https://old.reddit.com/r/pcmasterrace/comments/1sh4e5l/warning_hwmonitor_163_download_on_the_official/ #technews #cybersecurity #userawareness #HackerNews #ngated
https://old.reddit.com/r/pcmasterrace/comments/1sh4e5l/warning_hwmonitor_163_download_on_the_official/ #technews #cybersecurity #userawareness #HackerNews #ngated
⚠️Unbelievable! The most common passwords of 2025 are still “123456” and “password.” We’ve built smarter tech — but not smarter habits. 🔑🙈 #PasswordSecurity #UserAwareness
https://www.theregister.com/2025/11/06/most_common_passwords/
ClickFix attacks keep rising — exploiting trust, curiosity, and automation fatigue. Awareness is still the strongest patch. 🧠⚠️ #UserAwareness #PhishingDefense
https://thehackernews.com/2025/10/analysing-clickfix-3-reasons-why.html
Security problem of last decade: people dont update the software
Security problem of this decade: people autoupdate software
We have educated people we are again going to do that. What we are not going to do is fix the software environment. We can give 100 excuses of why it’s not possible but then when it comes to blaming ID01T we dont hesitate in putting user of gun point.
If software has an excuse of too complicated problem to solve, user has an excuse of too complicated toolset.
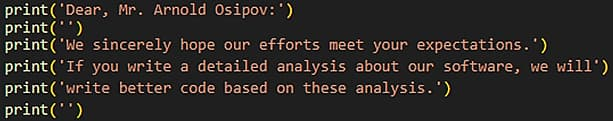
"⚠️ Chae$ 4.1: Taunting direct message to researchers at Morphisec within the source code. ⚠️"
The original Chae$ malware was identified in September 2023, and its latest version, dubbed Chae$ 4.1, employs advanced code polymorphism to bypass antivirus detection. It also includes a direct message to Morphisec researchers thanking them for their effort and hoping not to disappoint.
That's got to sting...
🛡️💻🔒
Source: Hackread by Deeba Ahmed
Tags: #CyberSecurity #MalwareAlert #Chae$Malware #Morphisec #AdvancedThreats #InfoSecCommunity #DriverScam #DataProtection #UserAwareness 🚨🌍💡
None of that helps us in security. Teach and positive reinforcement is way more effective in the long run.
Also, I bet that anyone and everyone who slams people for falling for a phish would fall for one. Why? We are human and can be gullible. ALL of us.
#infosec #phishing #userawareness
Y’all, make sure you’re educating your end users on the importance of burner phones! Protect your end users!
https://www.cnn.com/2023/05/09/us/utah-mom-childrens-book-husband-killing-cec/index.html
#swphl23 #infosec session on small teams...
Entry level is not 3 to 5 years of experience...
So many technology solutions that are procured to solve one problem. #techOverload. Instead, figure out how to use more of the tools you have already.
Never ending threats. Many focus on end users. #userawareness is needed.
Limited resources including people. Orgs need to realize they may need to train for experience instead of finding unicorns.
Lots of compliance requirements. Don't waste resources doing compliance if it's not required from outside motivations. Internal measures of program can do better to tell the story to mgmt. (Measure risks and mitigation instead.)
The 5 phases of the NIST CSF framework can be used to help define your program, but still use a business risk approach.
Swatting at flies is ineffective and inefficient.