🔥 Q1 2026 Cyber Risk report by #ANYRUN is out!
Explore the cyber risks and threat shifts for CISOs, including:
❗️ +14.7% credential theft
❗️ +98.3% loader attacks
❗️ +58.4% LOLBAS attacks
Turn Q1 intel into Q2 security priorities. Get the report: https://any.run/cybersecurity-blog/cyber-risk-report-q1-2026/?utm_source=mastodon&utm_medium=post&utm_campaign=cyber_risk_report_q1_2026&utm_content=linktoreport&utm_term=040626
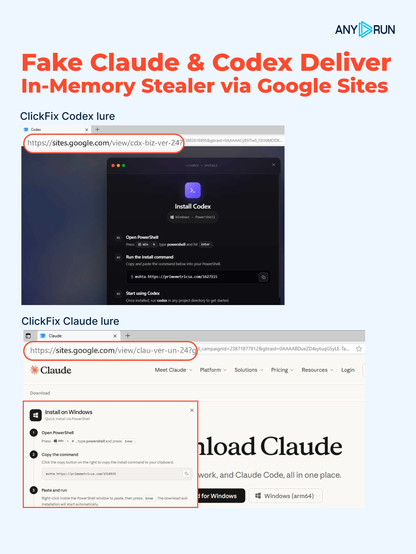
🚨 𝗙𝗮𝗸𝗲 𝗖𝗹𝗮𝘂𝗱𝗲 & 𝗖𝗼𝗱𝗲𝘅 𝗗𝗲𝗹𝗶𝘃𝗲𝗿 𝗜𝗻-𝗠𝗲𝗺𝗼𝗿𝘆 𝗦𝘁𝗲𝗮𝗹𝗲𝗿: 𝗖𝗹𝗶𝗰𝗸𝗙𝗶𝘅 𝘃𝗶𝗮 𝗚𝗼𝗼𝗴𝗹𝗲 𝗦𝗶𝘁𝗲𝘀
⚠️ We’re tracking a #ClickFix campaign that mimics popular AI tools, including Codex and Claude, and abuses trusted Google Sites infrastructure to deliver stealer #malware.
With no standalone executable dropped to disk and network activity appearing as legitimate powershell.exe traffic, the attack can significantly reduce visibility during the early stages of compromise.
❗️ Victims are directed to trusted sites[.]google[.]com pages and instructed to execute an mshta command. The attack results in in-memory stealer execution, theft of browser, email, and cryptocurrency wallet data, and outbound communication with attacker-controlled C2 infrastructure, while leaving fewer traditional detection opportunities for SOC teams.
Execution chain:
Trusted Google Sites lure ➡️ User-executed mshta command ➡️ Multi-stage PowerShell delivery ➡️ Steganographic payload extraction from image ➡️ Shellcode deployment ➡️ In-memory execution inside powershell.exe ➡️ Browser, email & wallet data theft ➡️ C2 exfiltration
👨💻 Using #ANYRUN Sandbox, investigate the full ClickFix execution chain, validate detection coverage, and observe PowerShell staging, steganographic payload delivery, and credential theft activity. Explore the analysis sessions and collect IOCs:
🔹 Codex lure: https://app.any.run/tasks/151cfb30-5ef2-4962-a90e-58a59ecc43da/?utm_source=mastodon&utm_medium=post&utm_campaign=claude_codex_clickfix&utm_term=030626&utm_content=linktoservice
🔹 Claude lure: https://app.any.run/tasks/698e0bd5-01b6-40fe-814c-5c0885cea645/?utm_source=mastodon&utm_medium=post&utm_campaign=claude_codex_clickfix&utm_term=030626&utm_content=linktoservice
🔍 Track related ClickFix activity in #ANYRUN TI Lookup, identify additional Codex and Claude lures, and uncover related AI-themed ClickFix activity and infrastructure:
🔹 https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=claude_codex_clickfix&utm_content=030626&utm_term=linktotilookup#%7B%2522query%2522:%2522url:%255C%2522https:/sites.google.com/*/cdx%255C%2522%2520or%2520url:%255C%2522https:/sites.google.com/*/clau%255C%2522%2522,%2522dateRange%2522:7%7D
🔹 https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=claude_codex_clickfix&utm_content=030626&utm_term=linktotilookup#%7B%22query%22:%22ruleName:%5C%22AI-themed%20ClickFix%20phishing%20page%20has%20been%20detected%5C%22%22,%22dateRange%22:14%7D
🚀 Equip your SOC with stronger phishing detection and contain incidents faster: https://any.run/enterprise/?utm_source=mastodon&utm_medium=post&utm_campaign=claude_codex_clickfix&utm_term=030626&utm_content=linktoenterprise
⚡ Faster SOC decisions and stronger threat visibility with #ANYRUN’s May updates.
