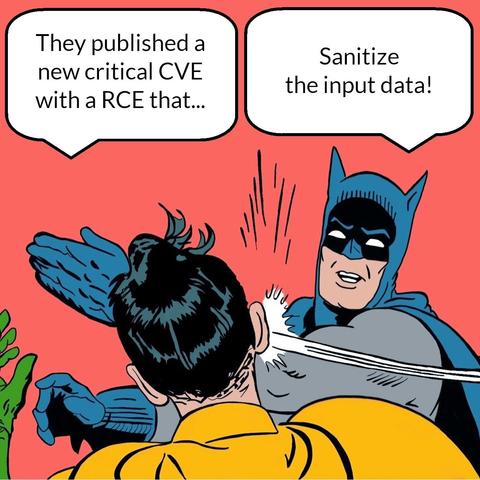
#fridayrant! Happy friday everyone, and here's this week's rant.
Speaking with a friend and colleague who sends me systematically #CVEs and fresh of the day #exploits, we had an argument (always a pleasure to have one btw) about #data #validation and other #cybersecurity issues.
My exact comment for this CVE (a #rabbitmq code injection) was: "if you don't sanitize your input and pass it to your application based on belief, you deserve the #code #injection".
Seriously, let's make a clear statement: how many #APIs do sanitize their input data? One of the very best answers I ever got was "but the data is sanitized on the client side"
Well, spoiler alert: nope. That's not gonna happen.
This problem is nothing new, truly: it's something I've been discussing since the early 2000s (actually after one the very first applications I made was so badly injected I still remember it to this day).
There is no such thing as "client side data sanitization".
You control everything coming to your application.
There is no such thing as "the #framework automagically solves this issue". You either know it or not. And if you use a framework, you probably have a legacy issue. Or will have one.
At the end of the day, #data is your main #asset and it provides value to your business and decisions.
Businesses stopped developing #software to solve problems, and often it sounds like arguing about divinities or alchemy.
It's a tool, not a magic wand.
But "any sufficiently advanced technology is indistinguishable from magic". So... are you a developer, or a believer?