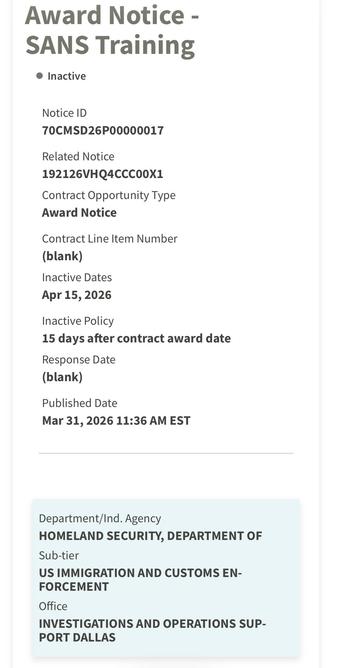
Ummm... Is SANS training ICE?
https://sam.gov/workspace/contract/opp/99f8bdc298c34f06bcac9bd7e39b1bca/view
Edit to add: SANS is training ICE how to pull information off of harddrives, etc.
FOR498: Digital Acquisition and Rapid Triage
"Course Overview:
A digital forensic acquisition training course, FOR498 provides the skills to identify the many and varied data storage mediums in use today, and how to collect and preserve this data in a forensically sound manner despite how and where it may be stored. This forensics data collection course covers digital acquisition from computers, portable devices, networks, and the cloud, and teaches rapid triage—the art and science of identifying and starting to extract actionable intelligence from a hard drive in 90 minutes or less."
This training will directly hurt people.
#sans #ice #infosec