Explore Tier 1 Reports, Elastic Security integration for fresh IOCs, and 1,400+ new detections 🛡️
Learn more and strengthen your SOC response now 👇
https://any.run/cybersecurity-blog/release-notes-may-2026/?utm_source=mastodon&utm_medium=post&utm_campaign=release-notes-may-2026&utm_term=030626&utm_content=linktoblog
Day 1 at Infosecurity Europe 2026 is a wrap 🇬🇧 One theme kept coming up in conversations with security leaders today: investigation speed matters, but decision confidence matters even more.
We're showing how #ANYRUN helps enterprise SOCs & MSSPs shorten time to insight while giving teams the context needed to make faster, more confident response decisions ⚡️
📍 Find our team at Stand C62 and learn how behavioral analysis and live threat intelligence help reduce uncertainty throughout the investigation process.
🎟️ Get your ticket: https://infosecurityeurope.com/en-gb/register.html?code=1666079269821849-VCP
🚨 𝗝𝗢𝗠𝗔𝗡𝗚𝗬 𝗪𝗲𝗯𝘀𝗵𝗲𝗹𝗹 𝗘𝗻𝗮𝗯𝗹𝗲𝘀 𝗟𝗼𝗻𝗴-𝗧𝗲𝗿𝗺 𝗖𝗼𝗺𝗽𝗿𝗼𝗺𝗶𝘀𝗲 𝗼𝗳 𝗩𝗼𝗜𝗣 𝗜𝗻𝗳𝗿𝗮𝘀𝘁𝗿𝘂𝗰𝘁𝘂𝗿𝗲
⚠️ #JOMANGY is an actively used PHP backdoor targeting FreePBX-based VoIP environments with stealth, self-recovery, and VoIP/SIP abuse capabilities.
Once deployed, it establishes persistent access, creates hidden root accounts, and abuses Asterisk/SIP services for toll fraud operations. Since VoIP systems are deeply integrated into enterprise environments, delayed detection can lead to prolonged unauthorized access, financial loss, and operational disruption.
❗️ The malware relies on stealth and defense-evasion techniques designed to survive cleanup attempts and complicate containment for SOC and IR teams once systems are compromised. MITRE ATT&CK techniques observed include:
🔹 𝗣𝗲𝗿𝘀𝗶𝘀𝘁𝗲𝗻𝗰𝗲 via Cron jobs and Unix shell configuration abuse
🔹 𝗗𝗲𝗳𝗲𝗻𝘀𝗲 𝗲𝘃𝗮𝘀𝗶𝗼𝗻 through log clearing, timestomping, and firewall modification
🔹 𝗖𝗿𝗲𝗱𝗲𝗻𝘁𝗶𝗮𝗹 𝗮𝗰𝗰𝗲𝘀𝘀 targeting `/etc/passwd` and `/etc/shadow`
🔹 𝗖𝗼𝗺𝗽𝗲𝘁𝗶𝘁𝗶𝘃𝗲 𝗲𝘃𝗶𝗰𝘁𝗶𝗼𝗻 of other webshells from compromised systems
🔹 𝗩𝗼𝗜𝗣/𝗦𝗜𝗣 𝗮𝗯𝘂𝘀𝗲 supporting toll fraud operations
Execution chain:
Vulnerable FreePBX instance ➡️ Exploit public vulnerabilities ➡️ Bash stager deployment ➡️ JOMANGY webshell deployment ➡️ Multiple persistence mechanisms ➡️ Self-healing loop ➡️ VoIP/SIP abuse
👨💻 Using #ANYRUN Sandbox, investigate JOMANGY behavior in real time, validate detection coverage, and observe webshell deployment, persistence mechanisms, and outbound C2 activity: https://app.any.run/tasks/6c779f0e-e422-4ef5-9bc7-6a799480cc20/?utm_source=mastodon&utm_medium=post&utm_campaign=jomangy_webshell&utm_content=linktoservice&utm_term=280526
Earlier visibility into persistence and webshell behavior helps SOC teams accelerate containment and reduce attacker dwell time. IOCs in the comments 💬
🔍 #ANYRUN TI Lookup reveals two active JOMANGY infrastructure clusters tied to attacker-controlled C2 servers, with activity traced back to April 2026. This visibility helps threat hunters uncover related activity, identify compromised environments, and track infrastructure reuse across campaigns: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=jomangy_webshell&utm_content=linktotilookup&utm_term=280526#%7B%2522query%2522:%2522destinationIP:%255C%2522160.119.69.4%255C%2522%2520OR%2520destinationIP:%255C%252245.95.147.178%255C%2522%2522,%2522dateRange%2522:180%7D
🚀 Scale your SOC’s triage and response with solutions trusted by 74 Fortune 100 companies and detect business risks earlier. Get an exclusive 10th anniversary deal for your team: https://app.any.run/plans/?utm_source=mastodon&utm_medium=post&utm_campaign=jomangy_webshell&utm_content=linktoplans&utm_term=280526
⚡ Connect #ANYRUN with your SIEM, SOAR, or EDR, and make triage faster, response sharper, and threat hunting deeper, without disruption.
