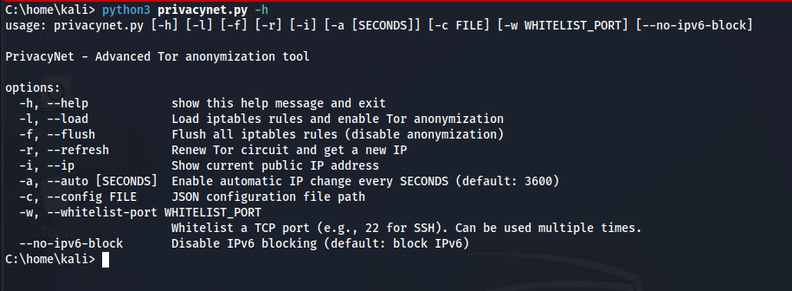
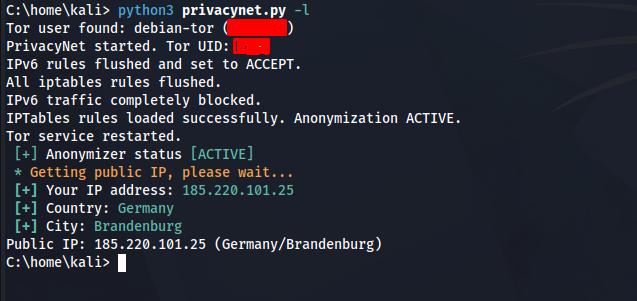
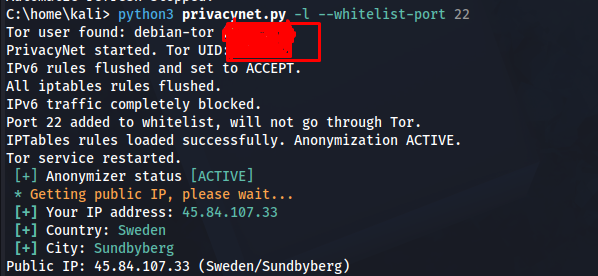
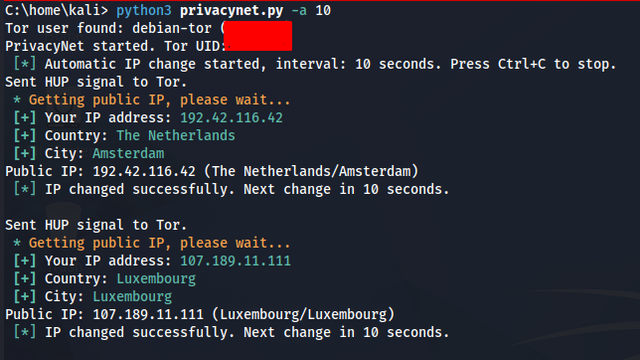
PrivacyNet - Open-source transparent Tor anonymizer for your entire system. Forces all TCP traffic through Tor using iptables.
https://github.com/HalilDeniz/PrivacyNet/ #privacy #tor #linux
Reading about cybersecurity and doing cybersecurity are two completely different things.
You can memorize every concept and still freeze when faced with a real system. Knowledge without practice is just theory.
Vulnerable VMs fix that. Platforms like VulnHub and VulNyx put you in controlled environments where you can break things, fail, and learn why without consequences.
Cybersecurity training platforms give both red and blue teams a safe place to practice real-world scenarios, from exploiting vulnerabilities to detecting, investigating, and responding to attacks
Here are popular online cybersecurity training platforms and their pricing options 😎👇
Find high-res pdf ebooks with all my cybersecurity related infographics at https://study-notes.org
#cybersecurity #cybersecuritytraining #blueteam #infosec #pentesting
What does a Pentester in Dubai do?
They simulate real cyberattacks to uncover vulnerabilities in your web apps, APIs, networks, and cloud systems—before attackers do.
That’s why businesses invest in proactive VAPT Services in Dubai.
🌐 www.vaptsecurity.com
Spoofing attacks manipulate identity or trust signals across network layers to deceive systems and redirect or disrupt legitimate communication.
Here are different types of spoofing attacks across OSI layers 😎👇
Find high-res pdf ebooks with all my cybersecurity infographics at https://study-notes.org
#cybersecurity #infosec #pentesting #informationsecurity #ethicalhacker
Die größten Unterschiede liegen nicht in den Tools, sondern im Mindset:
🔹 OPSEC first – Jede Aktion wird hinterfragt: Welche Spuren hinterlasse ich? Wie reagiert der Verteidiger?
🔹 Realismus vor Geschwindigkeit – Es geht nicht darum, möglichst schnell ans Ziel zu kommen, sondern einen echten Angreifer abzubilden.
🔹 Kontinuierliches Lernen – Standard-Tools werden zunehmend erkannt. Wer sich nicht weiterentwickelt, wird sichtbar.
🔹 Fehler als Lernmoment – Der Moment, in dem man erkannt wird, verändert die eigene Denkweise nachhaltig.
In unserem neuen Blogartikel beschreibt Marcel Heisel, wie wir neue Mitarbeitende auf genau diesen Wechsel vorbereiten – und was dabei wirklich den Unterschied macht.
👉 https://research.hisolutions.com/2026/05/vom-pentester-zum-red-teamer-wie-wir-neue-mitarbeitende-fit-machen/
#RedTeaming #Pentesting #CyberSecurity #OffensiveSecurity #OPSEC #InfoSec #ActiveDirectory
It was finally time to make use of some stickers.
Working through the HTB Windows PrivEsc module I keep drowning in edge cases.
I tried to distill what actually matters when you're starting out/ preparing for a cert, e.g.:
SeImpersonate → SYSTEM in one tool call. DnsAdmins → malicious DNS DLL. Server Operators → service binary hijack. And always whoami /all, not just whoami /priv.
Full walkthrough + real shell output:
niklas-heringer.com/skills-lab/windows-privilege-escalation-02-privesc-paths/
I put together a PoC for a boot manager downgrade attack against BitLocker, building on Microsoft STORM's BitUnlocker research (CVE-2025-48804). Simpler to pull off than Bitpixie in most cases.
The push for TPM+PIN enforcement and SVN-based revocation shall continue!
Repo: https://github.com/garatc/BitUnlocker
All credit to Microsoft STORM for the original research
#BitLocker #infosec #pentesting #WindowsSecurity #physicalaccess