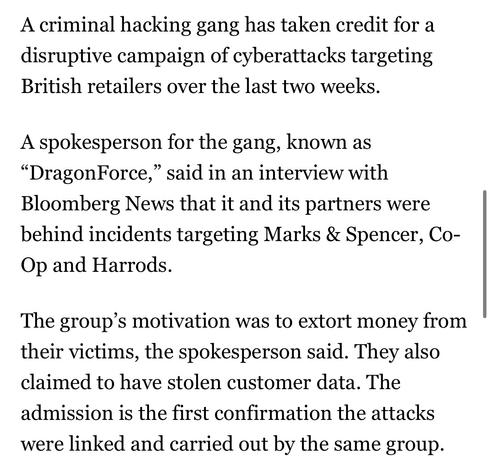
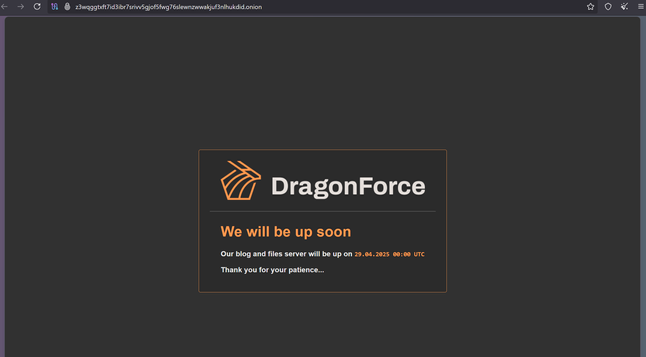
DragonForce Ransomware Cartel are claiming credit for attacks on Marks and Spencer, Co-op and Harrods and say more victim orgs are coming https://www.bloomberg.com/news/articles/2025-05-02/-dragonforce-hacking-gang-takes-credit-for-uk-retail-attacks
I'm going to make this the new ongoing megathread for DragonForce Ransomware Cartel's attack on UK retailers as they're all connected.
Why it matters: these are some of the UK's largest retailers, think Target or some such in a US sense.
Prior threads
M&S: https://cyberplace.social/@GossiTheDog/114381946765071799
Co-op: https://cyberplace.social/@GossiTheDog/114426688834113446
Harrods:
https://cyberplace.social/@GossiTheDog/114433519351165250
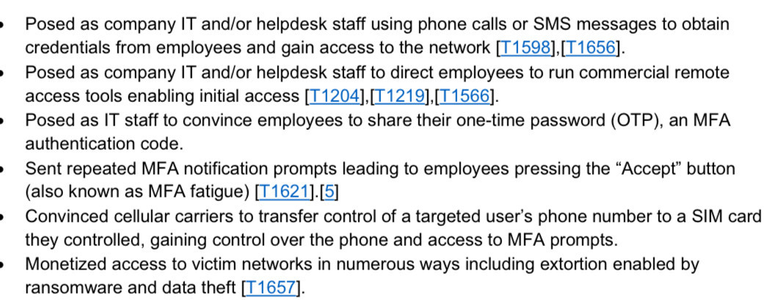
The individuals operating under the DragonForce banner are using social engineering for entry.
Defenders should urgently make sure they have read the CISA briefs on Scattered Spider and LAPSUS$ as it's a repeat of the 2022-2023 activity.
Links: https://www.cisa.gov/sites/default/files/2023-08/CSRB_Lapsus%24_508c.pdf
https://www.cisa.gov/sites/default/files/2023-11/aa23-320a_scattered_spider_0.pdf
I would also suggest these NCSC guides on incident management: https://www.ncsc.gov.uk/collection/incident-management
and effective cyber crisis comms: https://www.ncsc.gov.uk/guidance/effective-communications-in-a-cyber-incident
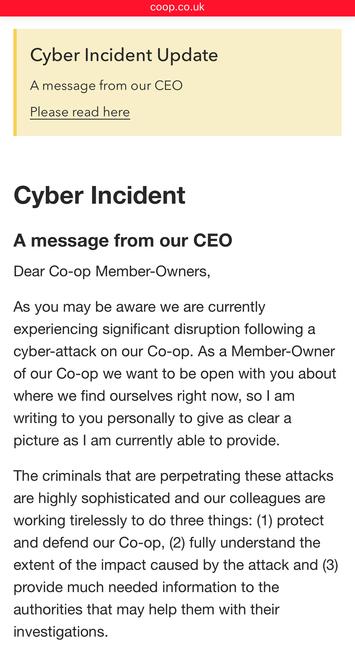
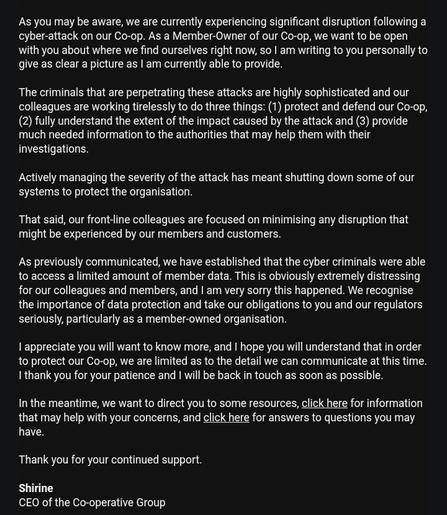
Co-op Group have now admitted a significant amount of member (customer) information has been stolen by DragonForce Ransomware Cartel, saying they "accessed data relating to a significant number of our current and past members" - around 20 million people. The Membership database, basically. That includes home addresses and phone numbers etc.
