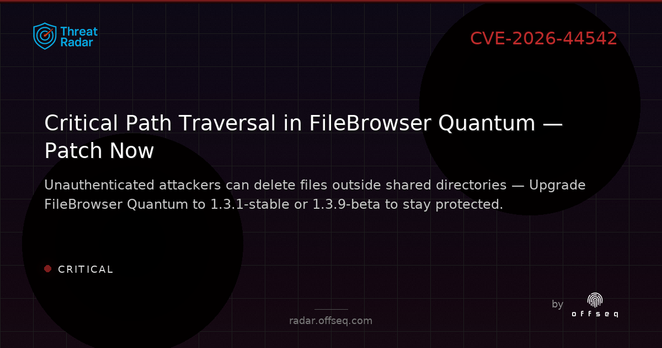
🚨 CRITICAL: CVE-2026-44542 in gtsteffaniak FileBrowser Quantum (<1.3.1-stable, <1.3.9-beta) allows unauthenticated file deletion via path traversal. Upgrade to fixed versions ASAP for protection! https://radar.offseq.com/threat/cve-2026-44542-cwe-22-improper-limitation-of-a-pat-f7d1f33b #OffSeq #vulnerability #FileBrowser #cybersecurity
🚨 CVE-2026-42281: CRITICAL SSRF in MagicMirror² (<2.36.0)! /cors endpoint lets unauthenticated attackers scan internal networks & exfiltrate environment secrets. Upgrade to 2.36.0+ now! https://radar.offseq.com/threat/cve-2026-42281-cwe-918-server-side-request-forgery-3c9e7191 #OffSeq #SSRF #MagicMirror #Vuln
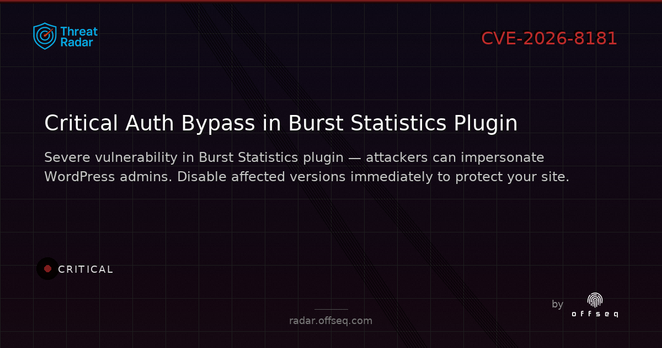
🔴 CVE-2026-8181: Burst Statistics WP plugin (v3.4.0 – 3.4.1.1) suffers CRITICAL auth bypass. Attackers can impersonate admins using any password — immediate removal advised until a fix is released. Details: https://radar.offseq.com/threat/cve-2026-8181-cwe-287-improper-authentication-in-b-c577a44d #OffSeq #WordPress #Vuln
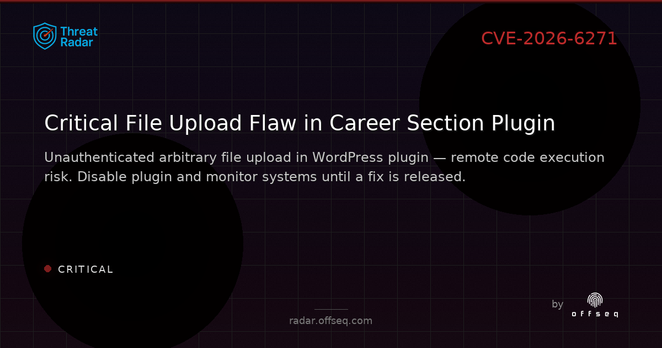
⚠️ CRITICAL: CVE-2026-6271 in shahinurislam Career Section plugin (≤1.7) lets unauthenticated attackers upload dangerous files — risk of remote code execution. Disable plugin immediately & monitor uploads. https://radar.offseq.com/threat/cve-2026-6271-cwe-434-unrestricted-upload-of-file--9fe22087 #OffSeq #WordPress #RCE #Vulnerability