\"/'
@semitones @dgar I once even encountered a website that accepted line breaks in the password.
I had typed the new password in a text file and had copy-paste-ed the whole line, including line break in the sign up form.
Later at the login form the same password (now without the line break) didn't work anymore.
Took me a minute or two to figure that out.
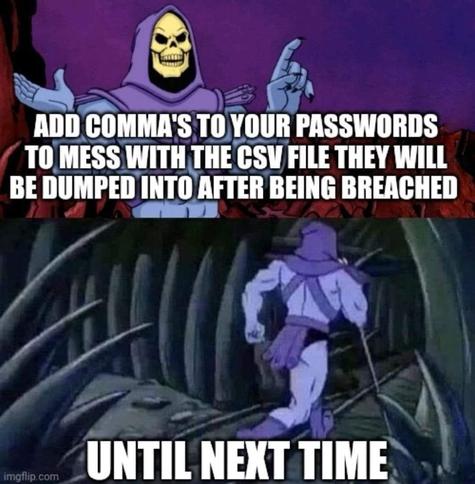
Malapostrophe alert!
Way back in time it also messed with you because the guy that wrote the login daemon didn't know what he was doing.
You might just luck out and take down a ransomware gang.
@dgar Proper CSV files have a solution to embedded commas.
Till next time! 🤓
@echedellelr
Only if you test if it works with every method you'll try to access, including password recovery.
Yes, I had problems as if the non-UTF-related password rules were different for account creation, login and recovery.
(Bonus points if you break the app at account creation.)
and from many other countries, like Brazil.
According to a Wikipedia article, semicolon is used by almost double the number of countries that use comma.
So, to include both characters is the best practice. 😁
_______
Please, what does "comma's" mean in the context?

@dgar
Use commas, multiple single quotes, and semicolons in odd non repeating patterns to really screw with parsing, be sure it also contains emojis if allowed, Unicode characters and write out Unicode such as the space ( )
All that along with the typical password security measures should fuck with exports, parsing and escaping just enough to get a malicious actor to at least toss your entry out.
You've done it right if you break the db and can't log in yourself lol.
If the information is being sold as a csv, it’s probably not the same person.
@dgar Standard CSV can handle commas in the field values: https://www.rfc-editor.org/rfc/rfc4180#page-2 (point 6).
But, I suppose that's not as funny/entertaining.
If you can, put double-quote characters in your passwords, too as they will help screw things up for non-standard CSV processors.

My password for every site is '; DROP TABLE USERS;
 OpenSoul
OpenSoul 