Up until now Co-op hadn't even used the words cyber or threat actor, referring to an "IT issue" and "third party" in comms.
New by me - breaking down the attacks on UK highstreet retailers
Regarding IOCs around the UK retailer activity - there’s loads doing the rounds, and they’re almost all not useful.
Eg hundreds of dynamic VPN IPs from 2022. If you google them you’ll find them on vendor blogs from years ago for Scattered Spider - people are recycling in panic and passing around in panic.
Don’t hunt on random IOCs. IP addresses change. Strengthen foundational controls. Review sign in logs for abnormal activity etc.
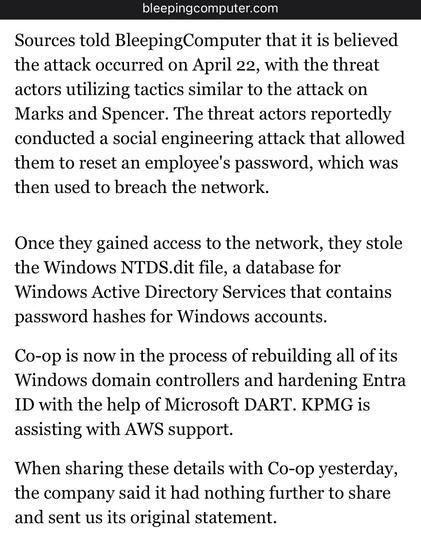
Bleeping Computer have more on the Co-op breach https://www.bleepingcomputer.com/news/security/co-op-confirms-data-theft-after-dragonforce-ransomware-claims-attack/
One of M&S’ biggest suppliers have said they have reverted to pen and paper for orders due to M&S lacking IT.
Additionally, M&S staff are raising concern about how they will be paid due to lack of IT systems.
M&S are over a week into a ransomware incident and still don’t have their online store working.
Here's the ITV News report anyhoo, logline: "ITV News understands the the ongoing cyberattack faced by the supermarket has worsened since Friday, impacting the ordering system, drivers and warehouse staff."
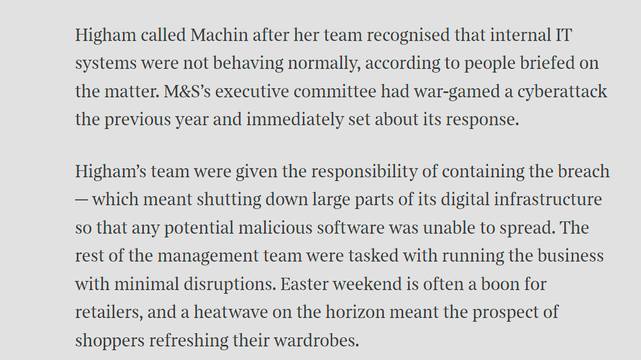
Sunday Times has a piece looking into ransomware incident at Marks and Spencer. It's pretty good, goes into their contain and eradicate focus.
"By shutting down parts of the IT estate, Higham’s team had worked to prevent the attack from spreading, but had also stopped parts of its digital operations from functioning. This was considered a worthy trade-off."
One error in the article - lack of recovery doesn't mean no ransomware paid. Paying is not quick restoration.
https://www.thetimes.com/business-money/companies/article/m-and-s-cyber-attack-ms-klrnxvwq6
Great NCSC piece by @ollie_whitehouse
I’d add - block by Entra policy specifically High risk logins (below is too FP prone), and SOC monitor them. SOC playbook = account probably compromised. How?
https://www.ncsc.gov.uk/blog-post/incidents-impacting-retailers
Sky News quote a source in M&S head office saying Marks and Spencer have no ransomware incident plan so they are making it up as they go along apparently, with staff sleeping in the office and communicating via WhatsApp.
M&S dispute this, saying they have robust business continuity plans.
Co-op Group appear to be trying to course correct with their cyber incident comms.
They’re calling it a cyber incident now, and have put a statement on the front page of their website, along with an FAQ. They haven’t yet emailed members (they should). Edit: they’ve started emailing members.
