We planned one report on Keitaro abuse, but we ran out of pages before we ran out of cases.
So here’s Part 2 of 3, a medley of threats that go well beyond AI‑investment scams.
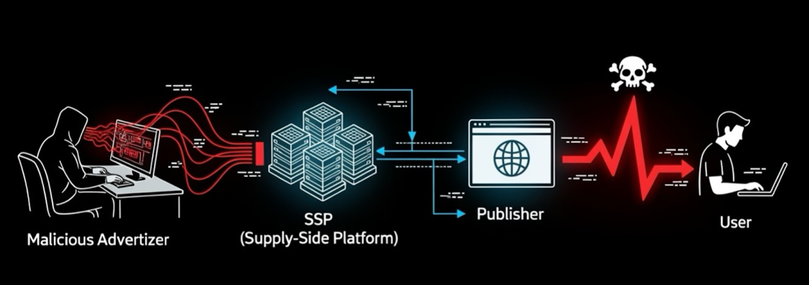
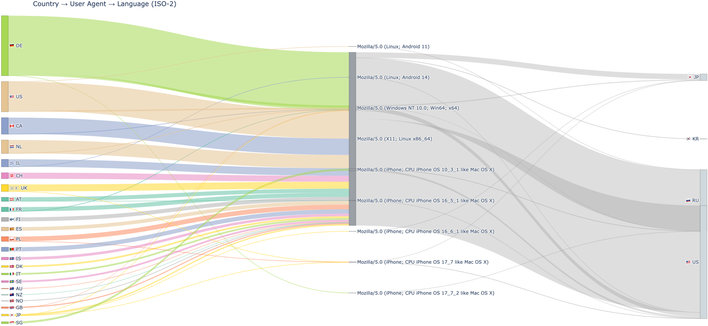
Threat actors abuse Keitaro’s traffic distribution, cloaking, and rule engine to hide malicious landing pages behind geo and device-based filters. They stack bulletproof hosting and reverse proxies to add layers of indirection, making takedown and analysis harder. In this post, we share how we overcame this using multi‑protocol, multi‑vantage telemetry. We leveraged JA4+ web server fingerprints, DNS analytics, and Confiant’s visibility into advertising supply chain data to uncover Keitaro abuse and the delivery of malware downloaders, infostealers, weaponized RMMs, wallet drainer campaigns, scams, and email spam and advertising attack vectors.
If you hunt threats distributed via adtech, these indicators can be useful pivots. https://www.infoblox.com/blog/threat-intelligence/no-reach-no-risk-the-keitaro-abuse-in-modern-cybercrime-distribution/
#dns #threatintel #threatintelligence #cybercrime #cybersecurity #infosec #infoblox #infobloxthreatintel #scam #ai #keitaro #adtech #tds #trafficdistributionsystem #cloaker #cloaking #landscape #malvertising #infostealer #rmm #remotemonitoringmanagement #downloader #malware #spam #airdrop #cryptocurrency #ja4 #ja4_fingerprinting