CVE-2026-45211: SQL injection crítica en WooCommerce Square
CVE-2026-45211 WooCommerce SQL injection afecta woosquare ≤4.7.1 con CVSS 8.50. Verificá si tu tienda es vulnerable y actualizá en 5 minutos antes de qu...
https://seguridadenwordpress.com/cve-2026-45211-woocommerce-sql-injection-woosquare/
#cve202645211 #woosquare #sqlinjection #woocommerce #seguridadwordpress
CVE-2026-45211: SQL injection crítica en WooCommerce Square - Seguridad en Wordpress
CVE-2026-45211 es una Blind SQL Injection con CVSS 8.50 en APIExperts Square for WooCommerce ≤4.7.1. Actualizá a 4.7.2 ahora.
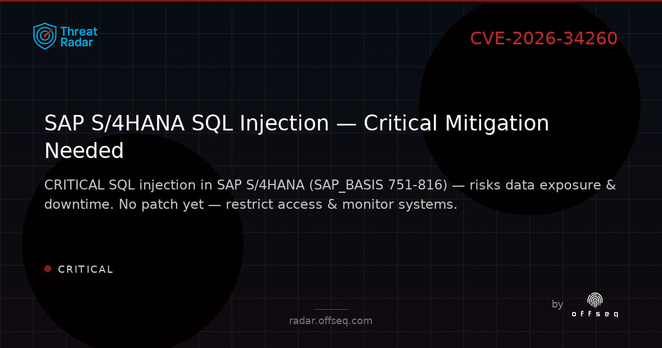
🚨 CRITICAL: SQL injection (CVE-2026-34260, CVSS 9.6) in SAP S/4HANA (SAP_BASIS 751-816). Authenticated attackers can access sensitive data & crash apps. No patch yet — restrict access & monitor logs.
https://radar.offseq.com/threat/cve-2026-34260-cwe-89-improper-neutralization-of-s-4864cd58 #OffSeq #SAP #Infosec #SQLInjectionCVE-2026-2413: SQL injection en plugin Ally afecta 400K
400.000 sitios WordPress expuestos por inyección SQL en plugin Ally de Elementor. ¿Tu versión es 4.0.3 o menor? Actualizá a 4.1.0 en 5 minutos antes de ...
https://seguridadenwordpress.com/inyeccion-sql-wordpress-plugin-ally-cve-2026-2413/
#sqlinjection #cve20262413 #elementor #allyplugin #seguridadwordpress
CVE-2026-2413: SQL injection en plugin Ally afecta 400K - Seguridad en Wordpress
CVE-2026-2413 es una inyección SQL sin autenticación en el plugin Ally para Elementor que expone más de 400.000 sitios WordPress. La corrección está disponible en la versión 4.1.0.
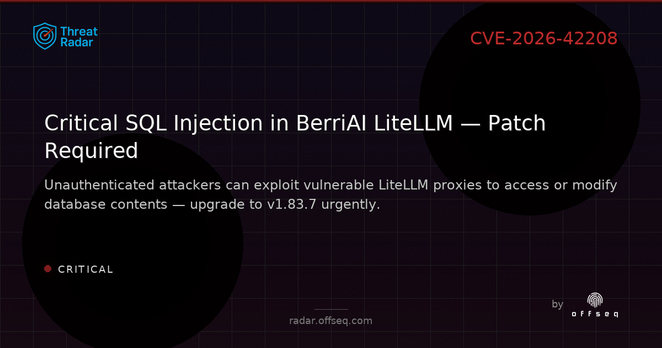
🚨 CRITICAL: CVE-2026-42208 in BerriAI LiteLLM (v1.81.16 – 1.83.6) enables unauthenticated SQL injection via API key processing. Patch to v1.83.7 immediately to protect credentials and data. Details:
https://radar.offseq.com/threat/cve-2026-42208-cwe-89-improper-neutralization-of-s-1213f296 #OffSeq #SQLInjection #Vuln #SecurityCVE-2026-4348: SQL Injection en BetterDocs Pro
¿Usás BetterDocs Pro 3.7.0? La inyección SQL sin autenticación CVE-2026-4348 expone tu base de datos WordPress. Verificá si estás en riesgo y actualizá ...
https://seguridadenwordpress.com/betterdocs-pro-inyeccion-sql-cve-2026-4348/
#betterdocs #sqlinjection #cve20264348 #pluginswordpress #vulnerabilidadwordpress

