⚽ Threat actors are warming up for the 2026 World Cup—and they’re targeting fans early.
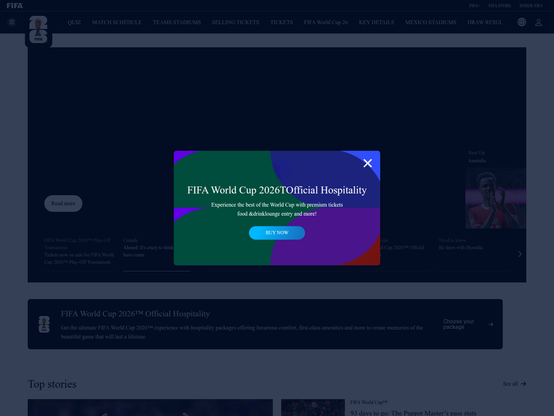
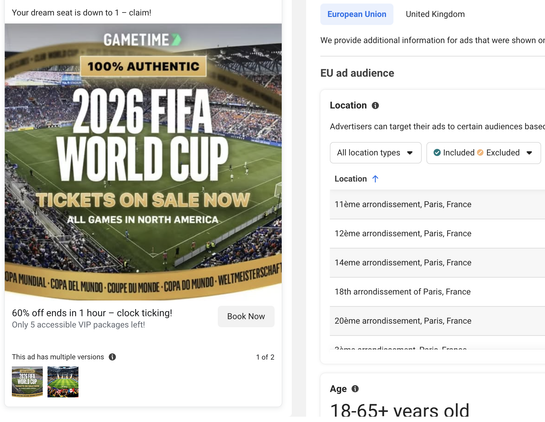
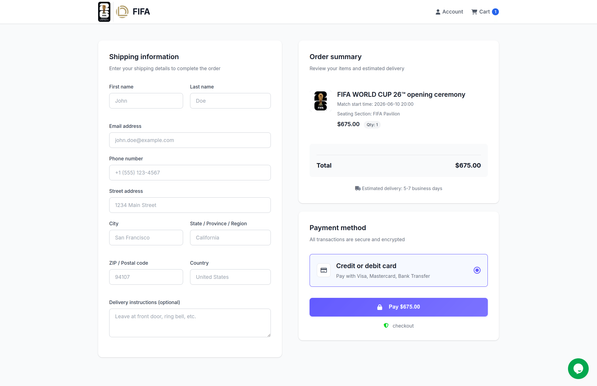
We’ve observed FIFA ticket phishing pages on domains such as fifa[.]bio and ww-fifa[.]com, distributed through malicious spam emails and Facebook ad campaigns. These sites prompt a bogus FIFA ID login to purchase tickets, then transition to a checkout flow collecting personal and payment information.
Payment flows redirect to actor-controlled domains (pay[.]fifa-com[.]com) or Stripe checkout pages with inconsistent merchants (we observed some with suspicious Romanian LLC names).
These recently-registered domains are mostly Cloudflare-hosted, spread across various TLDs, and consistently abuse FIFA branding. If it’s a suspicious domain in your inbox or feed, assume it’s not official. 🛑 ⚽
Domain sample: fifa-2026[.]homes, fifa-com[.]media, www-fifa-com[.]website, vvww-fifa[.]com, fifa-26-worldcup[.]com
#dns #infoblox #infobloxthreatintel #threatintel #threatintelligence #cybercrime #cybersecurity #FIFA #WorldCup2026 #phishing #scam #lookalikes