Investigation scenario:
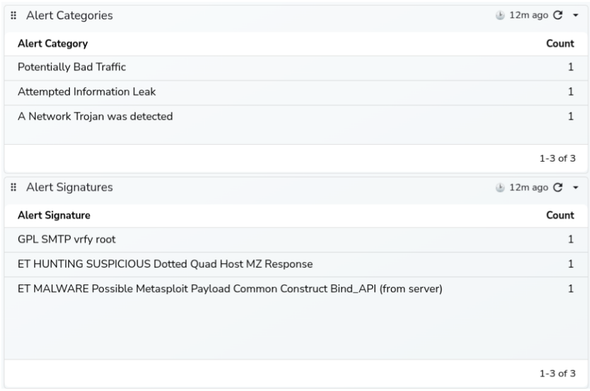
We just received three notifications with alerts from #Suricata #IDS
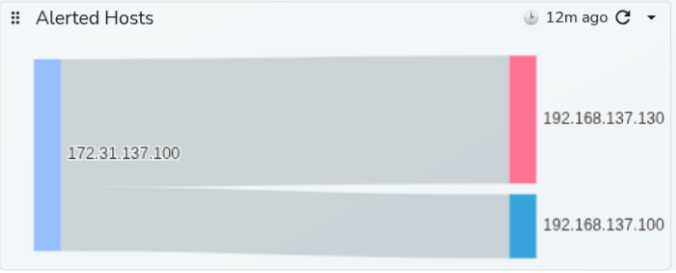
1) GPL SMTP vrfy root, from unknown IP to our mailserver
Shortly after that, two more alerts appeared:
2) ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response; from the same unknown IP to Windows computer in our network
3) ET MALWARE Possible Metasploit Payload Common Construct Bind_API, again from the same unknown IP to the same Windows computer
What happened?
What to do? How to analyze network traffic and investigate those alerts?
We do not have any EDR or XDR installed on that Windows computer. Right now,we have only Suricata eve.json logs ingested to the #OpenObserve #SIEM
If you would like to see more, you are welcome to attend my @suricata webinar on March 11.
Register here: https://us02web.zoom.us/webinar/register/WN_I6BNbCU2SNG2fAOEiotPiQ