All hail the Van Panther
Click on, "Show More" or "Read More" to get the links.
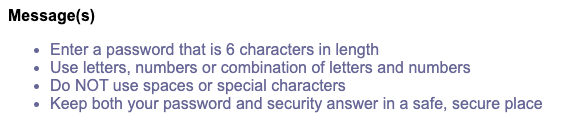
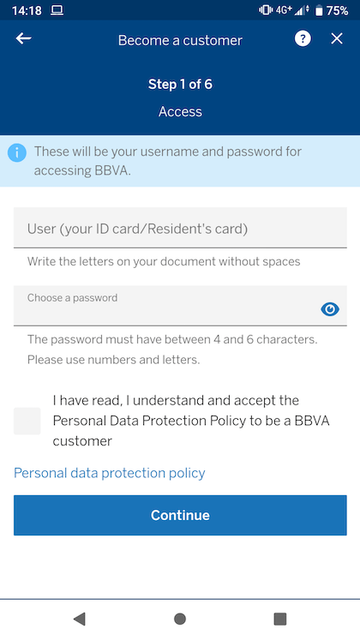
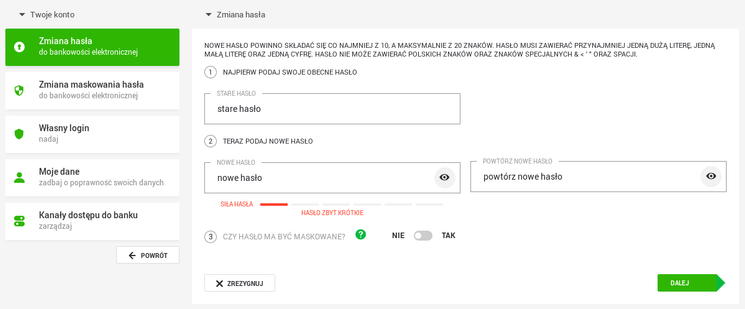
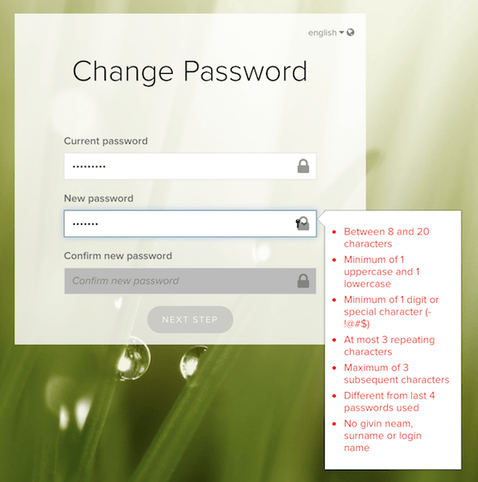
DESCRIPTION of the content found at the links, below - "Today we look at the problem Microsoft has with storing passwords in plain text in RAM."
==========
NOTE - This post is best viewed on a PC. Switched To Linux is, “written by a broad spectrum computer consultant to help people learn more about the Linux platform.” This account is a supporter of Switched To Linux and provides convenience posts of thumbnails art, videos and streams.
#SwitchedToLinux #Linux #Windows #Mac #Technology #Tech #AltTech #Privacy #Private #Security #Secure #FOSS #FreeAndOpenSource #FreeAndOpenSourceSoftware #FreeOpenSourceSoftware #YouTube #Odysee #Rumble #BitChute #Locals #Patreon #DLive #Twitch #AltTech #FactCheckTrue #Fediverse #SocialMedia #passwords #microsoft #edge
==========
After viewing the content located at the below links, Tell us what you think by filling out a "SATISFACTION SURVEY or ABUSE/SPAM REPORT" form from Teh AnKorage
https://cryptpad.disroot.org/form/#/2/form/view/elsOVQUrXAmGuer4kd75JhA3mNELuCj8cTjEUynrZZo/
\*Videos and podcasts may take a considerable amount of time to post. If it is not present, it will be, soon(tm).
MATRIX! Join our Matrix community where you can chat about Linux and general tech topics. Also, direct video links are provided for our Matrix community members! Don't miss out!
https://matrix.to/#/#switchedtolinux:matrix.org
#YouTube -
https://www.youtube.com/@SwitchedtoLinux/videos
#Odysee -
https://odysee.com/@switchedtolinux:0?view=content
#Rumble -
https://rumble.com/c/SwitchedToLinux/videos
#Bitchute -
https://www.bitchute.com/channel/uf9hzD216LX0
==========
Keep an eye out for a possible podcast!
PODCAST: https://podcast.switchedtolinux.com