🎯 Maximize your security stack performance with special deals: https://any.run/plans/?utm_source=mastodon&utm_medium=post&utm_campaign=integrations_and_connectors&utm_term=280526&utm_content=linktoplans
Find your vendor: https://any.run/integrations/?utm_source=mastodon&utm_medium=post&utm_campaign=integrations_and_connectors&utm_term=280526&utm_content=linktointegrations
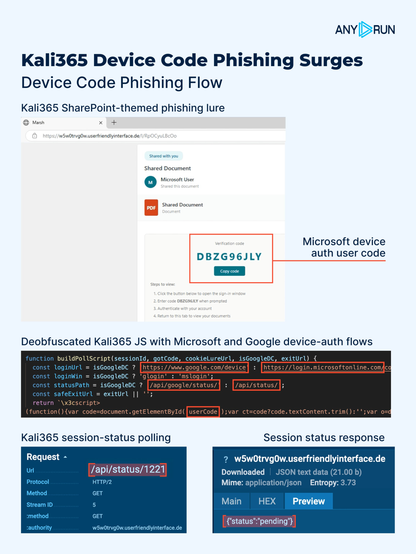
🚨 #𝗞𝗮𝗹𝗶𝟯𝟲𝟱 𝗔𝗰𝘁𝗶𝘃𝗶𝘁𝘆 𝗦𝘂𝗿𝗴𝗲𝘀: 𝗗𝗲𝘃𝗶𝗰𝗲 𝗖𝗼𝗱𝗲 𝗣𝗵𝗶𝘀𝗵𝗶𝗻𝗴 𝗜𝘀 𝗦𝗰𝗮𝗹𝗶𝗻𝗴 𝗙𝗮𝘀𝘁
We’re seeing a growing Device Code #phishing activity, with Kali365 emerging as one of the most active PhaaS. In the last 24 hours alone, #ANYRUN recorded 100+ related analysis sessions.
⚠️ The attack abuses legitimate Microsoft device authentication flows. Victims are shown a user code and instructed to enter it into a real Microsoft device auth page, allowing attackers to capture OAuth access tokens instead of passwords. The risk shifts from credential theft to token abuse, while significantly reducing the number of traditional phishing indicators typically used for detection and triage.
❗️ Deobfuscated Kali365 JavaScript revealed that after a verification gate, the lure deploys a phishing page, launches a legitimate Microsoft device authentication flow, and then polls /api/status/<session_id> for session states such as captured, expired, and declined.
📌 The code also contains lure-template generators for OneDrive, SharePoint, Teams, Outlook, and Voicemail, and a separate Google device-code authentication flow.
⚡️ #ANYRUN lets analysts safely reconstruct the flow, validate suspicious OAuth activity faster, and identify related phishing infrastructure before campaigns scale further, helping SOC teams reduce investigation time, improve detection accuracy, and lower MTTR.
👨💻 See the full phishing flow, validate detection logic, and collect #IOCs: https://app.any.run/tasks/d078f430-c3cc-44e8-a809-5506205049c3?utm_source=mastodon&utm_medium=post&utm_campaign=kali365_activity_surges&utm_content=linktoservice&utm_term=270526
🔍 Track Kali365 activity using this TI Lookup search query: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=kali365_activity_surges&utm_content=linktotilookup&utm_term=270526#%7B%2522query%2522:%2522threatName:%255C%2522kali365%255C%2522%2522,%2522dateRange%2522:7%7D%20
🚀 Scale your SOC’s triage and response with solutions trusted by 74 Fortune 100 companies and detect business risks earlier. Get an exclusive 10th anniversary deal for your team: https://app.any.run/plans/?utm_source=mastodon&utm_medium=post&utm_campaign=kali365_activity_surges&utm_content=linktoplans&utm_term=270526
🚀 10 years ago, #ANYRUN started as one analyst’s attempt to make malware analysis faster.
Today, 10,000+ companies use it daily.
⚡️ Read an exclusive interview with CEO Aleksey Lapshin on growth, AI, and why human expertise still matters: https://any.run/cybersecurity-blog/ceo-interview-anyrun-10-years/?utm_source=mastodon&utm_medium=post&utm_campaign=ceo_interview_anyrun_10_years&utm_content=linktoblog&utm_term=270526
What an amazing time at CONFidence 2026 🇵🇱
Big thanks to the cybersecurity professionals who stopped by our stand, joined a demo, and shared their SOC challenges 🙌
⚡️ The conversations don’t stop here. Explore how #ANYRUN supports SOC workflows: https://any.run/enterprise/?utm_source=mastodon&utm_medium=post&utm_campaign=confidence&utm_content=linktoenterprise&utm_term=270526