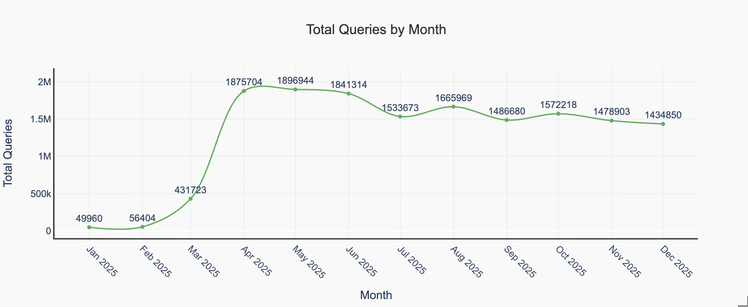
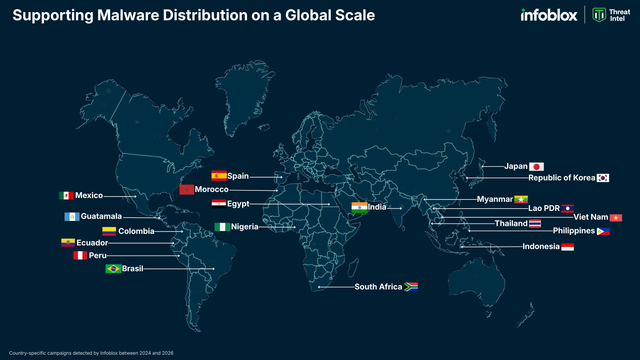
Send an SMS to confirm you're a human? That's strange. How about dozens of SMS, to locations all over the world? That sounds more like a hot take on International Revenue Share Fraud (IRSF). Infoblox Threat Intel has come across an operation that defrauds both individuals and telecoms by way of social engineering victims through the use of a fake CAPTCHA process.
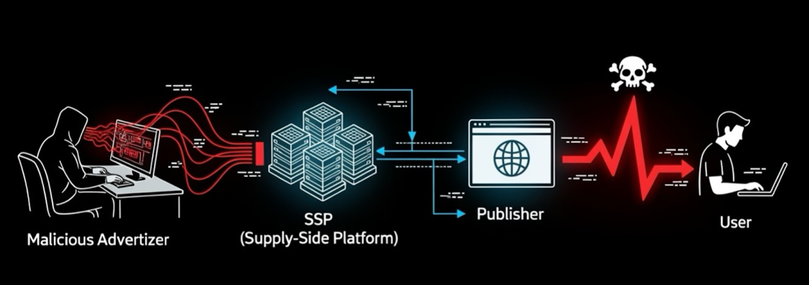
With IRSF, fraudsters generate their revenue by driving call or SMS traffic to numbers to which they have revenue sharing agreements with the local telecoms. Historically, this has been done by methods like hacking an organization's PBX system, or using bots to abuse services that generate one-time-passwords, and directing that call or SMS traffic to numbers under their control.
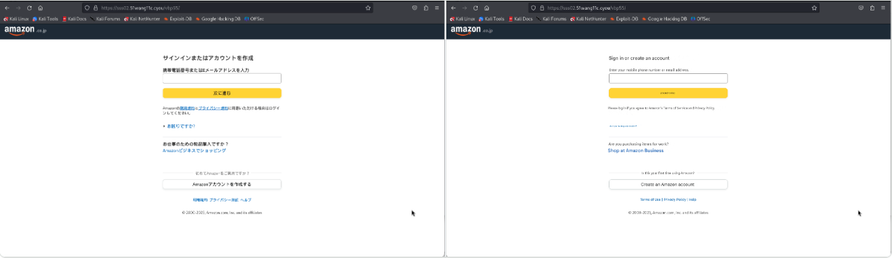
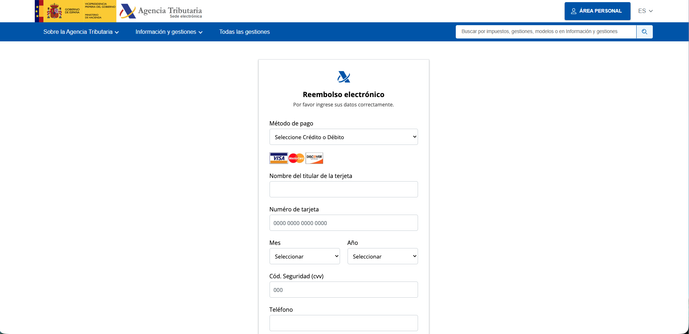
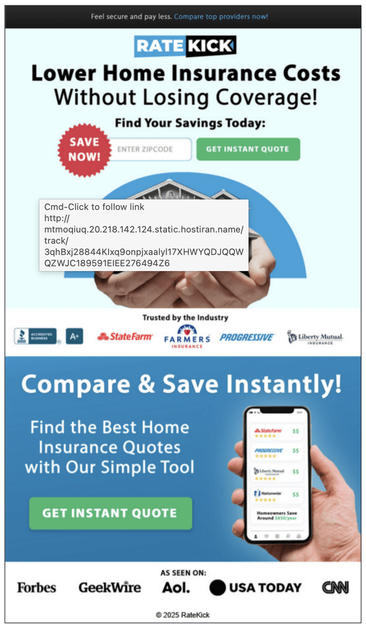
This operation, however, takes advantage of individuals' familiarity with the CAPTCHA process, by adding a multi-stage requirement to send bulk SMS to get access to games, videos, or adult content - because of course, these things are so hard to access online otherwise.
In this case, the victims are two-fold. First, it impacts the people who get unexpected international SMS charges on their bill, and then the telecoms who both pay termination fees to the international destinations telecom, and who also possibly absorb the cost of the chargeback.
Read more about our investigation into this new flavour of scam, including the specific domains and infrastructure we uncovered, here: https://www.infoblox.com/blog/threat-intelligence/hold-the-phone-international-revenue-share-fraud-driven-by-fake-captchas/
#threatintel #cybercrime #threatintelligence #cybersecurity #infosec #infoblox #infobloxthreatintel #scam #phishing #IRSF #telecom #captcha