CVE-2026-4348: SQL Injection en BetterDocs Pro - Seguridad en Wordpress
CVE-2026-4348 afecta a BetterDocs Pro ≤3.7.0: inyección SQL sin autenticación que expone toda la base de datos WordPress. Solución: actualizar a 3.7.1.
JetEngine: SQL injection crítico sin autenticación
¿Usás JetEngine en WordPress? Dos fallas SQL injection sin autenticación exponen tu base de datos. Verificá si tu sitio está afectado y actualizá ya.
https://seguridadenwordpress.com/jetengine-vulnerabilidad-wordpress-sql-injection-cve-2026/
#jetengine #sqlinjection #cve20264662 #crocoblock #wordpressrestapi

JetEngine: SQL injection crítico sin autenticación - Seguridad en Wordpress
CVE-2026-4662 y CVE-2026-4352 afectan JetEngine hasta 3.8.6.1 con inyección SQL no autenticada. Guía de actualización y mitigación.
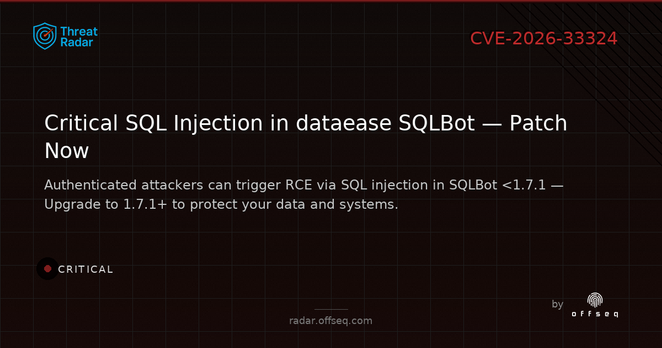
🚨 CRITICAL: dataease SQLBot <1.7.1 (CVE-2026-33324) is vulnerable to SQL injection via prompt injection. Authenticated users can trigger RCE on PostgreSQL. Upgrade to 1.7.1+ now!
https://radar.offseq.com/threat/cve-2026-33324-cwe-89-improper-neutralization-of-s-5605c7fd #OffSeq #SQLInjection #VulnCVE-2026-3359: SQL Injection en Form Maker sin auth
CVE-2026-3359 es una SQL Injection sin autenticación en Form Maker by 10Web (hasta v1.15.42). Actualizá ya y protegé tu base de datos WordPress.
https://seguridadenwordpress.com/cve-2026-3359-sql-injection-form-maker-10web/
#cve20263359 #sqlinjection #formmaker10web #wordpressvulnerabilidad

CVE-2026-3359: SQL Injection en Form Maker sin auth - Seguridad en Wordpress
CVE-2026-3359 permite inyección SQL sin autenticación en Form Maker by 10Web hasta v1.15.42. Cómo parchear y detectar explotación.
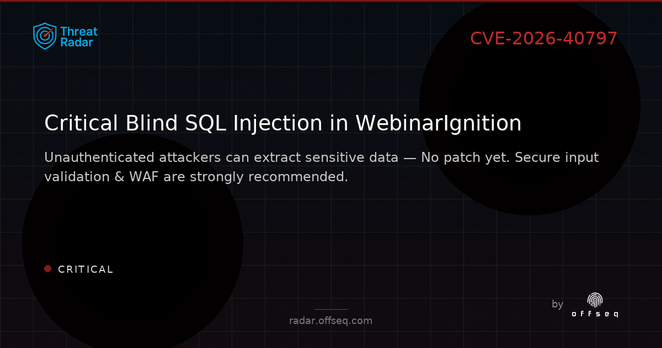
🔴 CRITICAL: CVE-2026-40797 in WebinarIgnition (≤4.08.253) enables unauthenticated Blind SQL Injection. No patch yet — use WAF, validate inputs, restrict DB perms. High confidentiality risk. Details:
https://radar.offseq.com/threat/cve-2026-40797-cwe-89-improper-neutralization-of-s-1958ecd4 #OffSeq #SQLInjection #WebinarIgnitionOh, another groundbreaking article promising to unravel Intel's secret
#voodoo memory
#tech, only to be thwarted by the mighty
#Cloudflare shield. 🤦♂️ Because who needs cutting-edge insights when you can play "Guess the SQL Injection"? 🚀💻
https://www.hpcwire.com/2026/02/05/what-is-z-angle-memory-and-why-is-intel-developing-it/ #Intel #SQLInjection #TechNews #HackerNews #ngated
What Is Z-Angle Memory and Why Is Intel Developing It? - HPCwire
Intel announced this week that it’s working with SoftBank subsidiary SAIMEMORY to commercialize Z-Angle Memory (ZAM), an advanced type of DRAM that stacks memory modules vertically. While ZAM chips aren’t expected to become available for at least three years, they could eventually replace the high-bandwidth memory (HBM) that is in such high demand today thanks […]