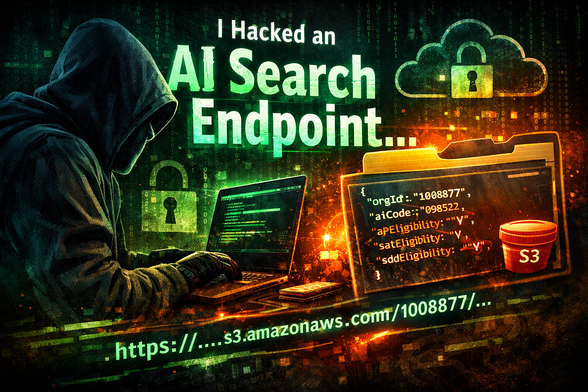
How I Turned an AI Search Endpoint into an Internal Org Intel Leak
This vulnerability was an authentication bypass and data leak involving an AI search endpoint acting as an oracle. The application failed to implement rate limiting, exposing presigned AWS S3 URLs without authentication to clients. Bypassed rate limits and enumerated valid prefixes, the researcher discovered a blueprint containing internal organization IDs, program eligibility logic, operational flags, system behavior hints—essentially a comprehensive system map. The researcher proposed adding strict rate limiting, revoking all existing presigned URLs, proxying requests through the backend, returning only necessary fields, sanitizing S3 payloads, removing internal metadata fields, adding logging and anomaly detection for enumeration patterns as mitigation measures. Key lesson: Combinations of seemingly minor flaws can lead to scalable vulnerabilities that provide a detailed system map #BugBounty #WebSecurity #DataLeak #APISecurity #RateLimiting
https://medium.com/@shxsu1/how-i-turned-an-ai-search-endpoint-into-an-internal-org-intel-leak-72ce87f61948?source=rss