TCS have been linked to the Marks and Spencer breach, at least in part.
The NCA has confirmed on the record that the investigation into the M&S and Co-op hack is focused on English teenagers. I could toot the names of the people I think they’ll pick up, but won’t.
TCS has a security incident running around the M&S breach.
Interestingly the source claims TCS aren't involved in Co-op's IT - which is categorically false, they took over most of it while I worked there, including the helpdesk, and my team (SecOps) after I left.
https://www.ft.com/content/c658645d-289d-49ee-bc1d-241c651516b0
Insurance Insider say Co-op Group have no cyber insurance policy.
It’s got the insurance industry hard as they think they can ambulance chase other orgs with it.
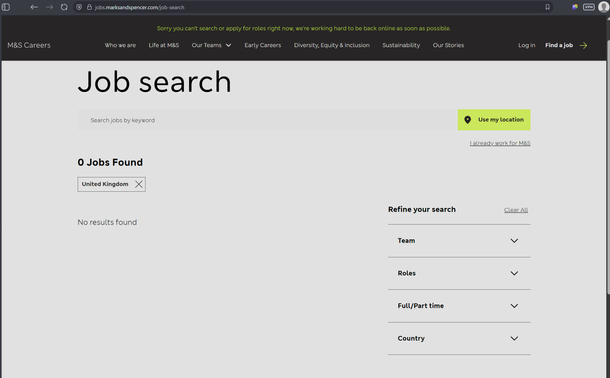
While Co-op have restored every customer facing system and internal systems like recruitment and remote working, M&S still don't even have recruitment back.
I'm reliably told they paid the ransom, so they'll be target #1 basically forever with other ransomware groups now due to resiliency woes and willingness to pay.
https://www.bbc.co.uk/news/articles/c23mz5eg091o
This Daily Mail piece about security leaders thinking work-from-home means they will be crippled is horseshit, I'm not linking it.
They've taken a survey about how security people think their businesses couldn't survive ransomware, and linked it to working from home. WFH isn't the problem: business IT and resilience being built on quicksand is the problem.
Sounds like their companies rely on a hard outer shell and a squishy inside defense and nearly no layers of security.
@GossiTheDog Looks like a product of the "a good lie contains as much truth as possible" school.
The connection to WFH is spurious; but only two thirds sounds low for "We don't really understand our problems; but they are probably apocalyptic".
@GossiTheDog The 'WFH' allegations seem in especially bad faith given the suspected entry point for the M&S compromise: the outsourced helpdesk.
Those guys are even more compliant labor than work-not-from-home employees, so the Daily Heil isn't going to say anything; but lack even the (informal; but in practice often at least reasonably effective) "does the IT person you just poked recognize who is interrupting with a password question?" ID verification step with onsite workers and onsite IT.
It wouldn't be the whole story either, but it's just as true.
@ftp_alun @GossiTheDog There are also the organizations where basically everyone is 'remote' relative to the cloud stuff that is what actually matters and will either be fine or irrecoverably paved depending on how you configured it and whether or not the AWS/Azure admin creds got compromised.
Endpoints are high hassle per unit change; and nobody staffs IT such that they can replace or reimage them all at once; but unless it's really the dark ages just swapping or paving is usually fine.
@GossiTheDog wasn't there some event, maybe 5 years ago, that meant a lot of WFH? Or did I hallucinate those times.
Is it suddenly a problem now or this is the same RTO bullshit being peddled?
Marks and Spencer abandoned my city to take themselves out in the sticks where the only way to get to them from here, is by car, so I have abandoned Marks and Spencer's, they have nothing really original anyway.
Take something from the shelf and when you reach the checkout, it costs twice as much! Nice!
Which in the UK would be a criminal offence (under the law as it currently stands).
@GossiTheDog Want to guess how much of my IT leadership career has been focused on building in-house expertise and dialing back the presence of MSPs?
Enough that it's made for a pretty good living...
@GossiTheDog when I got my business degree, one of my management profs said that the instant you outsource, you give up control. To the service provider, you move from income to liability on the balance sheet because you now are costing them money, and to eke out any profit they need to cut costs related to providing service to you.
Thus you get all this *gestures vaguely*




 🇺🇦
🇺🇦