I got an email from the Co-op a couple of hours ago.
@catatonicprime @GossiTheDog we hang up on users that get aggressive, etc.
Lol who the fuck is gonna sit there and take shit from anyone?
@GossiTheDog While in #BandQ today, the staff said they'd been having "some IT Issues like M&S"
Not sure if this was the staff just making a parallel of "generic IT issues" or if there has been some incident they haven't admitted yet
An IT security guy at a place I once worked said the executives were the biggest security vulnerability the company had because they wanted what they wanted and didn't care much about security. I think that's what tool Maersk down a few years ago - some exec installed malware that spread to the entire network.
"they normally put big all caps bold red warning if the person is a VIP, eg C suite, so they get VIP service - ie anything goes."
@Greengordon @GossiTheDog I just make a point of getting them to agree to accepting the risk and acknowledging that the Board will get quarterly updates on who is accepting this sort of risk on behalf of the company. The answer isn't "no", and if you as the exec want to hide that you're doing this, you're already admitting that you know it's wrong.
Funny how much more they care about security when their bosses look over their shoulders.
@GossiTheDog This is basically the plan for most businesses in reality.
It's fine to talk about stuff being "widely known best practice," but when IT shows up with big expenses for backups and security, the MBA's always decide it's more important to rightsize the headcount and operate lean. Many IT departments report up through an MBA and not a technical person, and many IT people are terrible at communicating risk dramatically enough to get money.
@GossiTheDog The thing that gets me is that the two statements are probably true for the people who said them. The Security group may have wargamed and prepared for malware attacks, and done so in a way that no one else in the technical stack even noticed happening (beyond some new agent installs being requested). So when the attack comes, the Security plan swings into action and no one outside of Security knows what it is or has practiced it.
This is high visibility. Executives step in to make Declarations, complicating the response. This is an incident big enough to need sub-commands to track various workflows, reporting up to a rotating incident command. Everyone wants to help, the workflows aren't well defined yet, and people help on their own authority (thanks to Command not having a clear picture yet and guiding where help would be good) and maybe make things worse in a few spots.
We had a plan.
It is chaos.
Both are true.
@GossiTheDog @ollie_whitehouse
Do egress filtering (esp. for servers) with alerting.
If there is unknown communication, then you have either a misconfiguration or a problem.
Keep critical IT infrastructure (network, firewalls, SAN/NAS, virtualisation, backups) separated from Active Directory.
Do not couple internet-facing systems (including VPN and M365) with your local AD.
@GossiTheDog I agree with most of your arguments. (In fact, the only one I take exception with is comparing ransomware with climate change. Ransomware is a much more real and urgent problem.) Those are pretty much arguments I've used myself when advising customers hit by ransomware not to pay.
But, ultimately, it's the company's decision. Even if the company makes the wrong decision, the government shouldn't be the one who decides for them.
See also this:
"Decryption tools are worse than they’ve ever been."
The organizational structure of ransomware groups is evolving rapidly.
The Ransomware-as-a-service (RaaS) model has not recovered from law enforcement disruption, and the entrance of novice actors along with non-Russian state-linked cybercriminals has led to uncertain outcomes for victims.
"Travelex aren’t alone. When I covered the Capita ransomware, they paid quietly paid"
maybe delete one of the "paid"s
When the first indication appears, shut everything down. I have seen banks do this, and watched tellers calmly tell customers "I'm sorry, but the system is temporarily shut down" and start from there.
If the breach is stopped quickly enough, you may have a chance.
Also, what about off site storage, that would not be accessible to the attacker?
Ultimately, the decision is a risk management decision, to evaluate as quickly as you can

Inside the M&S meltdown: 3am meetings and £40m a week in lost sales — The Times and The Sunday Times
Stuart Machin had been looking forward to a long weekend. It was Easter Saturday and the chief executive of Marks & Spencer had retired to his south London home for the evening, after a long day inspecting the aisles of his local M&S branch — something of a Machin pastime. Suddenly, his phone flashed with a call from his head of digital and technology, Rachel Higham, telling him that M&S’s IT systems were not functioning as normal. Neither knew it for certain then, but M&S was under attack by
@GossiTheDog It's terrible advice for any major incident, ransomware or not!
Do these morons learn nothing from history?
@distinctdipole if there's one thing we can learn from history, it is that nobody ever learns anything from history.

@GossiTheDog UK cyber security at private firms tends to be very poor on average but social engineering remains the hacker's most effective tool.
Slack and Teams access in particular seems like a large attack vector. I believe the Twitter hack a few years back - when it was Twitter - was facillitated by superuser creds being pinned to a slack channel.









 🌬️
🌬️